-

App Icon
-

Launch Screen
-

Home Screen of John
-
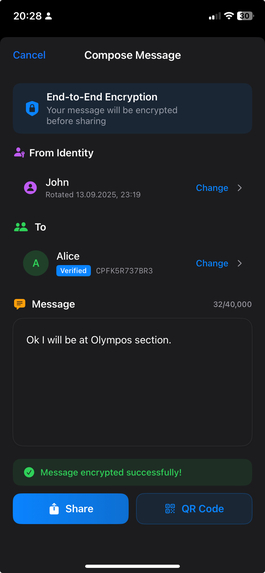
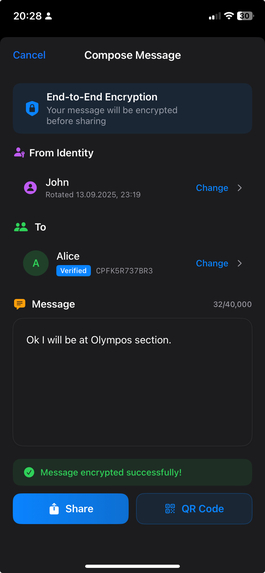
John enters a message and encrypts it
-

John shares the encrypted message in QR Code format
-
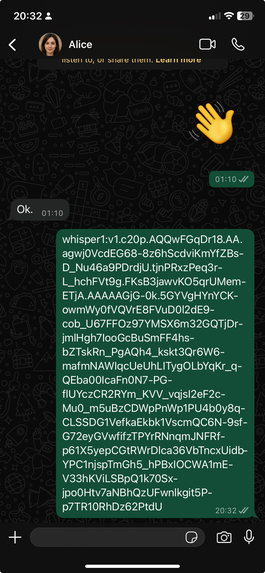
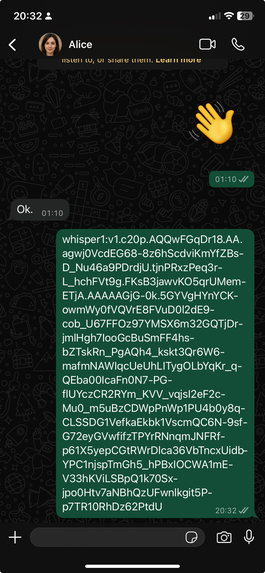
John sends the QR Code to Alice via Whatsapp in text format
-
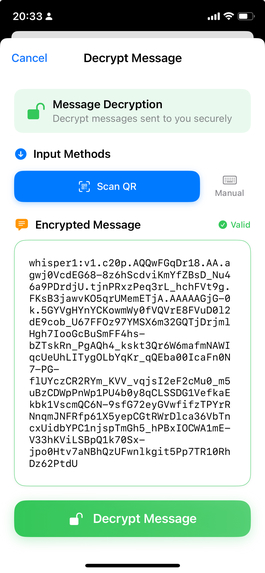
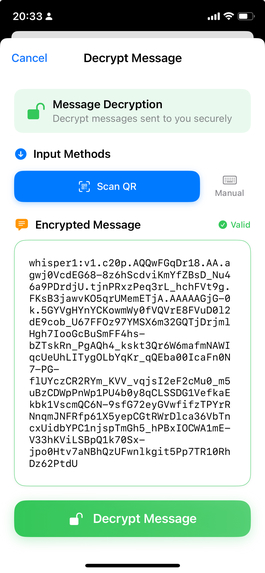
Alice scans the QR code or copy and paste the text from Whatsapp that includes encrypted message
-
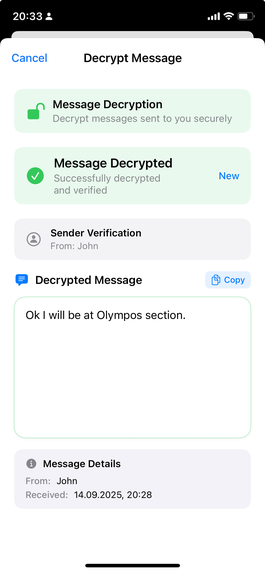
Alice decrypts the message successfully.
