-
-
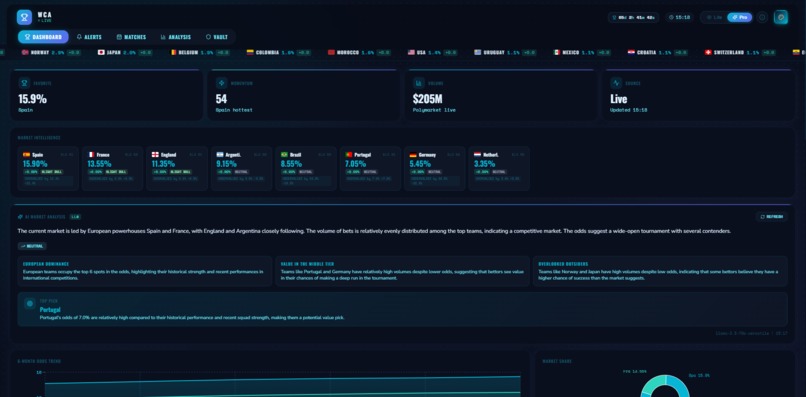
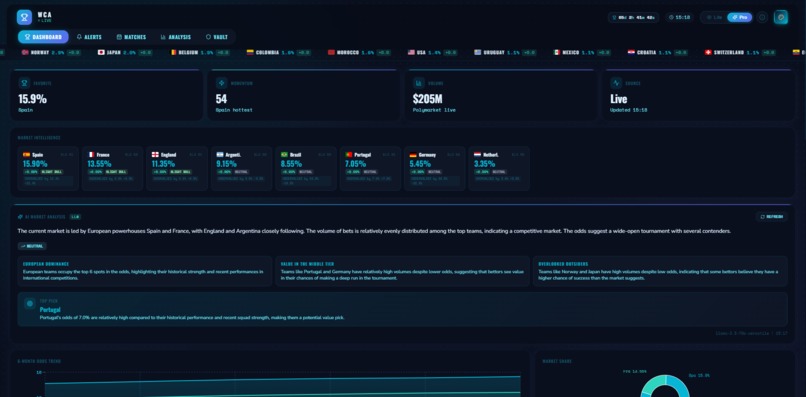
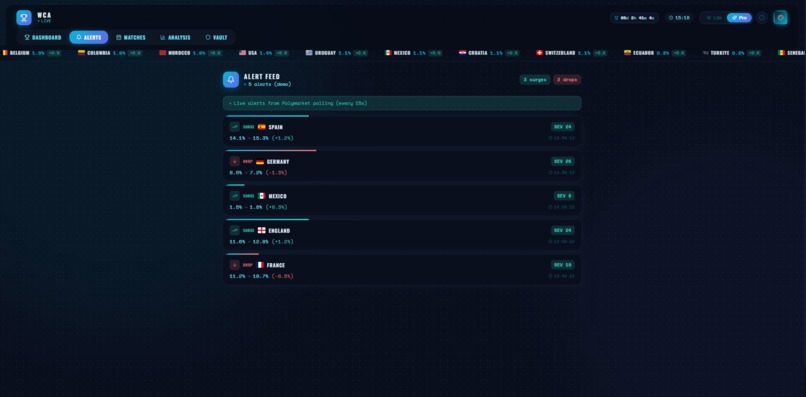
Live World Cup 2026 odds dashboard with AI-powered market analysis via Llama 3.3 70B — real-time data from Polymarket
-
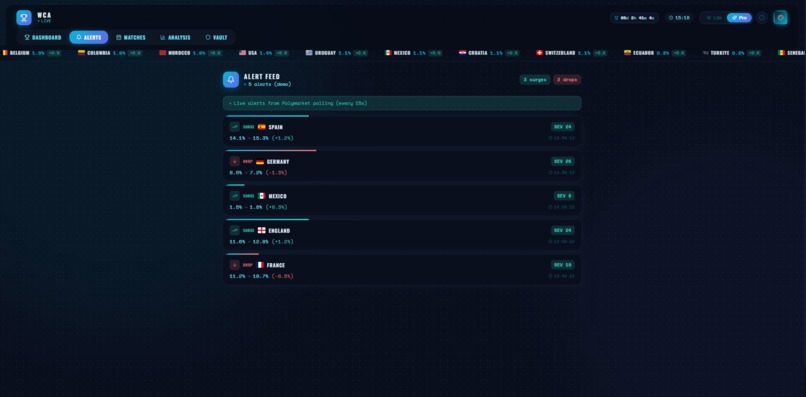
Smart alert feed detecting odds surges, drops, and volume anomalies with severity scores for 24+ teams
-

Match Center with head-to-head probability breakdowns showing home, draw, and away odds
-

Team comparison radar charts, head-to-head stats, and historical odds trends from Polymarket
-
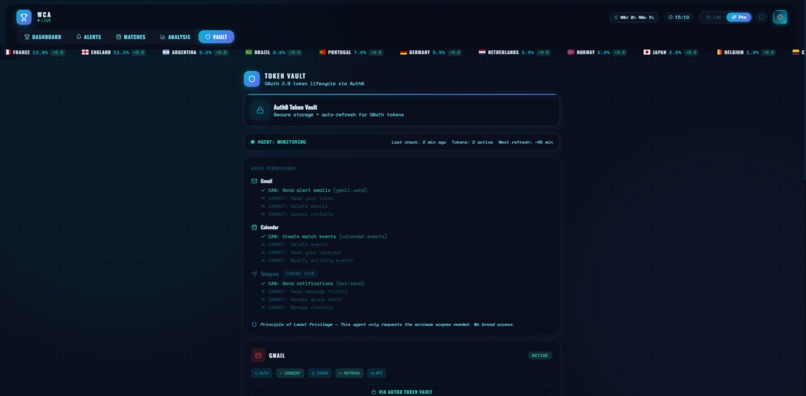
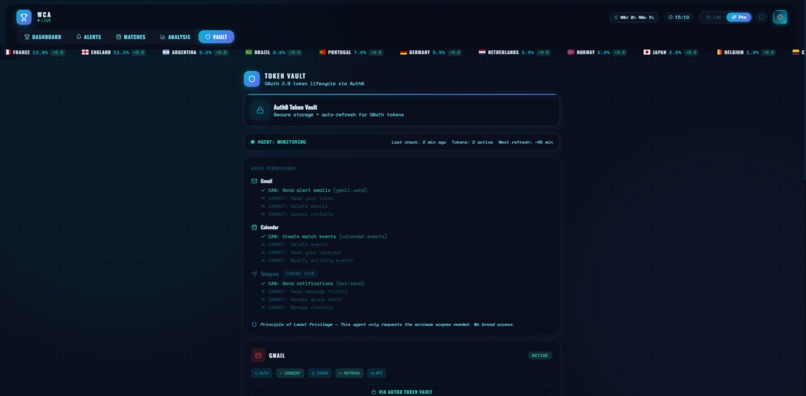
Auth0 Token Vault integration — connect Gmail and Calendar with minimum permissions and full transparency
Inspiration
The 2026 FIFA World Cup is generating massive betting activity on prediction markets like Polymarket, with over $196M in volume across 24+ teams. We saw an opportunity to build an AI agent that monitors these odds in real-time and acts on behalf of users — sending alerts through Gmail and Google Calendar — all secured through Auth0 Token Vault.
The key insight: users want autonomous agents that can interact with their digital services, but they need to stay in control. Auth0 Token Vault makes this possible by handling OAuth flows, token storage, and auto-refresh without the agent ever touching raw credentials.
What it does
WorldCup AI Agent is an autonomous monitoring agent that:
- Tracks live odds from Polymarket for 24+ World Cup 2026 teams, polling every 15 seconds
- Detects market movements using three signals: single-interval surges/drops, sustained velocity, and volume anomalies (z-score analysis)
- Generates AI-powered analysis using an LLM (Llama 3.3 70B via Groq) to provide natural language market summaries, key insights, and value picks
- Sends smart alerts via Gmail and Google Calendar using tokens stored securely in Auth0 Token Vault
- Shows transparent permissions — users can see exactly what the agent CAN and CANNOT do (e.g., "CAN: Send alert emails" / "CANNOT: Read your inbox")
