-
-
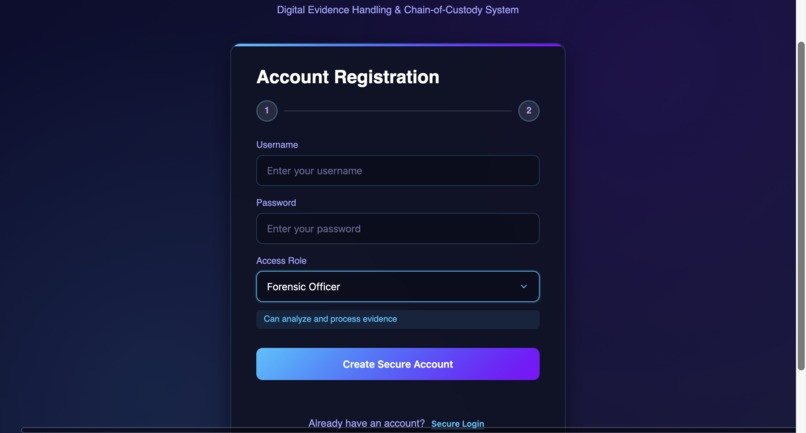
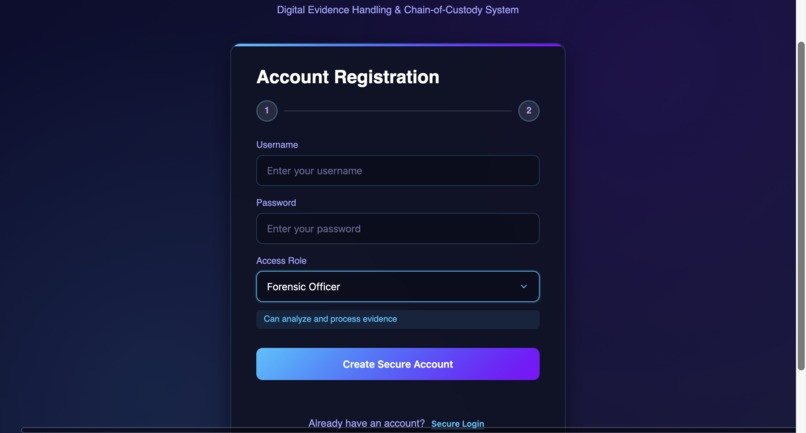
Least-privilege role assignment to ensure secure handling of sensitive medical and forensic evidence.
-
Role-based account registration to separate responsibilities between investigators, forensic officers, and auditors in healthcare workflows.
-
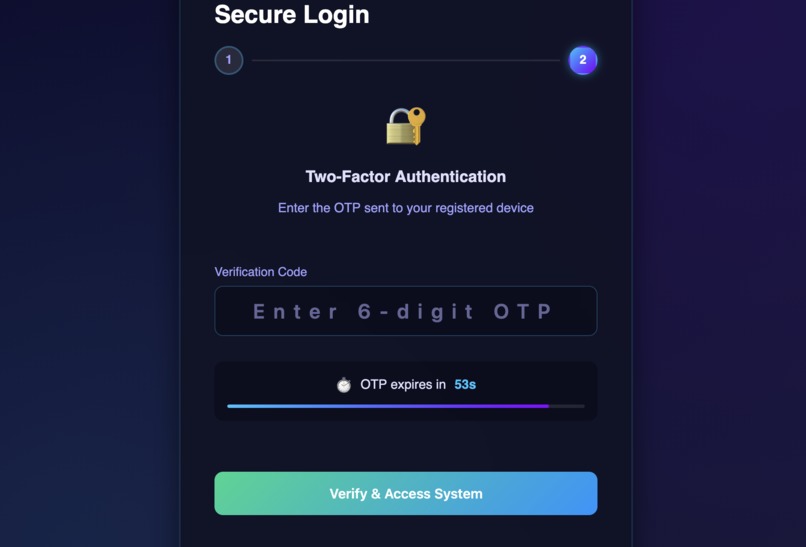