-
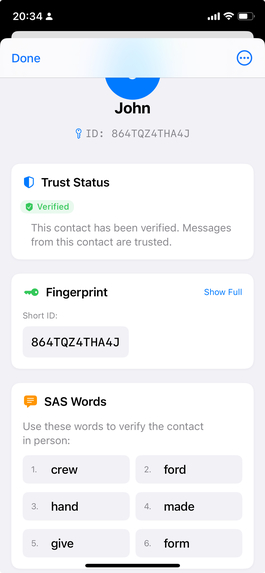
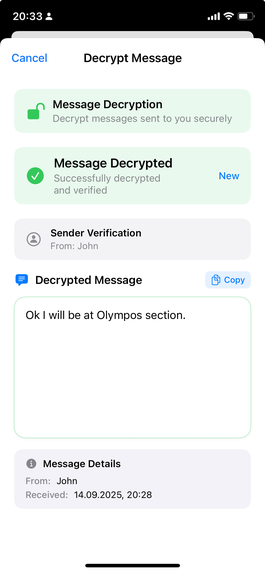
The detail identity view of John enlisted in Contacts List of Alice
-
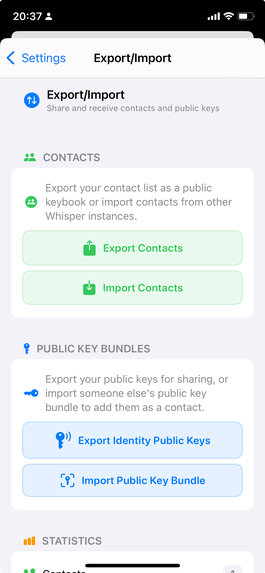
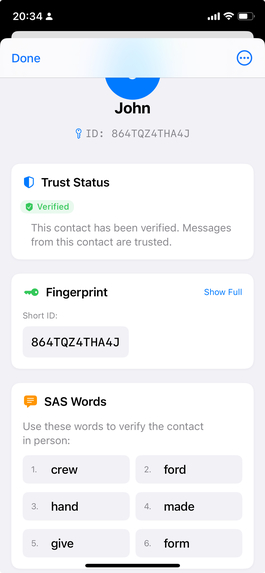
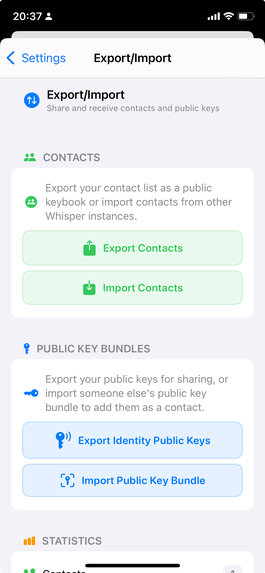
Export/Import Contacts screen
-
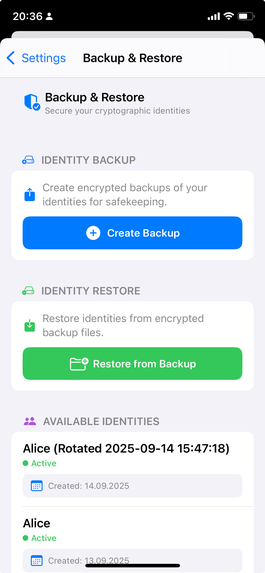
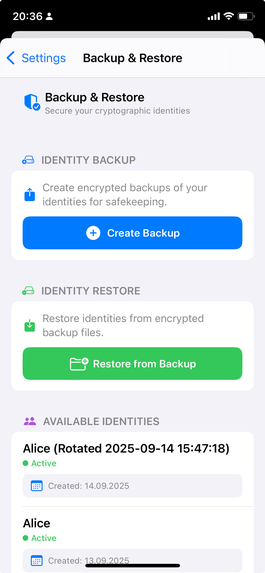
Backup/Restore Identities screen
-
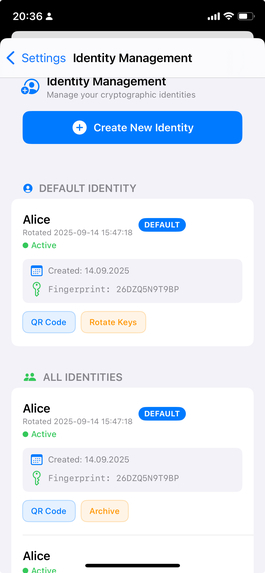
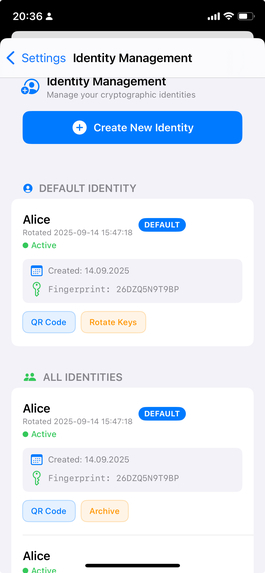
Identity management screen depicts Alice's current identities
-
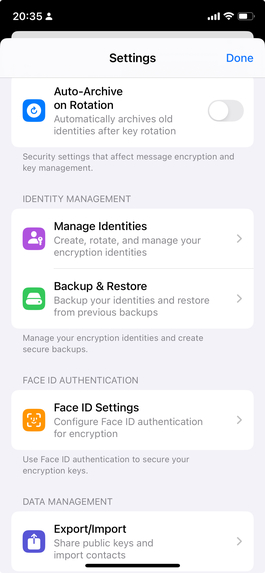
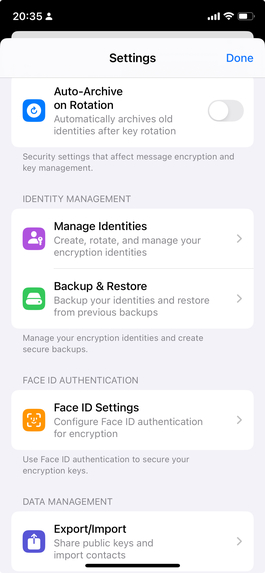
Settings Screen
-
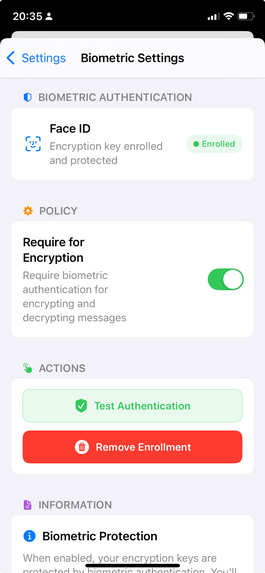
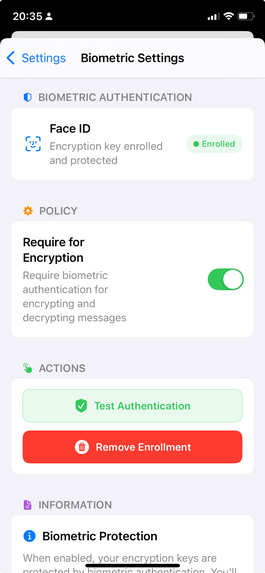
Face ID Settings Screen
Inspiration
While working in my current role, I encountered numerous incidents related to mobile device security—particularly on iPhones. I noticed that WhatsApp was often at the center of these issues, raising concerns about how it handles user privacy. International reports confirmed these fears, revealing cases where iOS devices were hacked through WhatsApp vulnerabilities.
This sparked a question in my mind: Could we create a way to send encrypted messages through insecure platforms like WhatsApp—without compromising privacy? I envisioned an app where user identities are verified and stored only on the device, enabling communication solely between trusted contacts.
From that idea, Whisper was born—a peer-to-peer, fully offline encryption tool that empowers users to communicate securely, even through traditional messaging platforms.