How we built it
Architecture:
- Frontend: React 18 + Vite with 11 themes, 3 viewing modes (Lite/Pro/Learning), and PWA support
- Backend: Vercel Serverless Functions (Node.js) with scheduled cron jobs
- Database: Supabase (PostgreSQL) with Row Level Security
- Auth: Auth0 Token Vault for secure OAuth token storage and retrieval via Management API
- AI: Groq API (Llama 3.3 70B) for market analysis — completely free
- Data: Polymarket Gamma API for real-time odds
Token Vault Flow:
- User clicks "Connect Gmail" on the Vault page
- Frontend calls our /api/connectService endpoint which generates an Auth0 authorization URL
- User is redirected to Auth0, then to Google OAuth consent screen
- User grants gmail.send and calendar.events scopes (minimum permissions only)
- Auth0 Token Vault stores the OAuth token securely and handles auto-refresh
- When the cron job detects a significant market movement, it calls Auth0's Management API to retrieve the token
- The agent uses the token to send an alert email via Gmail API, then discards it
Total deployment cost: $0 — all services running on free tiers (Vercel, Supabase, Auth0, Groq).
Challenges we ran into
- Token Vault integration: Understanding the Management API auth flow and M2M application setup took significant exploration. Getting the client credentials grant, Management API token, and user identity token retrieval all working together required careful sequencing.
- Real-time data accuracy: Polymarket's API returns raw probabilities that needed normalization and edge-case handling for teams with very low odds.
- Alert detection tuning: Balancing sensitivity (catching real movements) vs noise (avoiding false alerts) required implementing three complementary detection signals: single-interval changes, velocity over multiple snapshots, and volume anomaly detection using z-scores.
- Credential security: We had to migrate to a completely new repository after discovering hardcoded secrets in the original codebase, implementing proper environment variable management across frontend (VITE_ prefix) and backend.
