-
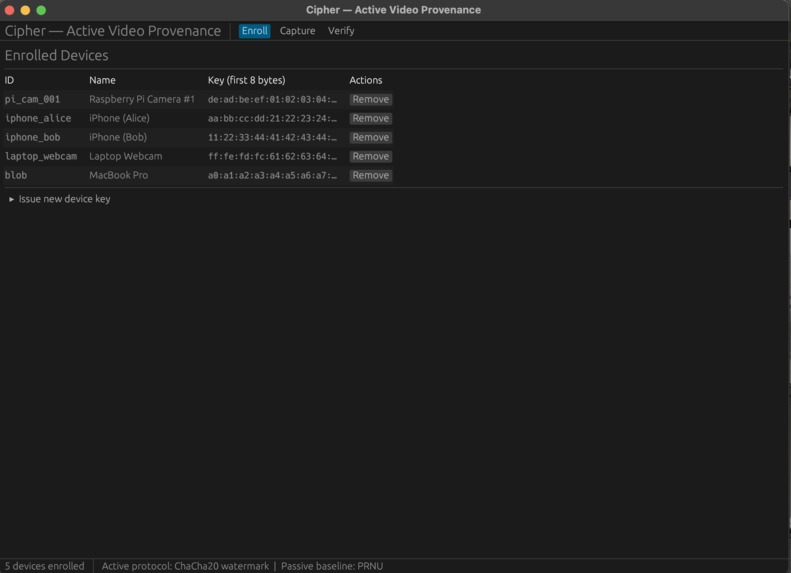
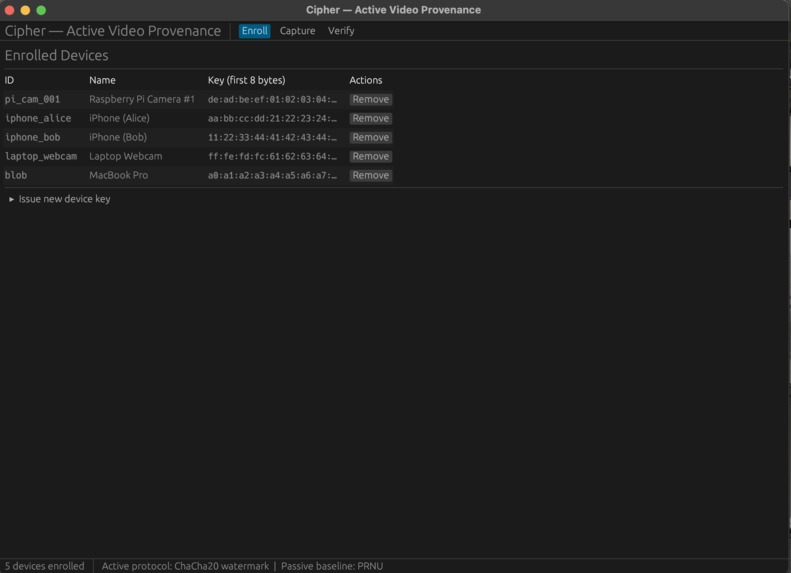
List of Devices that have been registered under the protocol are stored offline in a json structure along with their key values.
