-
-
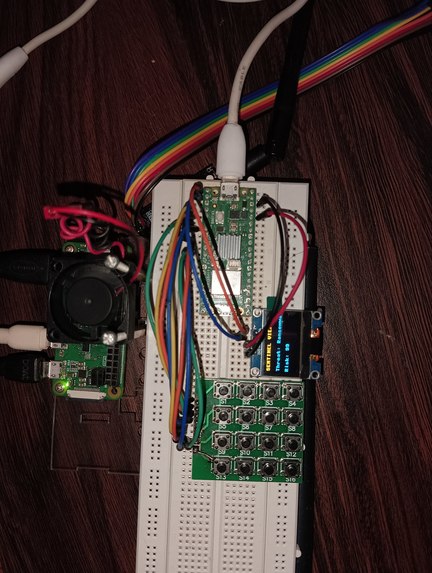
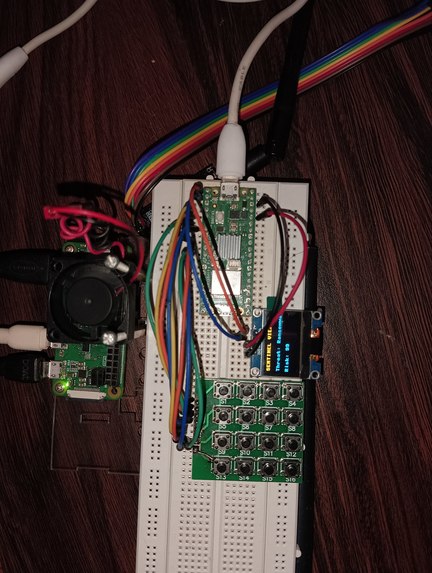
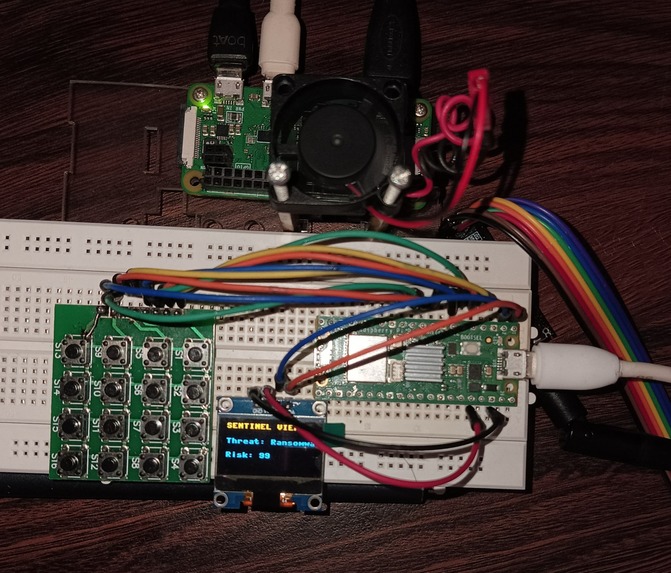
Hardware-setup. I have used a raspberry pi pico (Edge device), raspberry pi zero w (gateway to cloud), 4x4 keypad for attack simulation.