Accomplishments that we're proud of
- Real Token Vault implementation — not a mock. Tokens are stored in Auth0's infrastructure, retrieved via the Management API, and used to call Gmail and Calendar APIs. We tested this live: emails arrive in the inbox, calendar events appear in Google Calendar.
- Principle of Least Privilege — the agent requests only gmail.send and calendar.events scopes. It cannot read emails, delete events, or access contacts.
- Transparent permissions dashboard — the Vault page shows users exactly what the agent can and cannot do for each connected service, building trust through transparency.
- AI-powered analysis — an LLM (Llama 3.3 70B via Groq) generates natural language insights about market movements, making the agent truly intelligent rather than just rule-based.
- Zero-cost architecture — the entire application runs on free tiers: Vercel (hosting + serverless), Supabase (database), Auth0 (authentication), and Groq (AI inference).
What we learned
- Auth0 Token Vault is a powerful abstraction for agent-to-service authentication. The auto-refresh mechanism means agents can operate continuously without manual intervention or complex token lifecycle management.
- The Permission Dashboard pattern (showing explicit CAN/CANNOT lists) is essential for building user trust in autonomous agents.
- Combining rule-based detection with LLM-powered analysis creates a more useful agent than either approach alone. The rules catch the movements; the AI explains what they mean.
- Setting up M2M applications in Auth0 with the correct scopes (read:users, read:user_idp_tokens) is essential for Token Vault to work in a serverless backend.
What's next for WorldCup AI Agent
- Multi-user support with individual Token Vault connections per user
- Real step-up authentication using Auth0's acr_values for high-stakes actions
- More prediction markets beyond World Cup — elections, crypto, sports leagues
- Custom alert rules where users define their own thresholds and conditions
- Additional notification channels including Telegram and mobile push notifications
Bonus Blog Post: Building Secure AI Agents with Auth0 Token Vault
The Problem: Agents Need Access, Users Need Control
AI agents are becoming more capable every day, but there's a fundamental tension: to be useful, agents need access to user services (email, calendar, messaging). But giving an autonomous program access to your Gmail is terrifying — unless there's a robust security layer in between.
This is exactly what Auth0 Token Vault solves, and building WorldCup AI Agent taught us valuable lessons about how to use it effectively.
What is Token Vault?
Token Vault is part of Auth0 for AI Agents. Instead of your application storing OAuth tokens (with all the security risks that entails), Auth0 stores them in its own secure infrastructure. Your agent retrieves tokens on-demand via the Management API, and Auth0 handles refresh automatically.
Key Lessons from Building with Token Vault
1. Tokens never touch your infrastructure. Our Vercel serverless functions never store Gmail tokens. They request them from Auth0, use them for a single API call, and discard them. If our server is compromised, there are no tokens to steal.
2. Auto-refresh is invisible. OAuth tokens expire — usually after an hour. With Token Vault, Auth0 handles refresh transparently. Our cron job runs daily at 9am UTC, and the token is always fresh. We wrote zero refresh logic.
3. Principle of Least Privilege is enforced at the OAuth level. We request only gmail.send (not gmail.readonly or full Gmail access) and calendar.events (not full calendar access). The scopes are defined once in the Auth0 connection configuration.
4. The M2M flow requires careful setup. To retrieve a user's token, your backend needs a Management API token obtained via client credentials grant. This means setting up an M2M application in Auth0 with the right permissions (read:users, read:user_idp_tokens). Getting this chain right was the trickiest part.
Architecture Pattern: The Monitoring Agent
Our architecture follows a pattern we believe will become common for AI agents:
[Data Source] --> [Detection Engine] --> [Token Vault] --> [User Services] Polymarket Cron + Rules + AI Auth0 Gmail/Calendar
The agent operates autonomously: it fetches data, analyzes it (using both rules and an LLM), and when it detects something significant, it retrieves the user's OAuth token from Token Vault and sends an alert. The user stays in control through the Vault page.
The Trust Pattern: CAN/CANNOT Lists
The most impactful feature we built wasn't technical — it was the Permission Dashboard. Showing users exactly what the agent CAN do ("Send alert emails via gmail.send") alongside what it CANNOT do ("Read your inbox", "Delete emails", "Access contacts") dramatically increases willingness to grant access.
This pattern should be standard for any agent that uses Token Vault. Users shouldn't have to read OAuth scope documentation to understand what they're authorizing.
What Token Vault Means for the Future of AI Agents
As AI agents become more autonomous, the need for secure, user-controlled credential management will only grow. Token Vault provides the infrastructure layer that makes this possible:
- Agents can act on behalf of users without ever seeing their credentials
- Users can revoke access at any time through a single disconnect action
- Developers can focus on agent logic instead of OAuth complexity
Auth0 Token Vault removes the hardest part of building secure AI agents: credential management. The future of AI agents is autonomous but accountable. Token Vault is the infrastructure that makes that possible.
Built With
- auth0
- groq
- javascript
- llama-3.3
- node.js
- polymarket-api
- postgresql
- pwa
- react
- supabase
- token-vault
- vercel
- vite


Log in or sign up for Devpost to join the conversation.