-
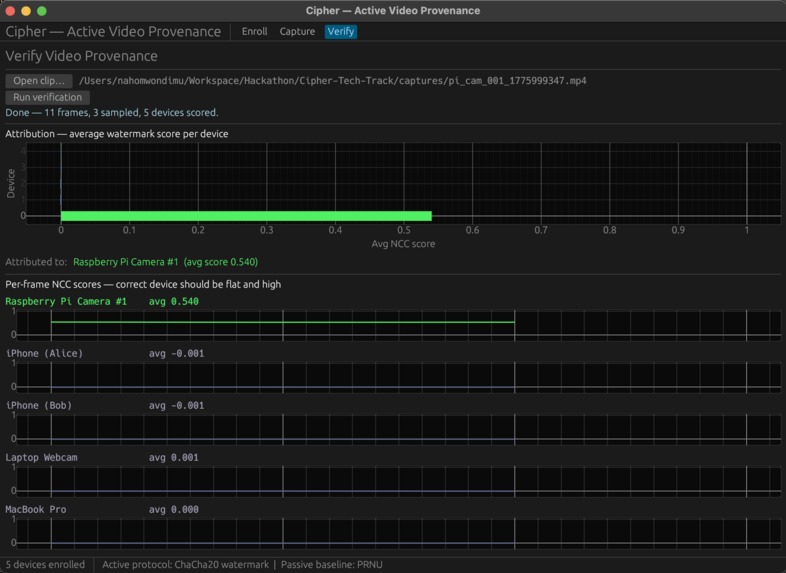
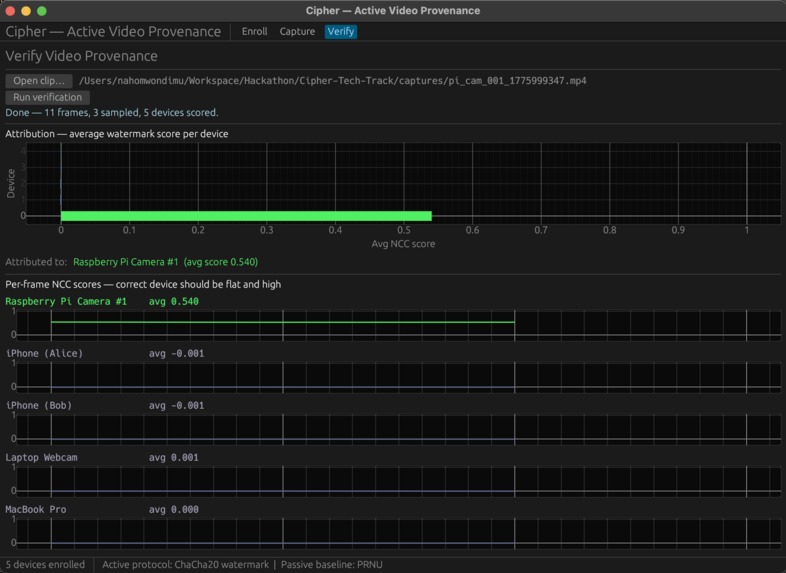
Results displayed are coming from the short clip of the chair taken in the last image. Results give input camera information.
-
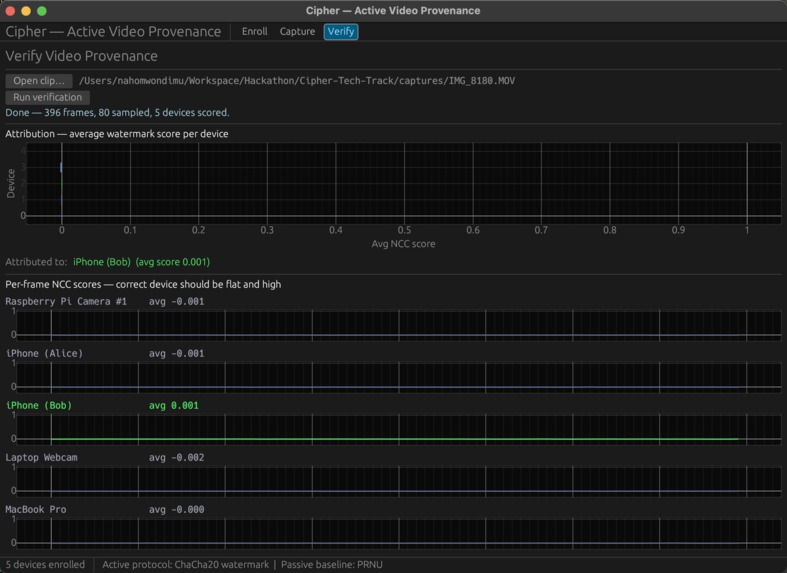
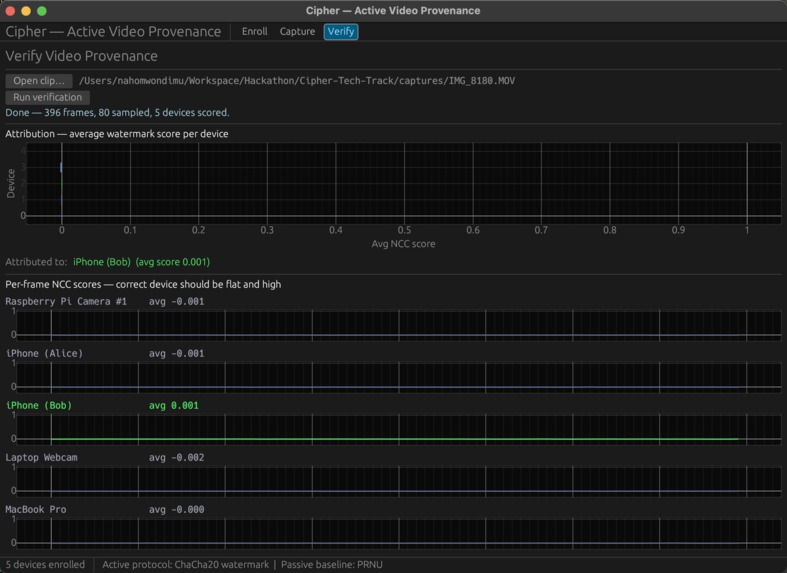
clean (non-registered) file analysis leads to blank and empty results.
