-
-

when temperature too high from threshold
-

Smart Lock Door System
-

Face Recognition when someone registered in database
-

Face Recognition when someone registered in database
-

Face Recognition when someone already marked in database
-

Face not Recognition when someone not registered in database
-
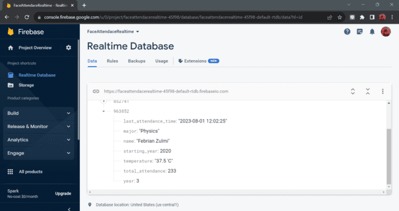
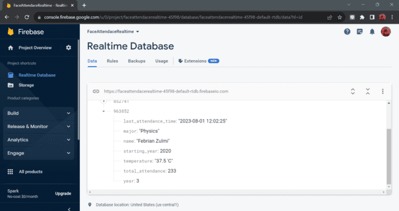
Realtime database for Internet of Things
Inspiration
In today's technological developments, room security systems requires a higher level of security, especially in rooms that Store important data and assets in a company or agency.
What it does
Security the room still has a conventional entry gap that can be utilized by irresponsible person. Therefore, a system was developed secure entry into the room using identity verification such as keys, cards, passwords, and so on. However, this method is considered inadequate effective because humans have limitations in remembering objects and combination of numbers. To overcome this problem, many systems are used biometric-based security. This method uses characteristics unique individuals such as fingerprints, faces, irises, or voices to recognize and verify someone's identity. Biometric authentication is considered more secure because it is difficult to fake or change. This system works with collect an individual's biometric data and compare it with that data has been previously registered in the database. If there is an agreement, access to the room given, so that only authorized people can enter. Profit Biometric-based security includes a high level of security, ease of use, and resistance to loss or theft. However, there are also considerations regarding privacy, implementation costs, and potential identification errors in the use of this system.
How we built it
In this research, several research procedures were carried out, in including: a. Literature study regarding door security systems, biometric authentication, facial recognition and processing for temperature, voice recognition, RFID, as well other circuits that will be used in the future system made. b. Prepare the tools and components needed to be used and designed in research. c. Assembling the system to be studied, facial recognition for temperature and voice recognition, as well as RFID. Then program both systems so that can carry out training and testing on facial and voice samples. d. Carrying out training and testing of facial and voice samples so that they can be recognized voices and faces studied. e. Designing an entire integrated system between voice recognition and face and the use of RFID. Testing the room security system using biometric authentication face and voice along with RFID and retrieve data from the system that has been created
Challenges we ran into
- Design a room security system based on facial biometric identification as well as image processing for temperature.
- Design a room security system based on voice biometric identification.
- Know the working capabilities of the facial and voice biometric identification system and RFID as additional security if an error occurs in the system room security
What we learned
This research succeeded in creating a security system that combines facial biometric identification with image processing to temperature estimation using a webcam camera. Results of characterization This facial recognition shows that the camera can work up to a distance 55 cm in recognizing faces. Although this system is less accurate if compared to the use of thermal cameras or direct temperature sensors however, this achievement shows great potential in improving security room. With this approach, the security system can provide positive impact in improving security in various environments.
This research has also succeeded in integrating recognition technology sound into the room security system which allows the system to identify individuals based on their unique sound patterns individual. The results of the characterization of the Voice Recognition module show that the module can work up to a distance of 15 cm in recognizing sounds with quiet environmental conditions or around 30dB.
This research has also succeeded in integrating RFID technology as additional precautions to provide extra protection against potential system disruption. Results from the characterization of this RFID sensor shows that the sensor can work up to 3 cm in detecting card.
What's next for Smart Door Lock System
Suggestions for future research reflect on the results of research that has been done the author did.
- It is better to use a laptop using a mini PC with qualified specifications to make it more efficient and flexible for side installation door, because using a laptop is too big and takes up a lot space if installed next to the door.
- Substitution is required for the Arduino V3 Voice recognition which has the ability to recognize and detect sounds better, due to Arduino V3 Voice recognition module used in this research not good at recognizing and detecting each individual's voice.
- Image processing for temperature with this webcam camera requires further development, so that this system is able to detect more temperatures accurate






Log in or sign up for Devpost to join the conversation.