What it does
Whisper is a revolutionary serverless, peer-to-peer encryption app that brings military-grade security to everyday communication. Unlike traditional messaging apps that rely on servers and trust third parties with your data, Whisper operates entirely offline on your device, ensuring your messages remain truly private.
Core Functionality:
- Encrypt messages locally using industry-standard cryptographic algorithms (Curve25519, ChaCha20-Poly1305, BLAKE2s)
- Share encrypted content via QR codes through any messaging platform (WhatsApp, email, etc.)
- Decrypt messages received from verified contacts with biometric authentication
- Manage multiple cryptographic identities with automatic key rotation
- Verify contact authenticity through Short Authentication String (SAS) verification
- Zero network connectivity - your data never leaves your device unencrypted
Key Innovation: Whisper transforms any messaging platform into a secure communication channel without requiring the recipient to use the same app or service.
How we built it
Technical Architecture
Built entirely in Swift/SwiftUI for iOS 15+, Whisper implements a sophisticated layered architecture:
User Interface (SwiftUI) → Application Services → Security & Policy Layer →
Cryptographic Core (CryptoKit) → Data Persistence (Core Data + Keychain)
Cryptographic Implementation
- Curve25519 ECDH for key agreement with perfect forward secrecy
- ChaCha20-Poly1305 AEAD for authenticated encryption
- BLAKE2s/SHA-256 for cryptographic hashing and key derivation
- Ed25519 for digital signatures with biometric protection
- HKDF-SHA256 for secure key derivation with context binding
Security Features
- Envelope Protocol: Custom "whisper1:" format with Base64URL encoding
- Message Padding: Traffic analysis resistance with constant-time validation
- Replay Protection: 30-day cache with atomic check-and-commit operations
- Freshness Validation: ±48 hour timestamp window
- Policy Engine: Configurable security policies (contact verification, signature requirements, biometric gating)
Development Process
Implemented through 20 comprehensive tasks covering:
- Core encryption system with CryptoKit integration
- Multiple identity management with secure key storage
- Contact management with trust verification
- Security policy enforcement
- Biometric authentication integration
- Message padding and replay protection
- QR code workflow implementation
- User interface and accessibility
- Performance optimization
- Comprehensive security testing
Challenges we ran into
1. Cryptographic Complexity
Implementing military-grade cryptography correctly is notoriously difficult. We faced challenges with:
- Key derivation context binding - ensuring each message has unique cryptographic context
- Constant-time operations - preventing timing attacks in padding validation
- Secure memory management - properly zeroizing ephemeral keys and sensitive data
- Algorithm lock enforcement - preventing downgrade attacks while maintaining flexibility
Solution: Extensive security testing with timing analysis, memory validation, and comprehensive test vectors.
2. iOS Keychain Integration
Securely storing cryptographic keys while supporting biometric authentication required deep iOS security knowledge:
- Access control policies - balancing security with usability
- Biometric enrollment changes - handling Face ID/Touch ID updates
- Device-only storage - ensuring keys never leave the device
- Secure Enclave integration - leveraging hardware security features
Solution: Implemented layered security with fallback mechanisms and comprehensive error handling.
3. Network Isolation Enforcement
Ensuring zero network connectivity required innovative build-time validation:
- Symbol detection - scanning binaries for forbidden networking APIs
- Build-time enforcement - failing builds if networking code is detected
- Comprehensive coverage - detecting URLSession, Network framework, sockets, etc.
Solution: Created Python-based build script that analyzes source code and compiled binaries.
4. Performance vs Security Balance
Cryptographic operations are computationally expensive, especially on mobile devices:
- Background processing - keeping UI responsive during encryption
- Memory optimization - managing crypto buffers efficiently
- Battery impact - minimizing power consumption
- Lazy loading - optimizing identity and contact management
Solution: Implemented priority-based background processing with memory pools and intelligent caching.
5. User Experience Complexity
Making advanced cryptography accessible to everyday users:
- Key verification workflow - simplifying SAS word verification
- Trust management - clearly communicating security states
- Error handling - providing helpful feedback without revealing sensitive information
- Accessibility - supporting VoiceOver and Dynamic Type
Solution: Extensive UX testing with clear visual indicators and comprehensive accessibility support.