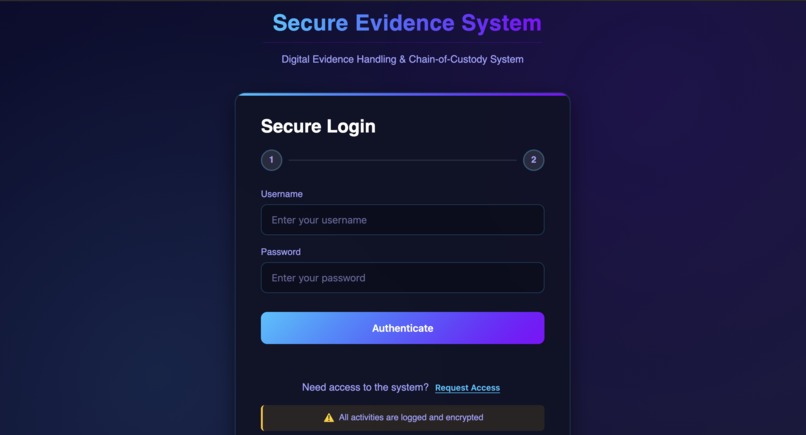
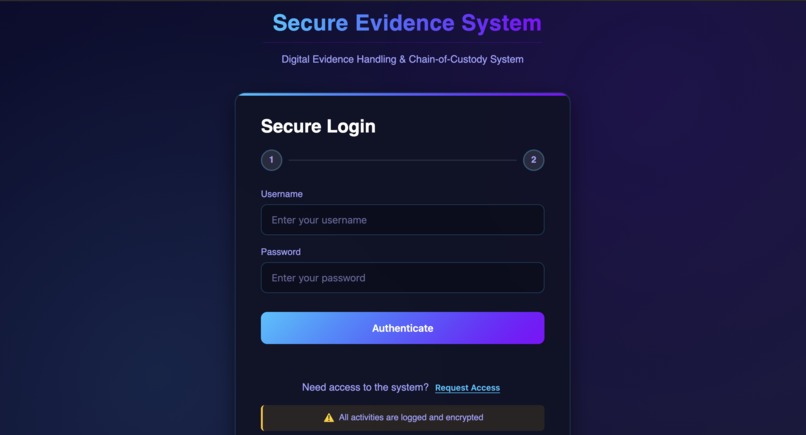
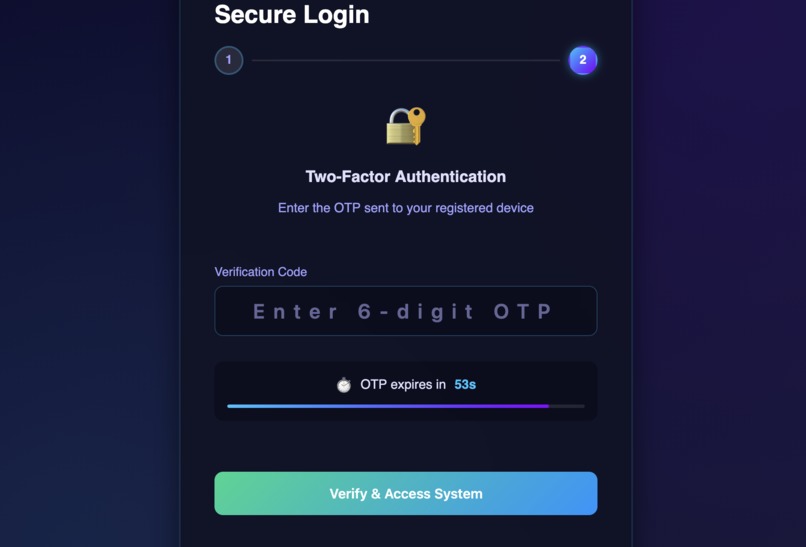
Multi-factor authentication to protect access to sensitive healthcare and medico-legal data.
-
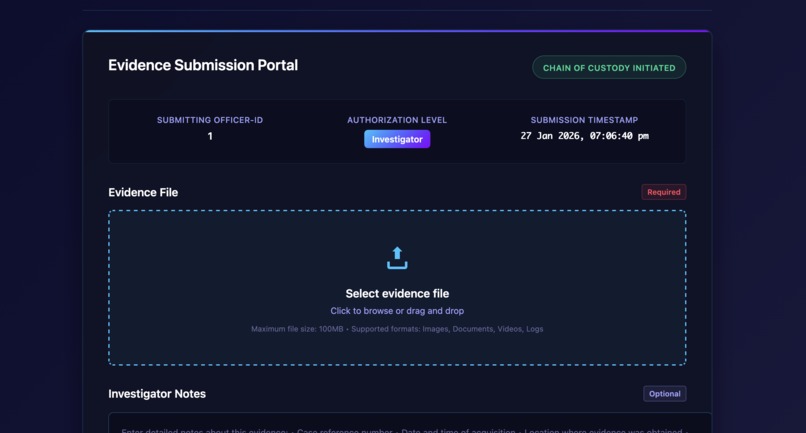
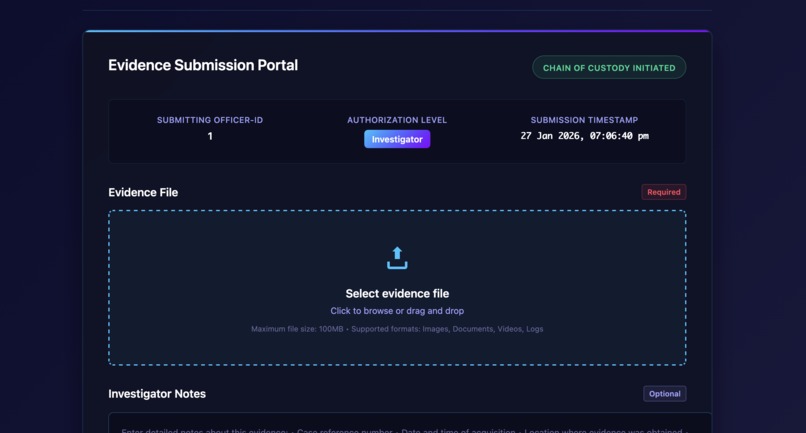
Controlled upload workflow for medical images, reports, and incident evidence with enforced chain-of-custody.
