-
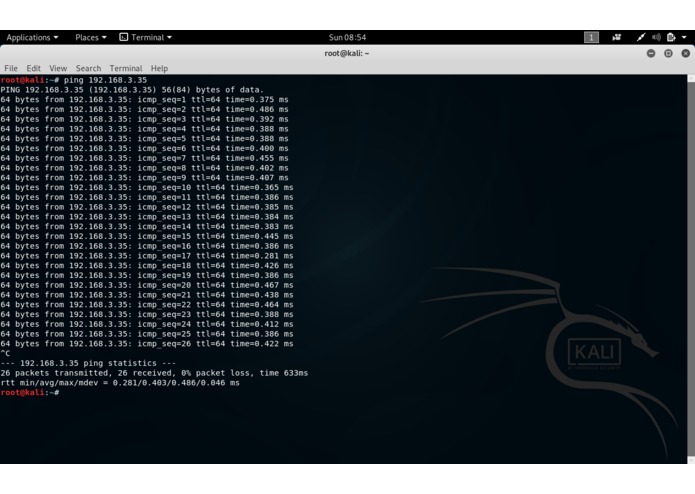
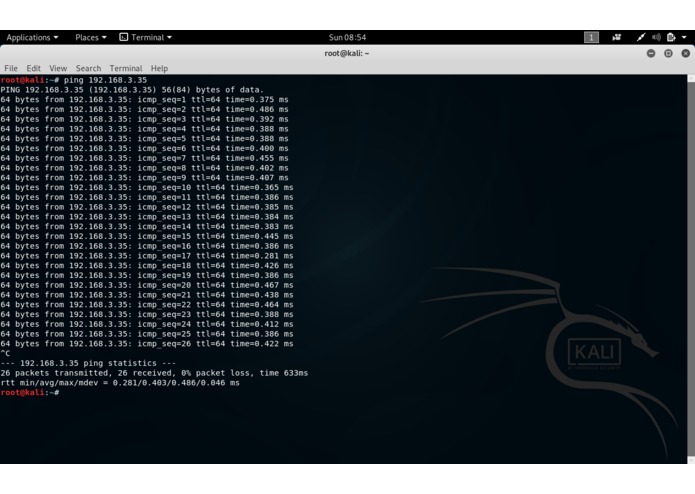
Ping on the Attacker Box
-
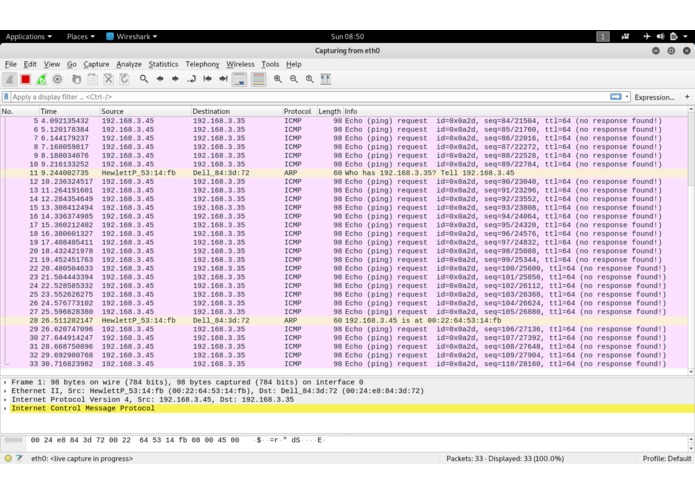
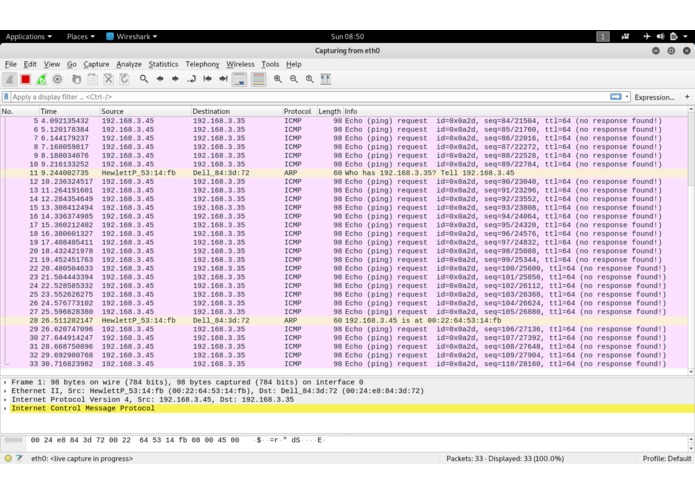
Pinging traffic in Wireshark
-
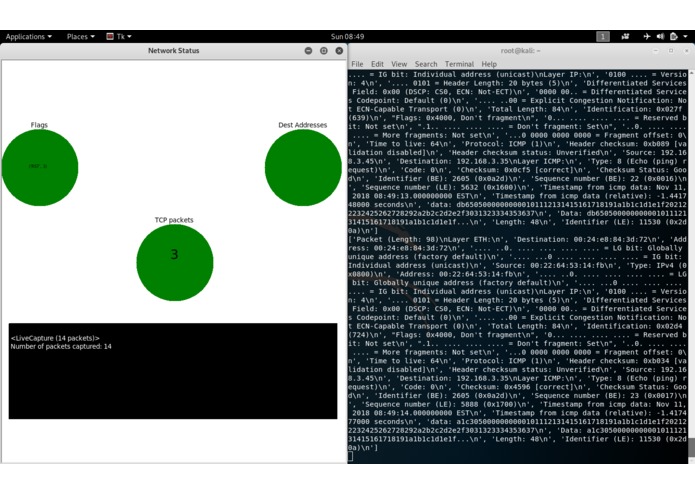
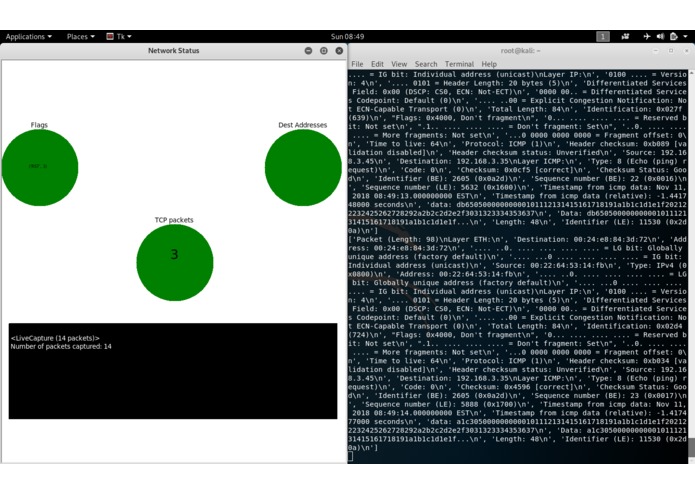
Pinging traffic in our IDS
-
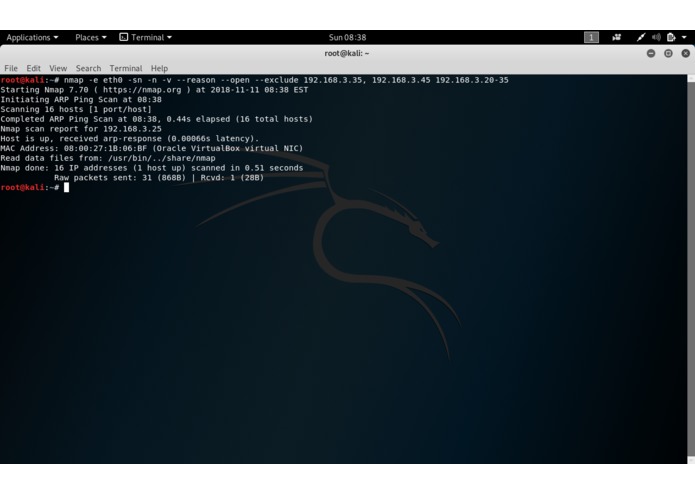
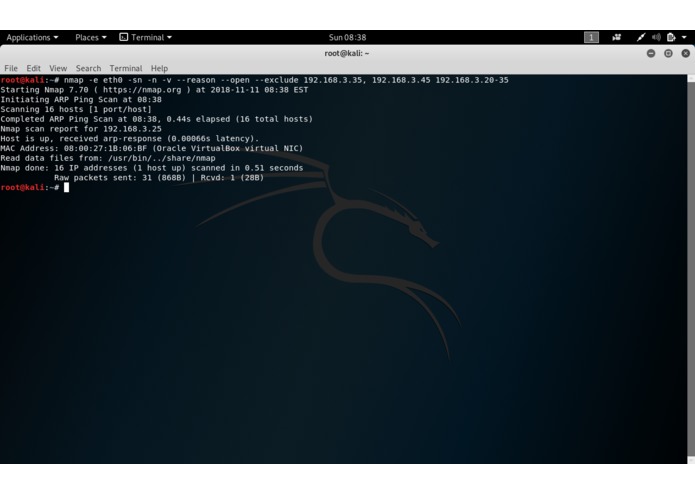
Host Scan on the Attacker Box
-
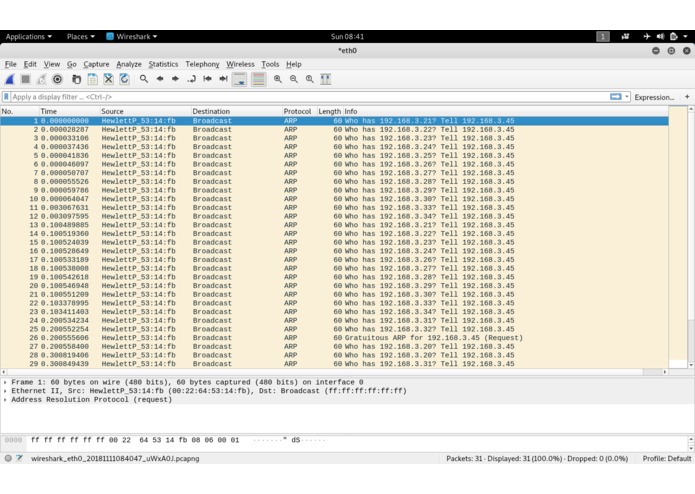
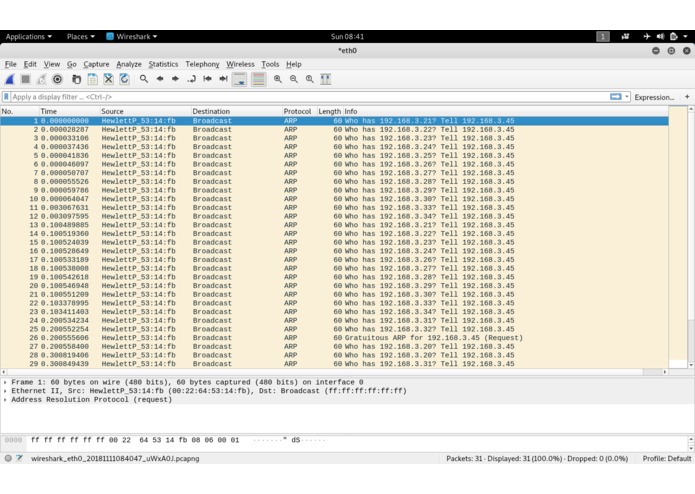
Host Scan traffic in Wireshark
-
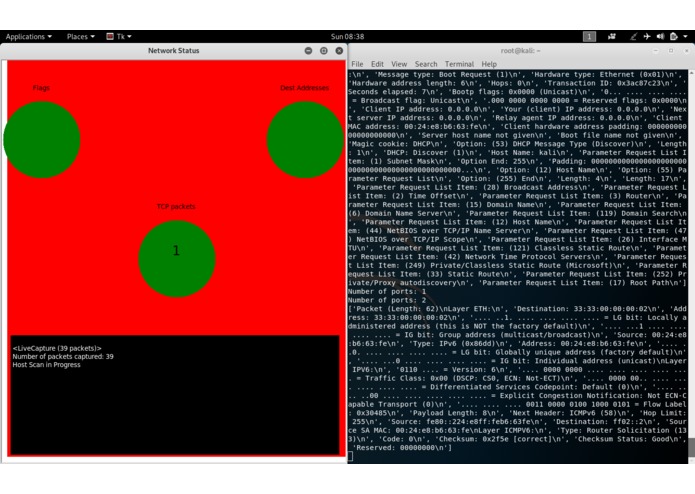
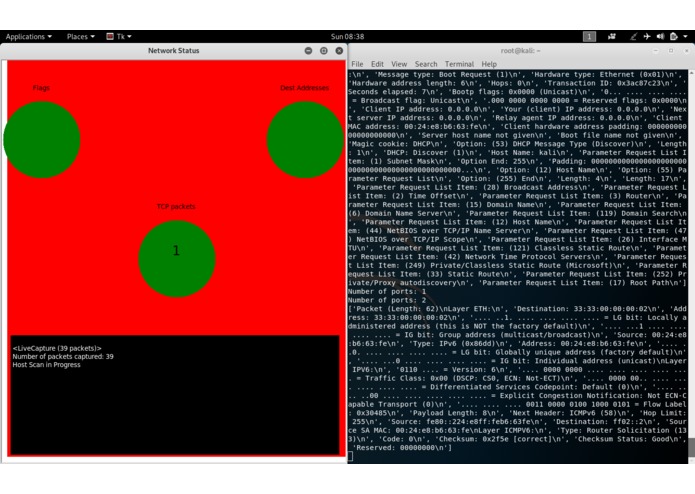
Host Scan traffic in our IDS