-
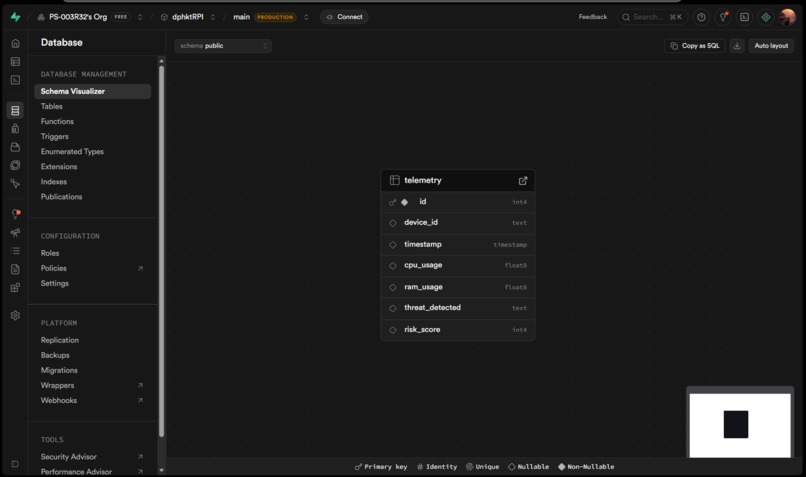
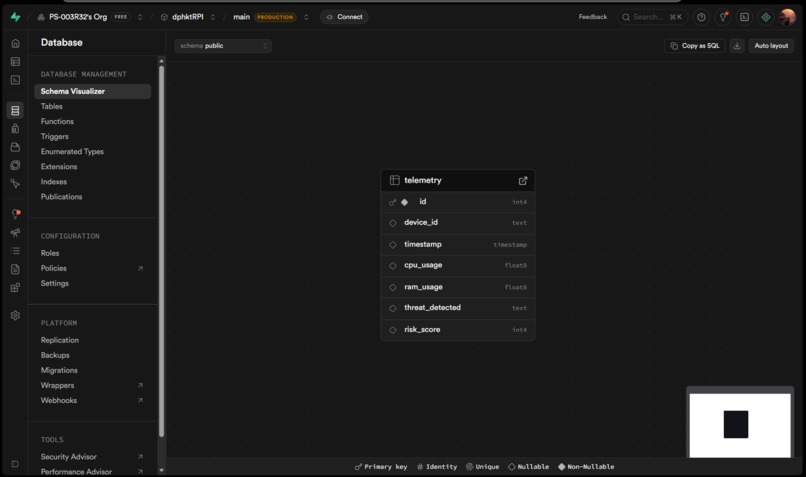
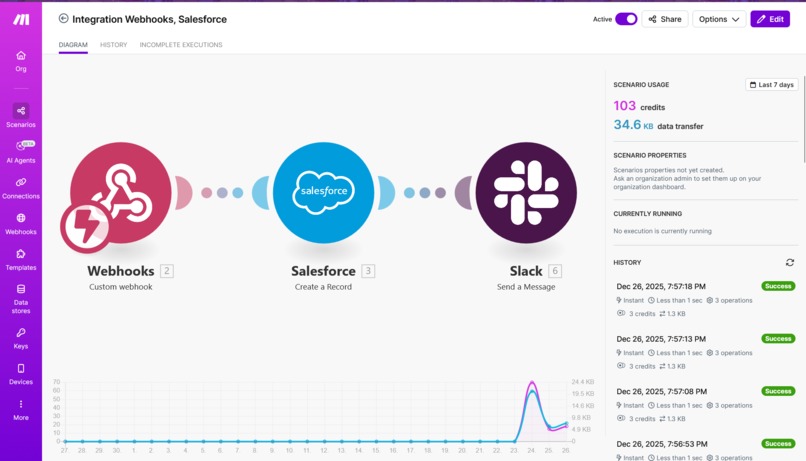
Supabase database setup using PostgreSQL. Webhook from Make.com automation for Salesforce ticket and Slack message sending feature.
-
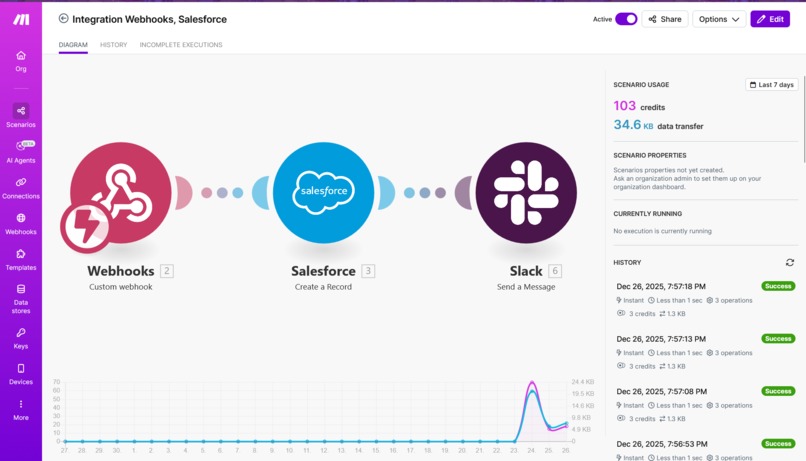
Webhook from Make.com automation for Salesforce ticket and Slack message sending feature.