-
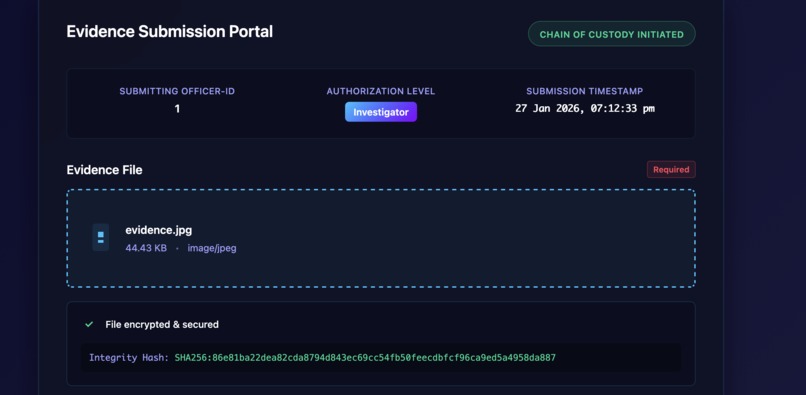
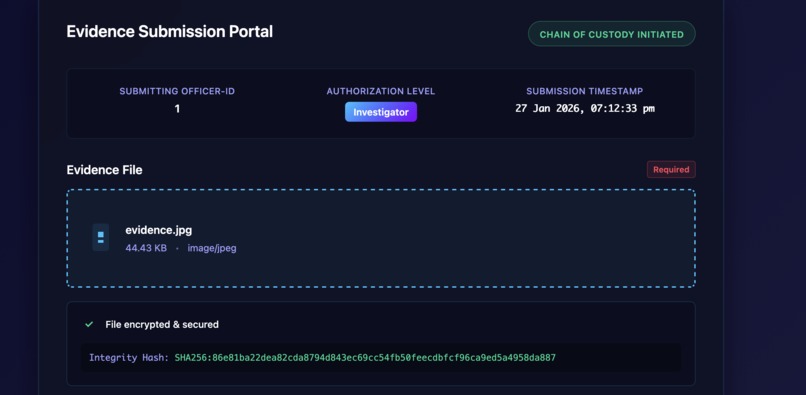
Secure submission of medico-legal and healthcare evidence with encryption, timestamping, and integrity verification.
