-
-
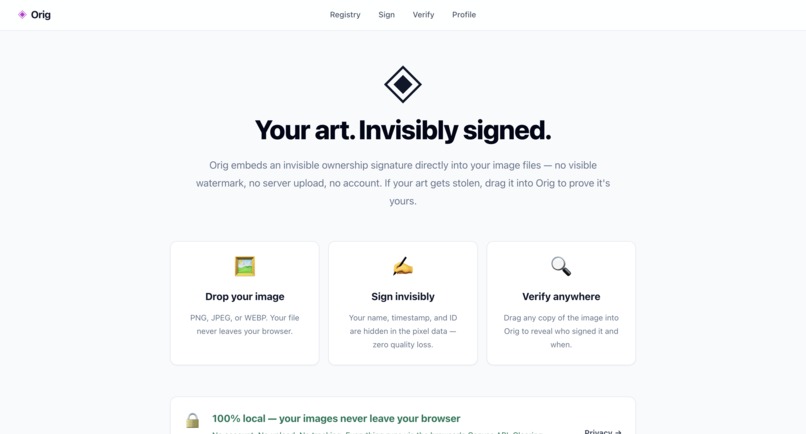
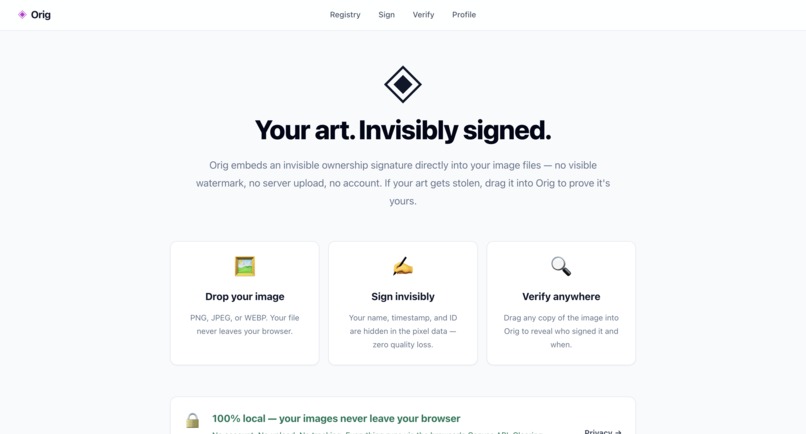
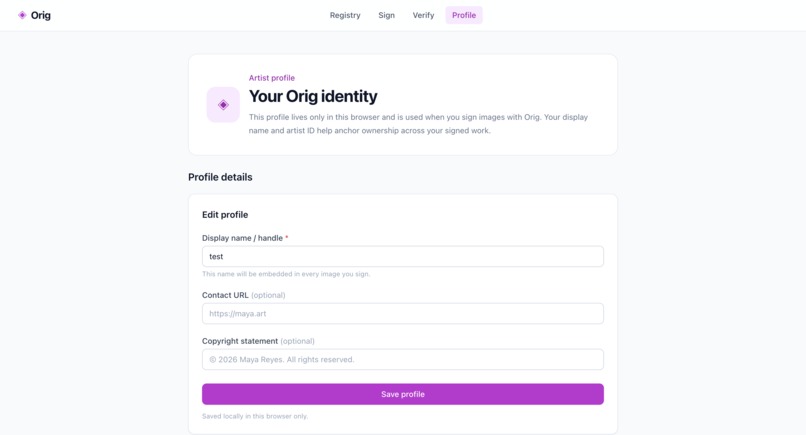
About explains how Orig invisibly signs files, verifies ownership, and keeps images local in the browser.