-
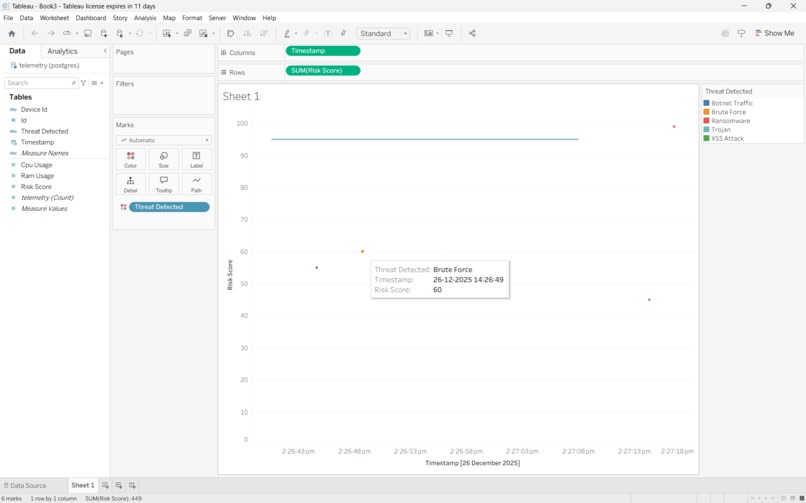
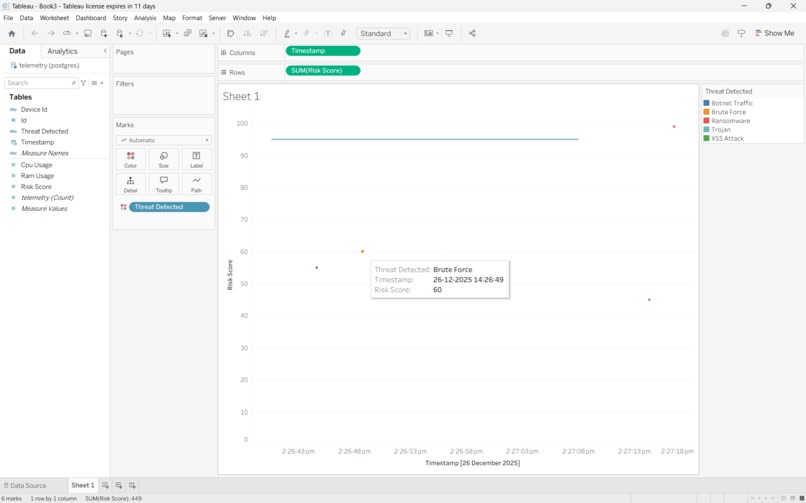
Live attack vectors graph visualization with complete details on the Tableau Desktop.