-
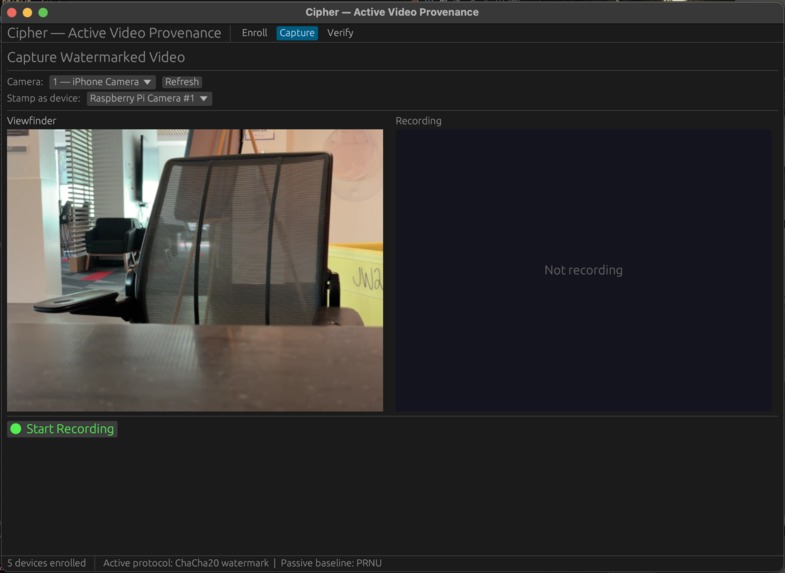
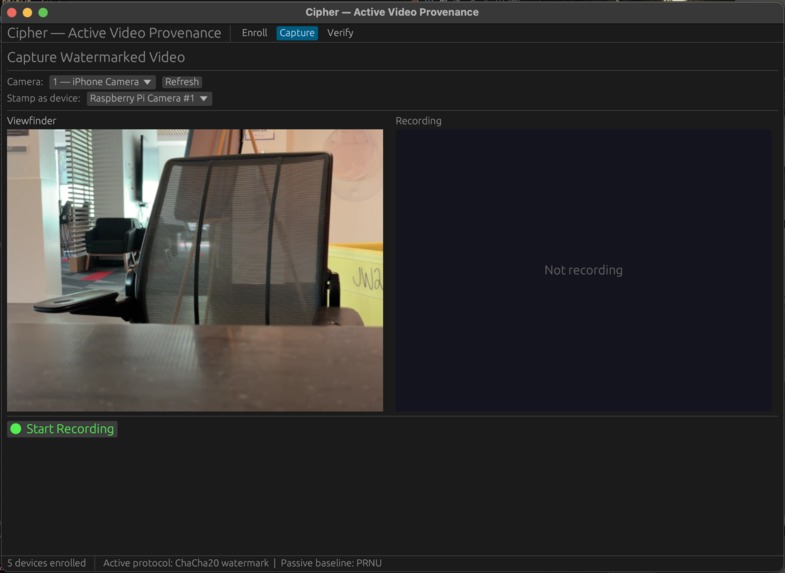
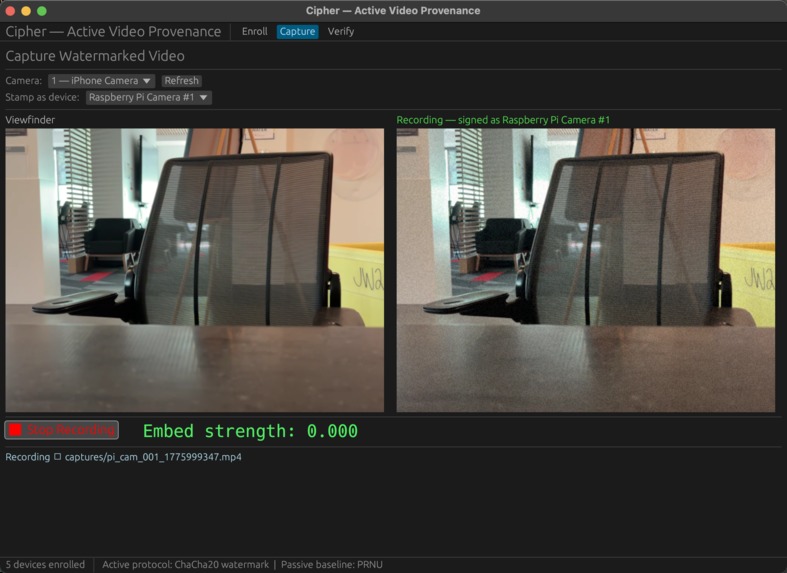
Capture tab displays the input from different camera sources.