-
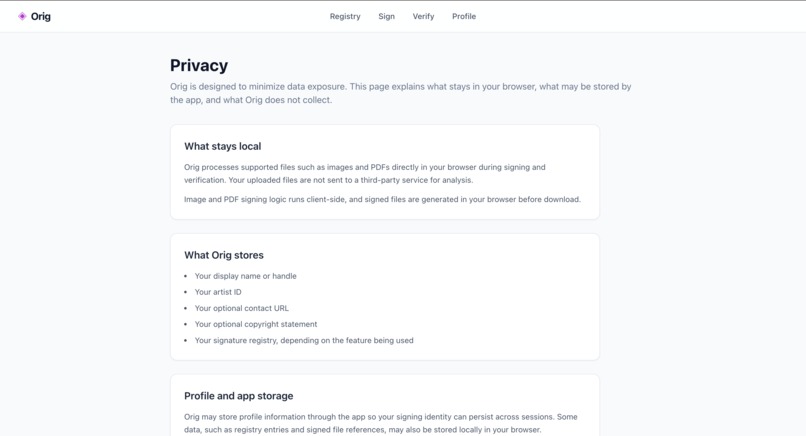
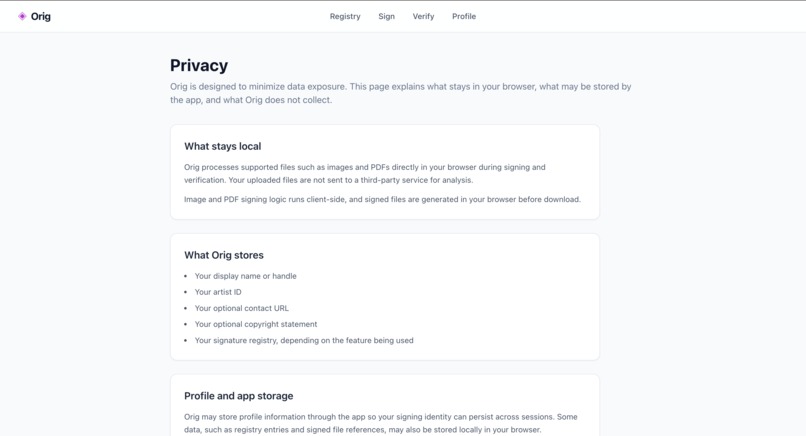
Privacy explains what Orig stores locally, what stays in the browser, and how users stay in control of their data.
-
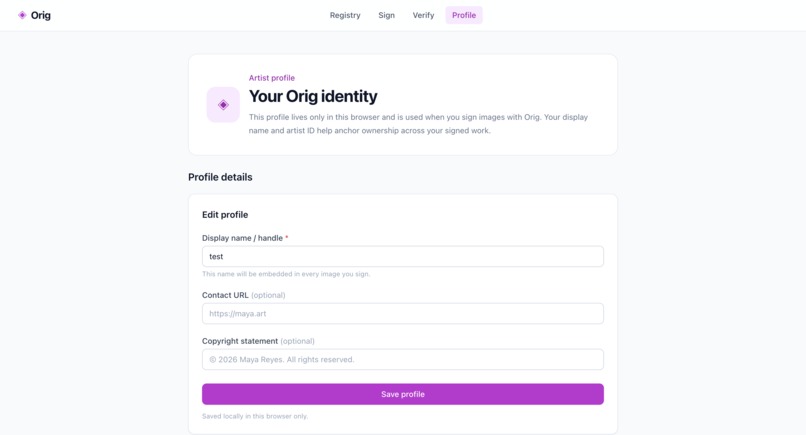
Local profile data is used to embed creator identity into signed files.
-
