-
-
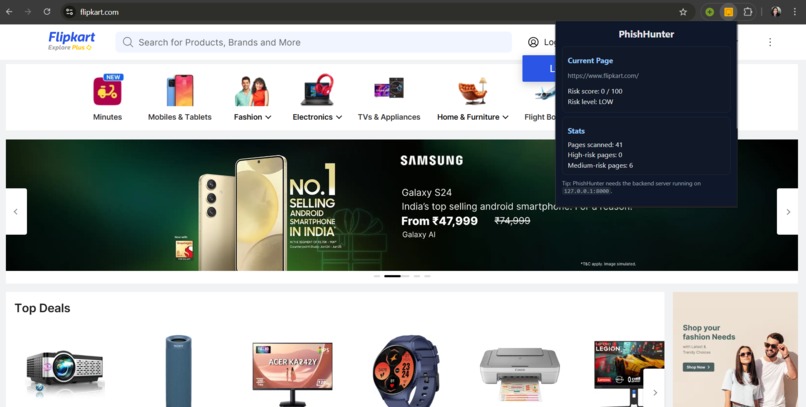
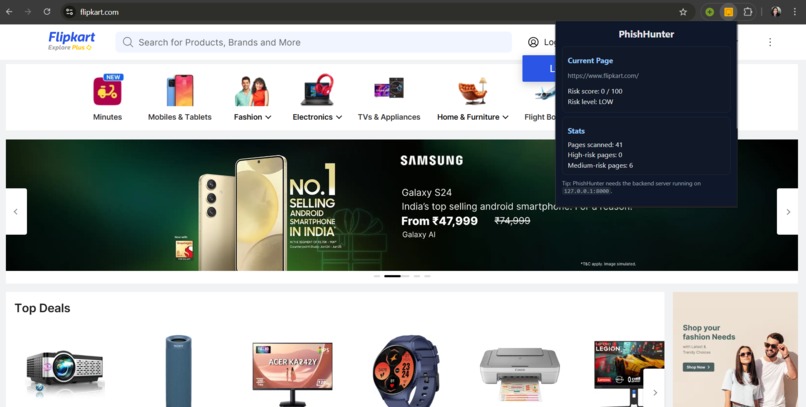
PhishHunter verifies Flipkart as a low-risk website.
-
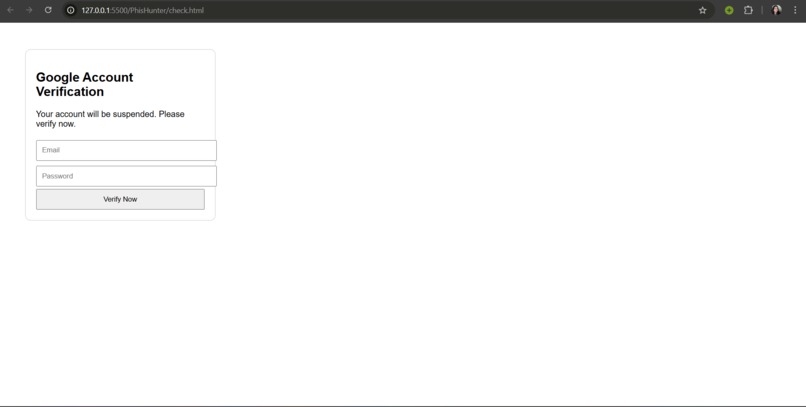
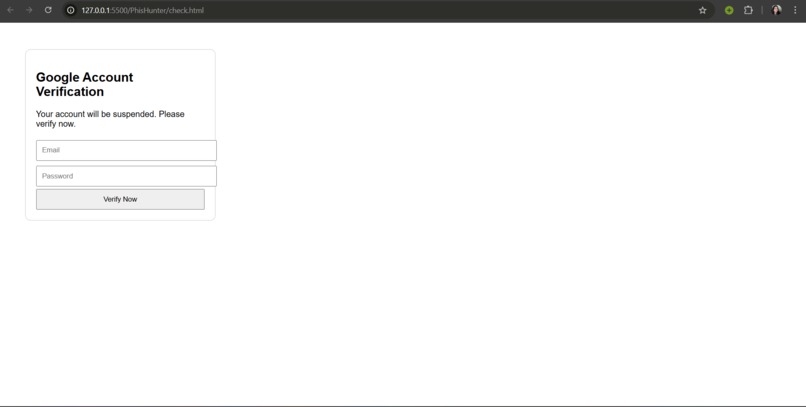
Demo phishing page mimicking a Google login, used to validate PhishHunter’s detection pipeline.