-
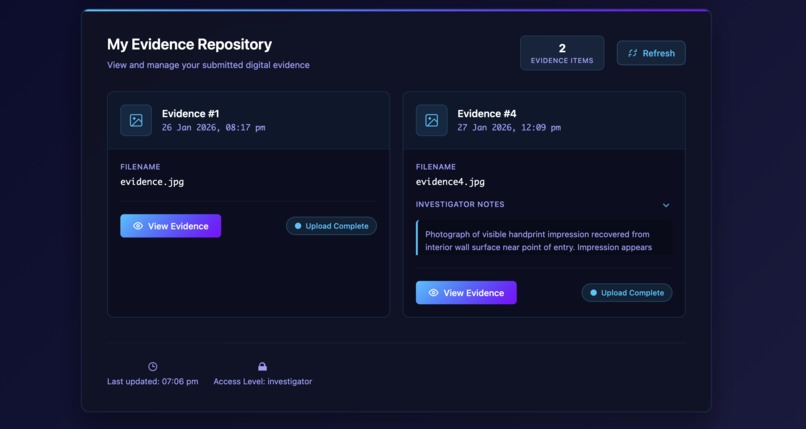
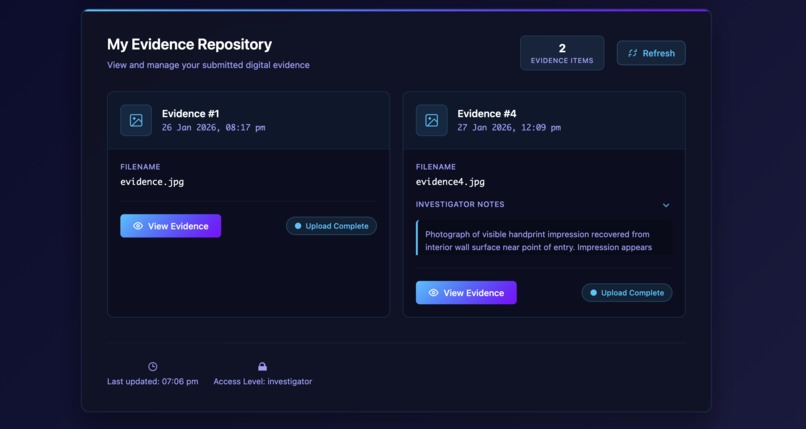
Secure repository for managing healthcare and forensic evidence linked to investigations or clinical incidents.
-
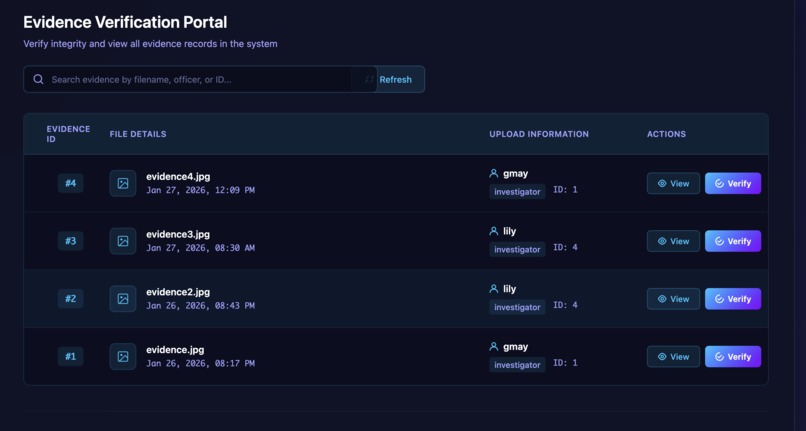
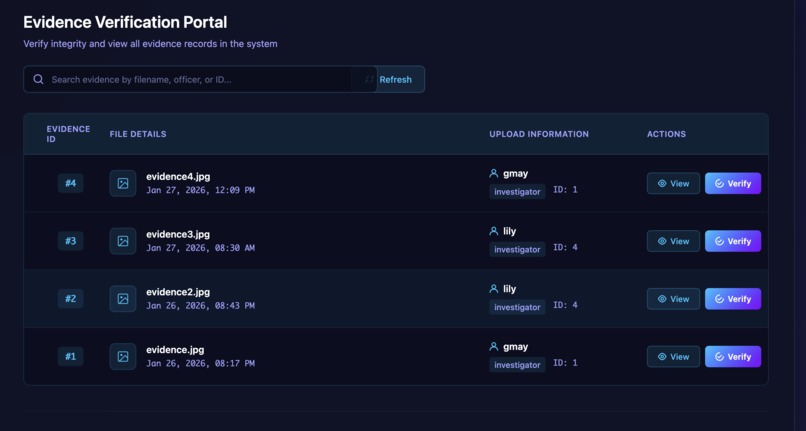
Forensic verification of medical evidence to detect tampering and ensure authenticity of patient-related records.