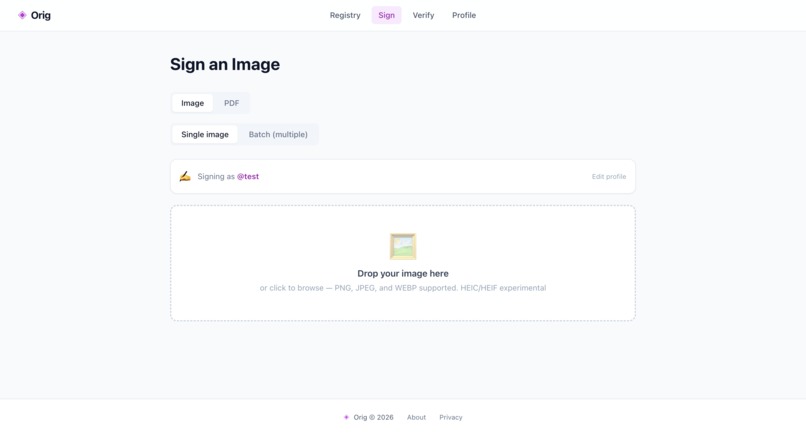
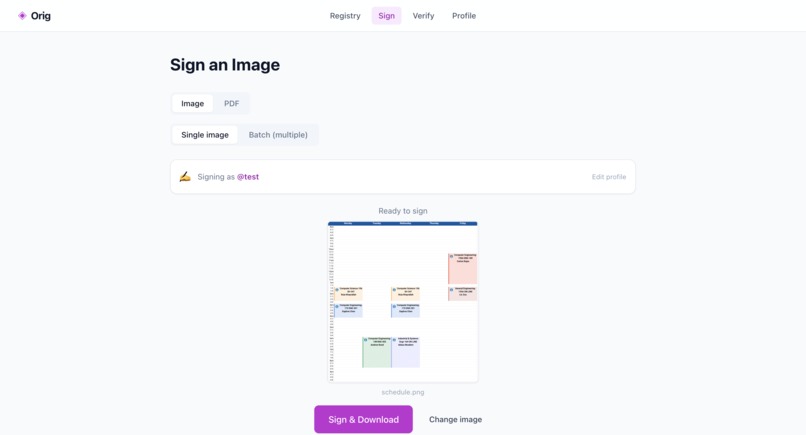
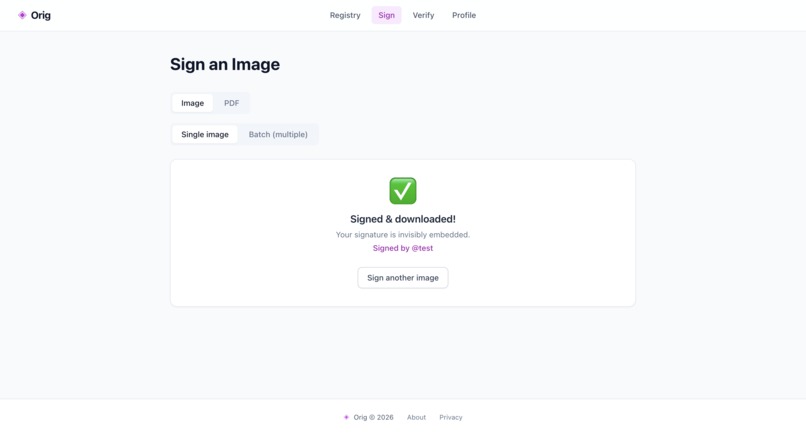
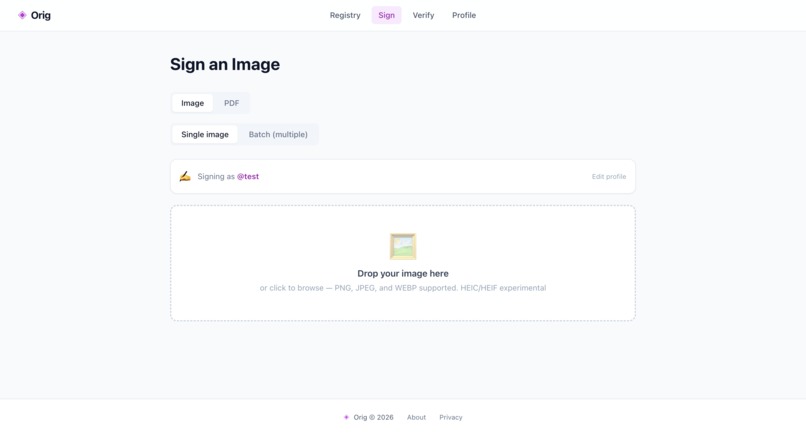
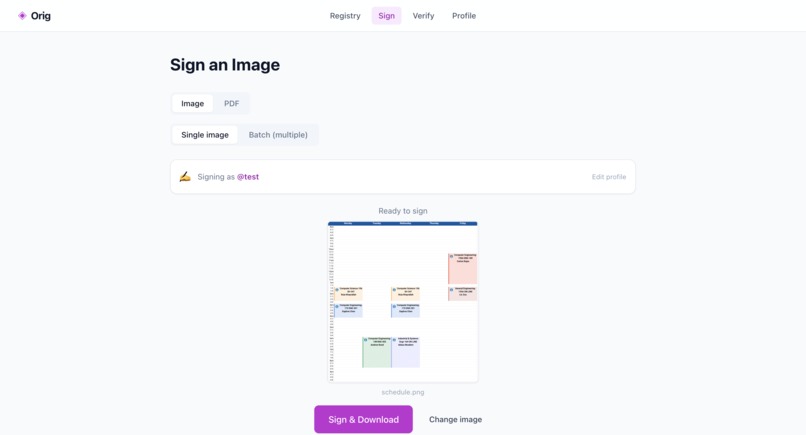
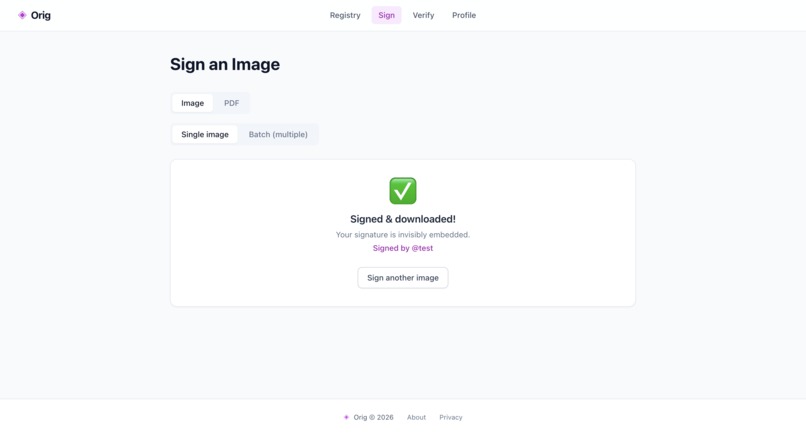
Sign embeds an invisible ownership signature and downloads a protected copy.