-
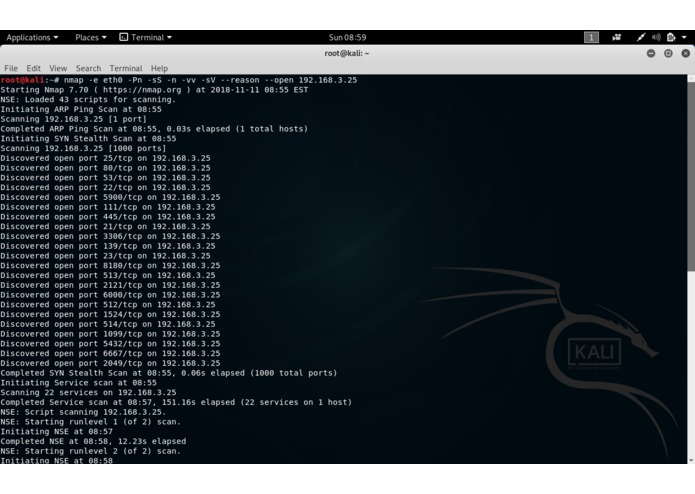
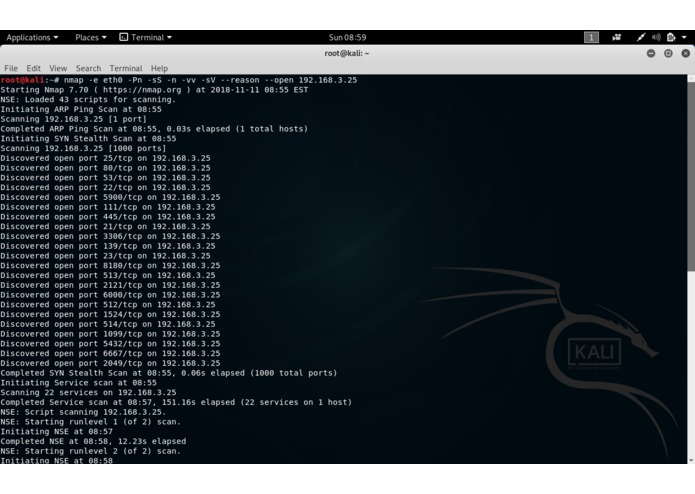
Port Scan on the Attacker Box Pt.1
-
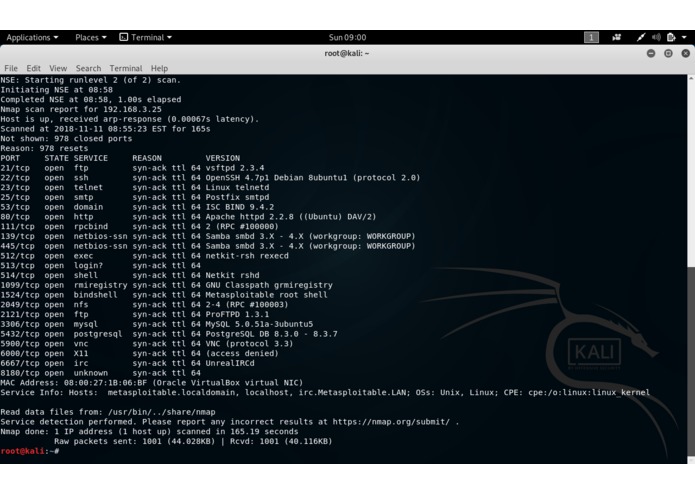
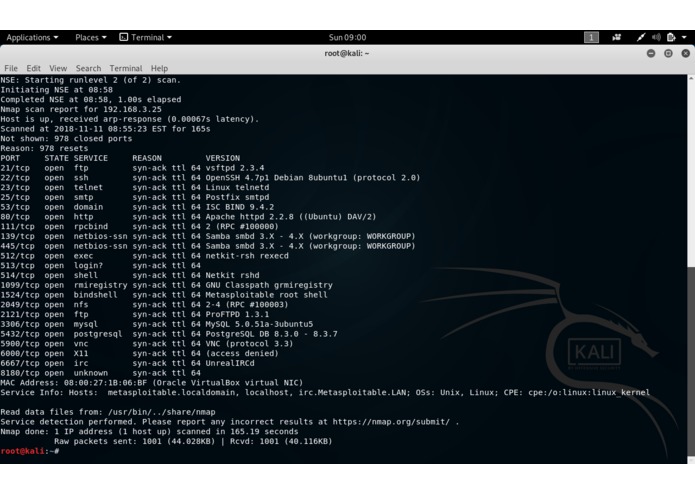
Port Scan on the Attacker Box Pt.2
-
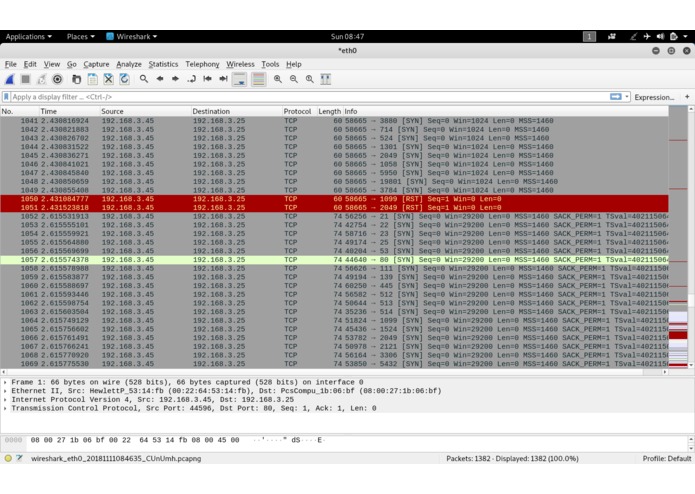
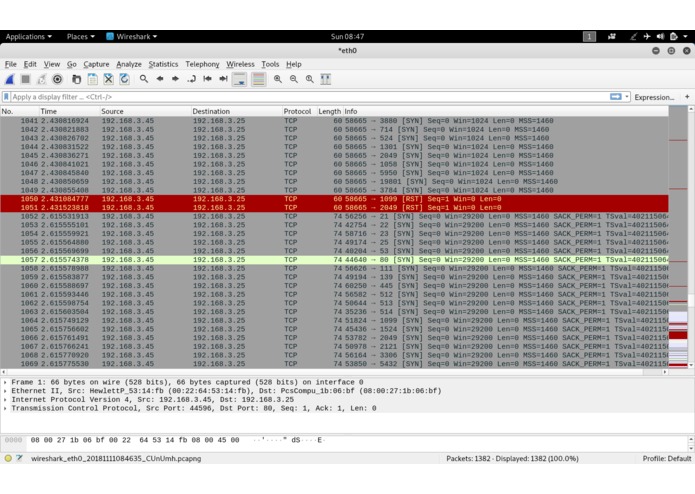
Port Scan traffic in Wireshark
-
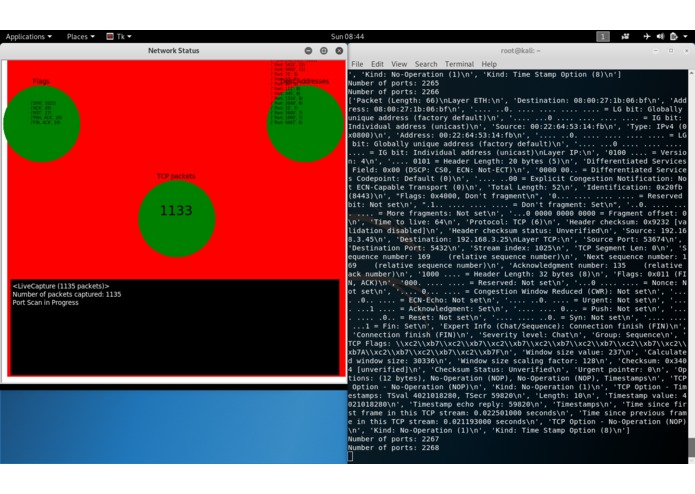
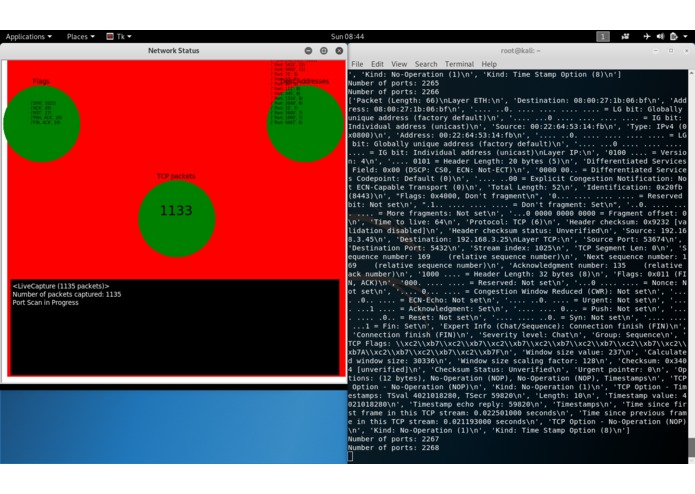
Port Scan traffic in our IDS
Inspiration
Last year we demonstrated how to create a virus and hack a network. This year we wanted to create an Intrusion Detection System to help protect the network.
What it does