Accomplishments that we're proud of
🔐 Security Excellence
- Zero network policy - Completely offline operation with build-time enforcement
- Military-grade cryptography - Same algorithms used by Signal Protocol
- Perfect forward secrecy - Compromised keys cannot decrypt past messages
- Comprehensive security testing - 32 validation tests covering all attack vectors
🏗️ Technical Innovation
- Custom envelope protocol - Efficient, secure message format
- Atomic replay protection - Prevents message replay attacks
- Context-bound encryption - Each message cryptographically tied to its context
- Constant-time operations - Resistant to timing attacks
📱 iOS Integration Excellence
- Biometric authentication - Seamless Face ID/Touch ID integration
- Keychain security - Proper use of iOS hardware security features
- Accessibility compliance - Full VoiceOver and Dynamic Type support
- Performance optimization - Background processing with memory efficiency
🧪 Comprehensive Testing
- 151+ localization strings - Complete internationalization support
- Performance benchmarks - Detailed crypto operation analysis
- Security validation - Automated testing of all security requirements
- Accessibility testing - WCAG 2.1 AA compliance
📚 Documentation Excellence
- Complete specifications - Detailed requirements and design documents
- Implementation summaries - 20 task completion reports
- Security analysis - Comprehensive threat model and mitigation strategies
- App Store compliance - Ready for production deployment
What we learned
Cryptographic Engineering
- The critical importance of context binding in preventing cryptographic attacks
- How constant-time operations are essential for preventing side-channel attacks
- The complexity of key lifecycle management in production systems
- Why algorithm agility can be a security vulnerability
iOS Security Architecture
- Deep understanding of iOS Keychain access control policies
- How to properly integrate biometric authentication with cryptographic operations
- The importance of Secure Enclave for hardware-backed key storage
- Best practices for secure memory management in Swift
Mobile App Security
- How to implement network isolation at the build level
- The challenges of offline-first application architecture
- Balancing security and usability in cryptographic applications
- The importance of comprehensive error handling without information leakage
Software Engineering
- The value of specification-driven development for complex security projects
- How comprehensive testing is essential for cryptographic software
- The importance of accessibility in security-focused applications
- Why performance optimization matters for cryptographic operations
User Experience Design
- How to make complex cryptography accessible to everyday users
- The importance of clear trust indicators in security applications
- Why progressive disclosure works well for advanced security features
- How visual feedback helps users understand cryptographic operations
What's next for Whisper
Immediate Goals (Next 3 months)
- App Store submission - Complete Apple review process and launch
- Security audit - Professional third-party security assessment
- User testing - Beta testing with privacy-focused user groups
- Performance optimization - Further improvements based on real-world usage
Short-term Enhancements (6 months)
- Multi-language support - Localization for major world languages
- iPad optimization - Enhanced UI for larger screens
- Advanced key management - Hardware security key integration
- Group messaging - Secure multi-party communication
Medium-term Vision (1 year)
- Cross-platform support - Android version with protocol compatibility
- Enterprise features - Organization-wide key management
- Advanced verification - Integration with external identity verification
- Quantum-resistant algorithms - Future-proofing against quantum computers
Long-term Impact
- Open source release - Making the protocol and implementation publicly auditable
- Academic collaboration - Working with cryptography researchers
- Standards contribution - Contributing to secure messaging standards
- Privacy advocacy - Promoting user privacy rights and education
Technical Roadmap
- Protocol evolution - Versioned protocol with backward compatibility
- Performance scaling - Optimizations for larger contact lists and message volumes
- Advanced policies - More granular security policy controls
- Integration APIs - Secure integration with other privacy-focused applications
Whisper represents a new paradigm in secure communication - proving that military-grade security can be both user-friendly and completely private. By eliminating servers and network dependencies, we've created a truly sovereign communication tool that puts users in complete control of their privacy.






Log in or sign up for Devpost to join the conversation.