-
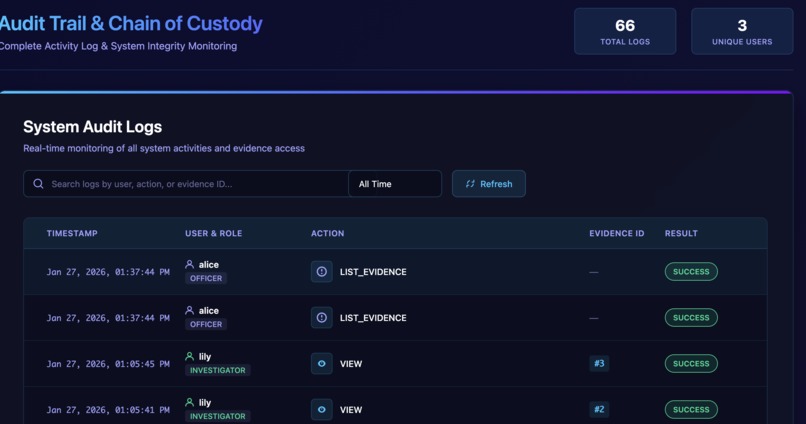
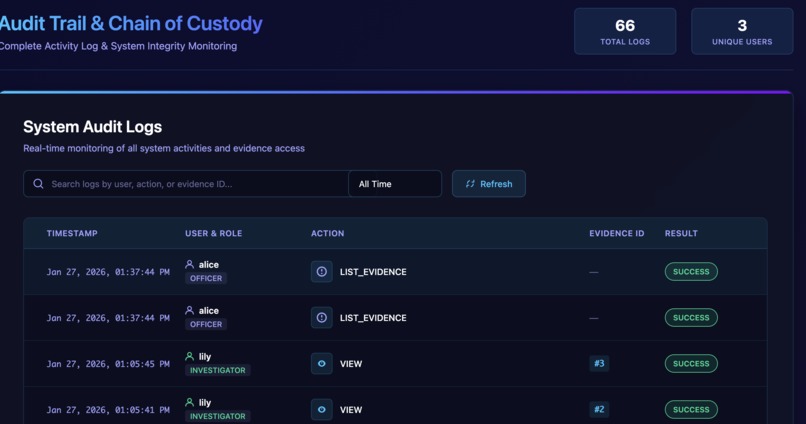
Immutable audit trail ensuring accountability and traceability of sensitive medical and forensic records.
Inspiration
Digital evidence plays a critical role in healthcare investigations, medico-legal cases, and forensic analysis. Medical images, lab reports, and digital records are often used to make decisions that affect patient safety, legal outcomes, and professional accountability.
However, these digital artifacts are vulnerable to tampering, unauthorized access, and poor access control. In many systems, evidence integrity is assumed rather than cryptographically guaranteed, and audit trails are incomplete or unreliable.
This project was inspired by the need for a secure, verifiable, and accountable way to handle sensitive digital evidence, where trust cannot rely on assumptions but must be enforced by design.
What the Project Does
The Secure Evidence Handling & Chain-of-Custody System is a full-stack application that ensures digital evidence remains:
- Tamper-proof
- Authentic
- Confidential
- Auditable
The system enforces a strict chain-of-custody using cryptography and role-based access control. Every action performed on evidence is logged, verifiable, and traceable.
Although demonstrated using investigator and forensic roles, the system is directly applicable to healthcare and medico-legal environments, such as:
- Hospital incident investigations
- Medical evidence preservation
- Digital forensic verification
- Compliance and audit review
How It Works
- Users authenticate using multi-factor authentication (password + OTP).
- Evidence is uploaded by authorized users.
- Each evidence file is:
- Hashed using SHA-256
- Digitally signed using RSA (PSS padding)
- Encrypted using AES
- Encrypted evidence and metadata are securely stored.
- Authorized officers can decrypt and verify integrity using public-key verification.
- All actions are recorded in immutable audit logs to preserve the chain of custody.
Role-based access control ensures:
- Uploaders cannot modify verification records
- Verifiers cannot alter original evidence
- Auditors can review actions without modifying data
How We Built It
Backend
- Python (Flask)
- Flask-SQLAlchemy
- MySQL
- Cryptography library
Frontend
- React
- JavaScript
- CSS
The backend handles cryptographic operations, access control, and auditing, while the frontend provides a clear interface for evidence upload, verification, and monitoring.
Sensitive configuration files, keys, and encrypted storage are intentionally excluded from the repository for security.
Challenges We Faced
- Designing secure workflows without overcomplicating the user experience
- Correctly implementing cryptographic primitives instead of using insecure shortcuts
- Ensuring strict role separation and least-privilege access
- Maintaining audit logs that are meaningful and tamper-resistant
Balancing security, clarity, and usability required careful architectural decisions.
What We Learned
- How cryptography can be applied practically to enforce trust, not just demonstrate theory
- The importance of auditability and accountability in high-stakes systems
- Designing systems where misuse is technically prevented, not just discouraged
- How security architecture directly impacts real-world reliability and trust
Future Scope
With further development, this system can be extended to:
- Hospital compliance platforms
- Cybercrime reporting and investigation tools
- Court-admissible digital evidence management
- Integration with secure cloud storage and key management services
Built With
- cryptography
- flask
- javascript
- mysql
- python
- react
Log in or sign up for Devpost to join the conversation.