We created a program that can read live traffic on a network and tell when a port scan or host scan is taking place. This is often the first step a hacker takes before attacking a network.
How we built it
- We hooked up 3 computers so that 2 were on the same network and could talk to eachother. We hooked up the third computer so it couldn't join the network, but could sniff all traffic. We also created a 2 way network tap with 2 one way sniffing ports.
- We sent pings, host scans, and port scans between the attacker and target, and sniffed the network traffic with Wireshark and the sniffer computer so we could identify which identify the traffic signature of a host scan and port scan.
- We created a program that identifies malicious traffic and clearly displays to the screen when a scan is happening and what type of scan is taking place.
Challenges we ran into
- When hooking up the computers we got weird results. With lots of trouble shooting we identified that one of 3 network cables were the incorrect. To solve this we make our own network cables.
- We had trouble getting Wireshark to see traffic. We asked for a mentors help and they told us what the problem was and how to solve it.
We had a lot of trouble writing the program. Sometimes syntax errors, other times it was identifying how to write code that could tell the difference between different types of traffic.
We were also trying to create a network tap where you could see both sides of the network traffic (3 way network tap), but our electrical engineer later learned that the circuit for that was very complex and would have required her to start building it at the beginning of Technica, so she created us a 2 way network tap instead.
Accomplishments that we're proud of
We're proud that we could create the program and go further to make the program clearly show what what happening on the network.
What we learned
- We learned the symptom of using the incorrect/inconsistent wire types on a network.
- We learned how to use wireshark, how to analyze data on a network, tell what the data means, and identify strange behavior and scanning signatures.
- We learned troubleshooting techniques and honed our programming skills.
What's next for The-Exploit-2
If The-Exploit-2 goes further, it will not only identify different types of network scans, it will identify when malware is running on a network, and perhaps even be able to tell you what type of malware. If we were to also include an IPS (Intrusion Prevention System) that received this information, it could stop the attack and/or scan immediately as it's happening.
Built With
- python
- turtle-graphics


Log in or sign up for Devpost to join the conversation.