-
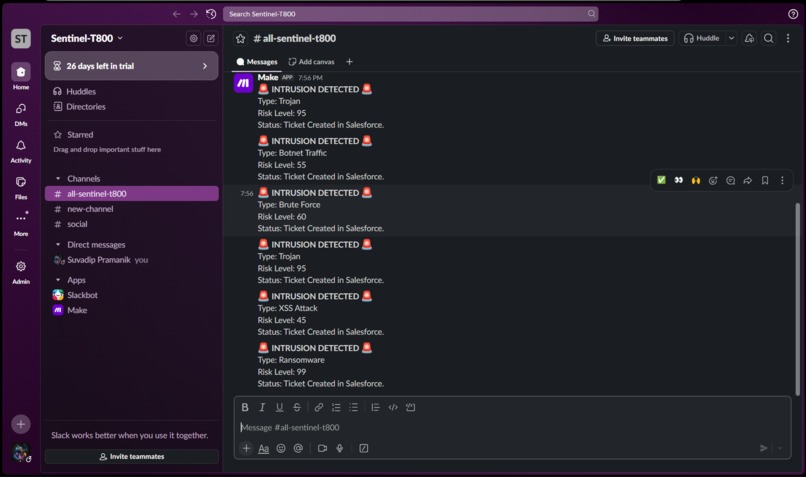
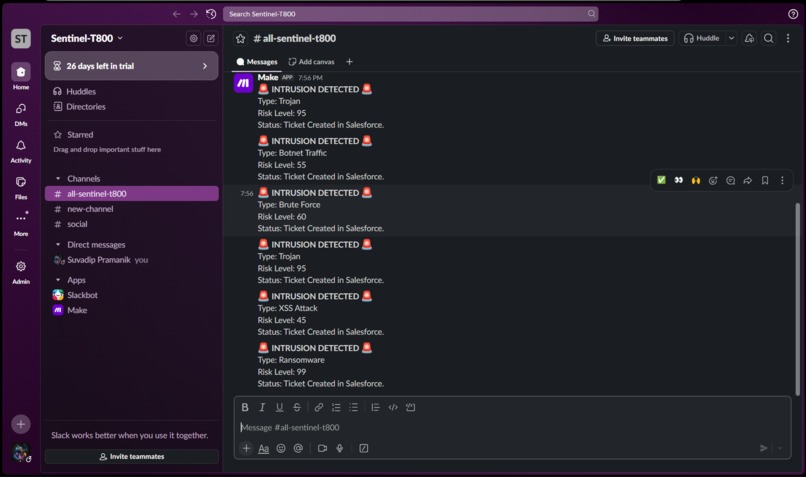
Automated Slack message generation using make.com webhook
-
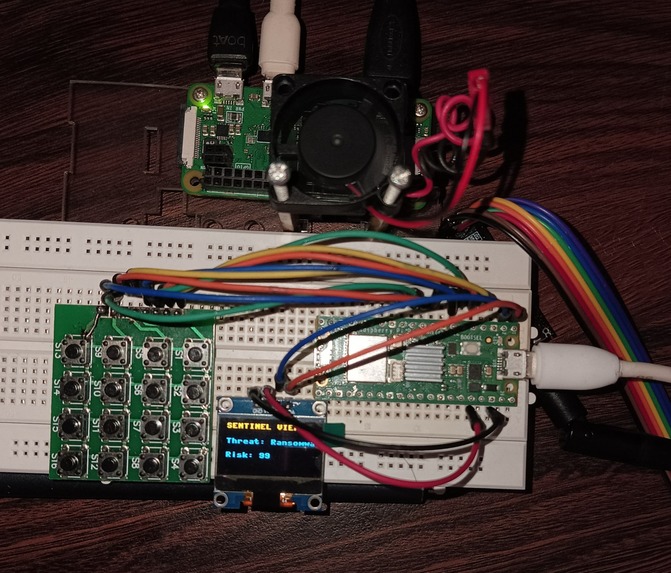
Hardware-setup-2 shows the attack vector on the oled. Each button is assigned a different attack vector for simulation of a real attack.
-

tiny hands
Inspiration
In the high-stakes world of cybersecurity, the gap between Detection and Response is where the damage happens. Traditional Intrusion Detection Systems (IDS) often operate in silos—logging threats to a database but failing to trigger immediate, tangible action. We wanted to close this gap. Our inspiration came from the concept of a biological nervous system: when your finger touches a hot stove, you don't wait for a "log entry" to be written to your brain; you react instantly. We envisioned Sentinel as a digital nervous system for network security, where the sensor (the Edge Device) feels the pain (the Threat) and the brain (the Cloud) reacts in milliseconds. We wanted to move beyond boring log files and create a system that makes cyber threats physical, visible, and actionable.
What it does
Sentinel is an end-to-end IoT Cyber Threat Detection pipeline. Detects: A physical Edge Device (Raspberry Pi Pico) simulates specific network attacks (like DDoS, SQL Injection, or Brute Force) via a keypad interface. Transmits: The data is securely transmitted over a custom USB serial protocol to an intelligent Gateway (Raspberry Pi Zero W). Orchestrates: The Gateway instantly routes this data to the Cloud (Supabase) for storage and triggers an automation workflow (Make.com). Reacts: Within seconds, the system: Alerts: Sends a "High Priority" notification to a Slack channel. Tickets: Creates an official Incident Case in Salesforce for enterprise compliance. Visualizes: Updates a live "Security Operations Center" dashboard on Tableau, plotting the attack's Risk Score R(t) over time.