-
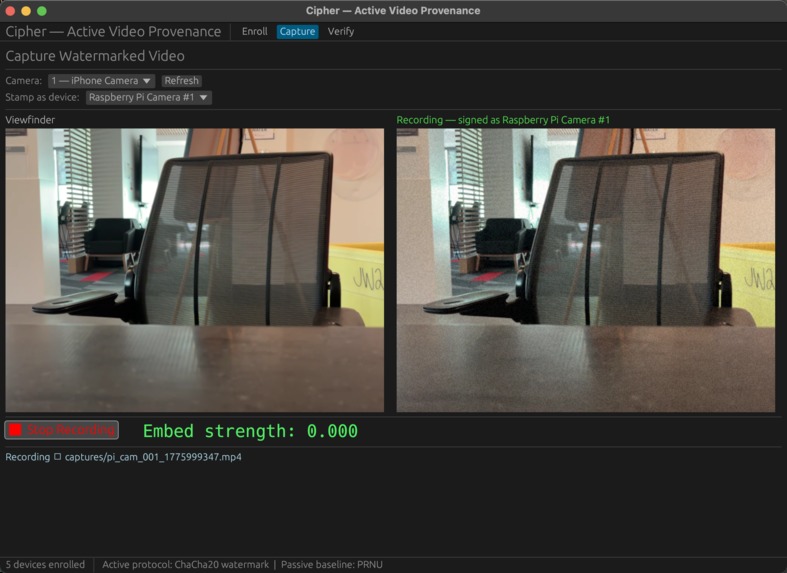
When you start recording, Second display panel lights up to show embedding and Embed Score increases the more time you give it.
Cameras that sign their own footage
Inspiration
In 2017, NSA contractor Reality Winner was arrested within 72 hours of leaking a classified document. The FBI didn't need network logs. Every color laser printer secretly embeds tiny yellow dots on each page, encoding its serial number and a timestamp. The NSA had the decoding table. Game over.
That tech has been in every office printer for 20+ years, but it's covert, proprietary, and only works on paper. We wanted the video version: overt, open, and built for the medium people actually care about now.
What we built
A Rust desktop app that stamps a cryptographic watermark into webcam footage as it's being recorded. No post-processing step. The file hits the disk already signed. Drop any clip into the Verify tab and it scores every frame against every enrolled device, showing both a bar chart of the best match and a sparkline across time.
The per-frame scoring gives us something we didn't expect: tamper localization. Splice foreign content into a watermarked clip and the sparkline shows a clean dropout at the exact frames that were inserted. The system doesn't just tell you who shot a clip. It tells you which parts of it are real.
How it works
Each device has a secret key that seeds a pseudorandom pattern of +1s and −1s, one per pixel. We add that pattern (scaled way down, invisible to the eye) onto every frame. To verify, we pull the high-frequency noise out of a suspect clip and check for a match. Correct device: clear signal. Any other device: noise. Unwatermarked clip: the system honestly reports "unknown" instead of guessing.
It's classical spread-spectrum watermarking, the same math that hides signals in streaming audio, adapted for real-time video.
Stack
Rust end to end. egui for the GUI, nokhwa for the webcam, ffmpeg subprocess for H.264. One binary, no cloud, multi-threaded so the UI stays smooth while encoding.
What surprised us
Real-time embedding takes under a millisecond per frame. We thought it'd be the bottleneck; it isn't even close. The signal survives aggressive recompression because the watermark is spread across every pixel, so noise cancels while signal accumulates. And per-frame scoring, which was a 30-minute code change, completely transformed what the system can do.
What's next
Deploying the signing logic inside camera hardware. A real PKI for device keys. Re-signing protocols for legitimate editors. And adversarial testing against attacks specifically designed to strip the watermark.
Built With
- eframe
- egui
- rust
Log in or sign up for Devpost to join the conversation.