-
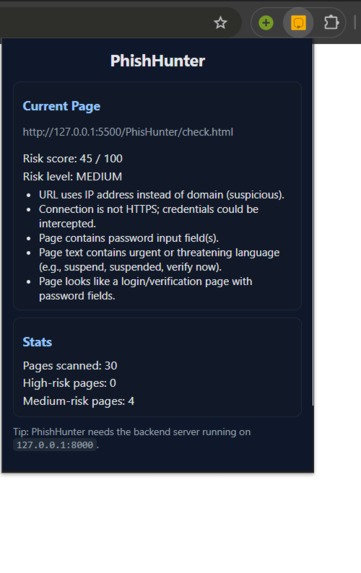
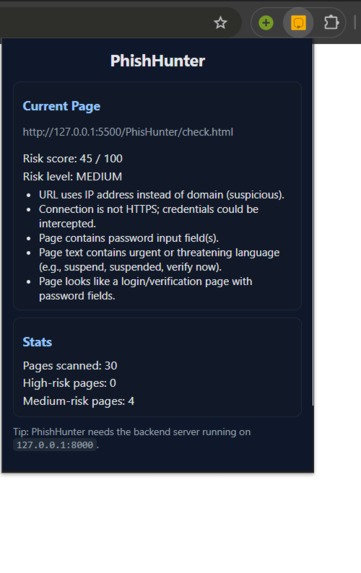
Real-time phishing risk breakdown showing why a login page is flagged as suspicious.
-
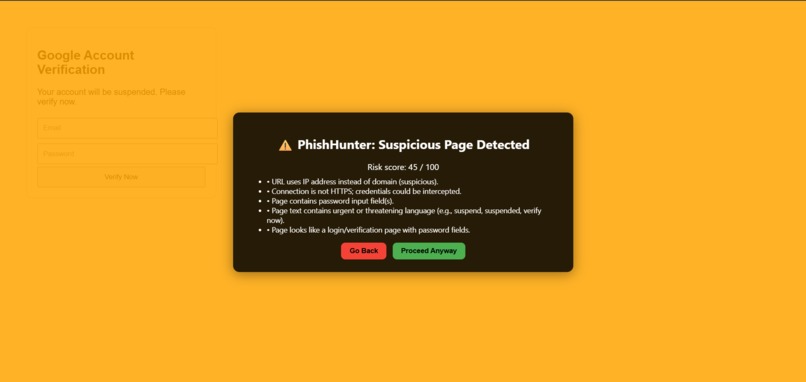
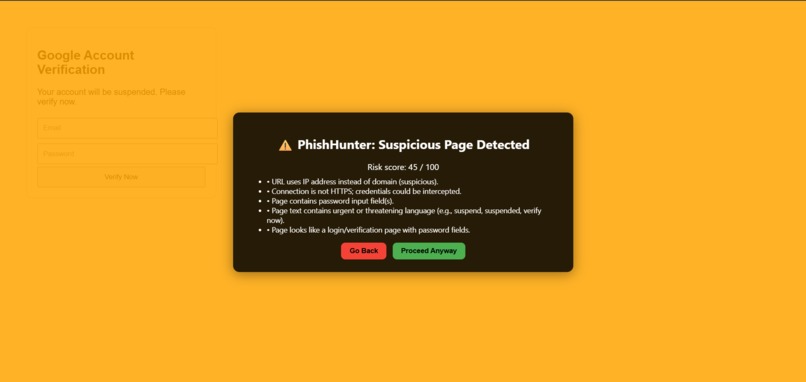
PhishHunter protecting users by interrupting a deceptive login page and clearly explaining why it is unsafe.