How we built it
We architected the system in three distinct layers:
The Physical Edge (Sensory System): We built a custom hardware interface using a Raspberry Pi Pico. We wrote Micro Python firmware to handle interrupt-based inputs from a 4x4 Matrix Keypad and provide local feedback via an SSD1306 OLED display. This device communicates via a custom JSON-over-Serial protocol.
The Intelligent Gateway (Nervous System): We used a Raspberry Pi Zero W as the bridge. We developed a multi-threaded Python service that performs "Port Hunting" to auto-detect the Pico on USB insertion. It reads the serial stream, enriches the data with device telemetry, and performs parallel API requests to our backend.
The Cloud Brain (Cognitive System): Database: We utilized Supabase (PostgreSQL) for its high-performance connection pooler. We used the psycopg2 library to inject secure, SSL-encrypted logs directly into the DB. Automation: We replaced complex server-side code with Make.com Webhooks, allowing us to route data to Slack and Salesforce simultaneously.
Visualization: We connected Tableau Desktop directly to the Supabase backend port (6543), creating a real-time visualization that refreshes as new threats arrive.
Challenges we ran into
The "Silent" USB Port: One of the biggest technical hurdles was the Raspberry Pi Zero's Linux Modem Manager service, which kept "hijacking" our USB serial port, preventing the script from reading data. We had to perform deep system administration to disable these services and write a robust Python script that could recover from USB disconnections automatically. Database Port Conflicts: Connecting Tableau to Supabase was not straightforward. We discovered that the default PostgreSQL port (5432) does not support the transaction pooling required for high-frequency IoT logging. We had to reconfigure our entire network stack to use the Session Pooler on port 6543 and enforce strict SSL certificate validation to get the connection stable. Real-Time Latency: Coordinating three different APIs (Supabase, Slack, Salesforce) initially caused a 5-second delay. We optimized our Python gateway to handle these requests asynchronously, bringing the "Detection-to-Alert" time down to under 2 seconds.
Accomplishments that we're proud of
True End-to-End Pipeline: We successfully built a system that touches every layer of the stack: Embedded Hardware -> Linux Gateway -> Cloud Database -> Enterprise SaaS -> BI Visualization. Hardware Integration: Getting two different Raspberry Pi boards (Pico and Zero) to talk seamlessly over a serial interface was a complex hardware challenge that we solved with a custom JSON protocol. Enterprise-Grade Dashboard: Instead of a simple web page, we built a professional Tableau Dashboard. Seeing the graph spike in real-time as we pressed a button on the hardware felt like magic.
What we learned
IoT Protocols: We gained deep experience in JSON serialization over UART/USB interfaces.
Cloud Architecture: We learned the importance of "Connection Pooling" in databases when dealing with high-frequency sensor data.
The Power of Webhooks: We realized that using webhook orchestrators (like Make.com) allows for much faster iteration than writing custom API integrations for every single service.
What's next for Sentinel: Real-time IoT Cyber Threat Detection & Response
AI Risk Analysis: We plan to integrate a Machine Learning model (using TensorFlow Lite on the Pi Zero) to analyze the frequency of keypresses and dynamically calculate the Risk Score R based on attack patterns, rather than hardcoded values. Wireless Edge Nodes: We want to upgrade the Pico to a Pico W to remove the USB cable, allowing us to place "Sensor Nodes" all over a building that report back wirelessly to the central Gateway. Biometric Authentication: Adding a fingerprint sensor to the hardware to ensure that only authorized security personnel can clear or acknowledge a threat from the physical device.
Built With
- make.com
- micropython
- postgresql
- python
- raspberry-pi
- salesforce
- slack
- sql
- ssd1306
- supabase
- tableau








Log in or sign up for Devpost to join the conversation.