Inspiration
Every day, millions of people open links without thinking twice—whether from emails, WhatsApp forwards, job offers, or random websites. Most users cannot differentiate between a real login page and a fake one, and attackers exploit this by creating convincing clones of Google, Microsoft, banking portals, and even government sites.
People unknowingly enter their passwords, OTPs, and financial details… and within seconds, hackers gain full access.
We built PhishHunter because we strongly believe cybersecurity should not depend on how “tech-savvy” someone is. The browser should protect the user—not the other way around.
What it does
PhishHunter is a demo prototype of a real-time phishing detection system. Our current version showcases:
How a browser extension can scan a webpage instantly
How we analyze the URL, page content, DOM structure, and form behavior
How an AI-powered backend can generate a risk score
How users get a clear warning overlay if a page looks suspicious
The prototype demonstrates the workflow, UI, and core detection logic we plan to expand with advanced models.
Even in demo form, it already detects several common phishing indicators.
How we built it
Our hackathon prototype consists of two components:
- Browser Extension (Manifest V3)
Injects a content script into every webpage
Extracts the URL + HTML content
Communicates with the backend
Displays real-time alerts and warning overlays
Popup UI shows risk level & reasons
- FastAPI Backend
Currently using heuristic-based detection, which analyzes:
Suspicious URL patterns
Password fields on untrusted domains
Urgent/scam-like text
Hidden iframes
Insecure or mismatched form actions
It returns a structured risk score (0–100) along with explanations.
Our goal was to build the pipeline, not the full final AI system — and that’s exactly what we achieved.
Challenges we ran into
Building even a demo version of a phishing detector came with challenges:
Balancing detection rules so the system works without being either too strict or too lenient
CORS + extension permissions, which required careful configuration
Time limitations during the hackathon
Designing an overlay system that works on any webpage without breaking layout
Ensuring the backend responds quickly enough for a real-time feel
Since phishing is a complex problem requiring huge datasets and ML training, our challenge was to show how the final product would work, even if the full AI model isn’t implemented yet.
Accomplishments that we're proud of
Built a fully working, end-to-end phishing detection system
Developed a polished browser extension UI with overlays and real-time alerts
Created a modular AI backend that can later integrate ML/CNN models
Implemented clear interpretability: users know WHY a page is risky
Achieved smooth scanning with almost zero lag
Designed a system that can realistically scale for enterprise or student use
Most importantly, We created something that can genuinely protect people from losing their accounts and money.
What we learned
How modern phishing attacks are crafted and why users fall for them
Deep understanding of:
Manifest V3 architecture
Content scripts vs background SW
Cross-origin communication
DOM parsing and security red flags
Building a real-world cybersecurity product with both frontend and backend components
How to balance usability, false positives, and security
Importance of explainability (“why something is dangerous”) in cybersecurity tools
How to design systems that work fast, locally, and securely
What's next for phishHunter
We plan to take PhishHunter to the next level with:
- Machine Learning-based URL classifier
Using real phishing datasets (PhishTank, OpenPhish) to train a model that boosts accuracy.
- CNN-based visual similarity detection
Detect pages impersonating Google, Microsoft, PayPal, etc., even if the URL appears normal.
- Organization dashboard
Admin-level analytics for companies and schools.
- Auto-block mode
Instead of warnings, high-risk pages can be instantly blocked.
- Edge, Firefox, and Safari support
PhishHunter is just getting started—our goal is to make the web safer for everyone, one click at a time.
Built With
- beautiful-soup
- chrome-storage-api
- css3
- fastapi
- github
- heuristic-based-scoring-system
- html5
- javascript
- localhost
- manifest
- pydantic
- python
- tldextract
- url-analysis-engine
- uvicorn
- venv
- vscode
Log in or sign up for Devpost to join the conversation.