-
-
-
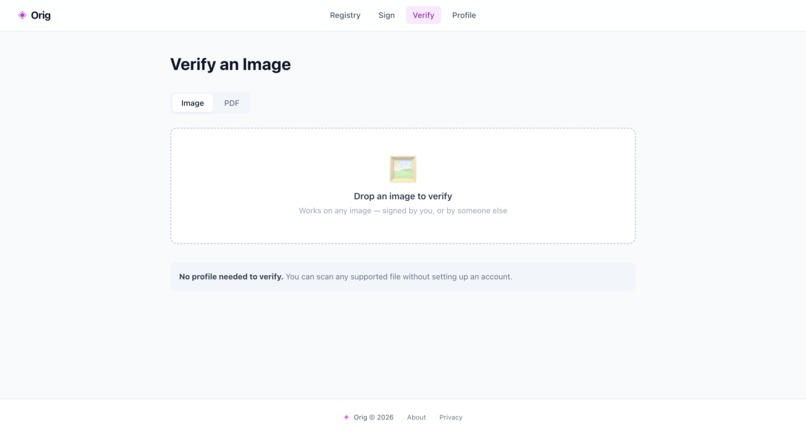
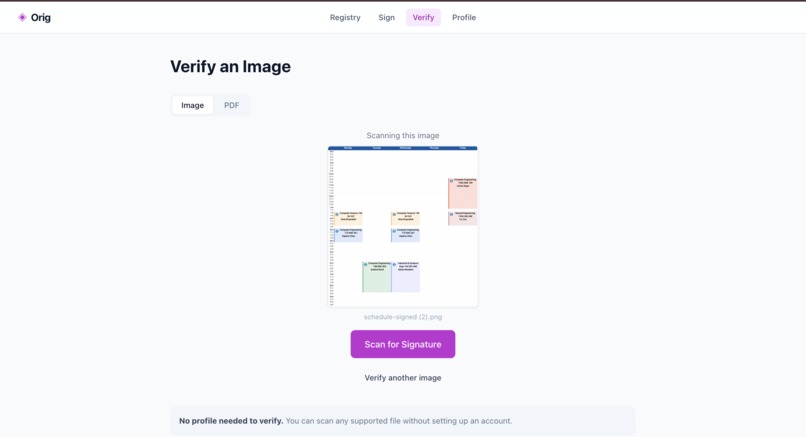
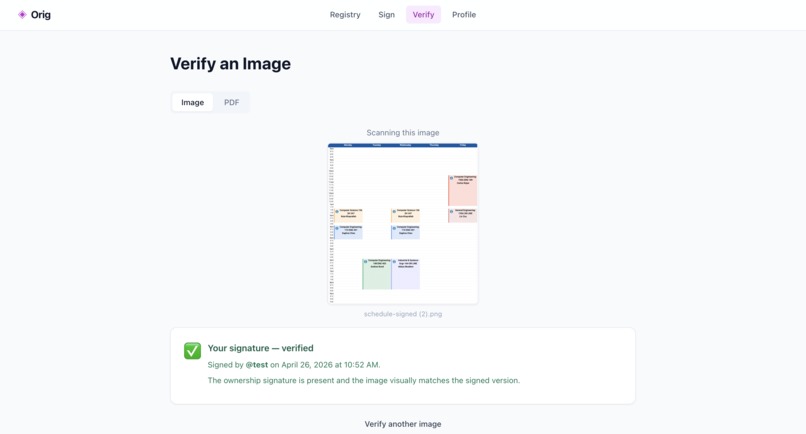
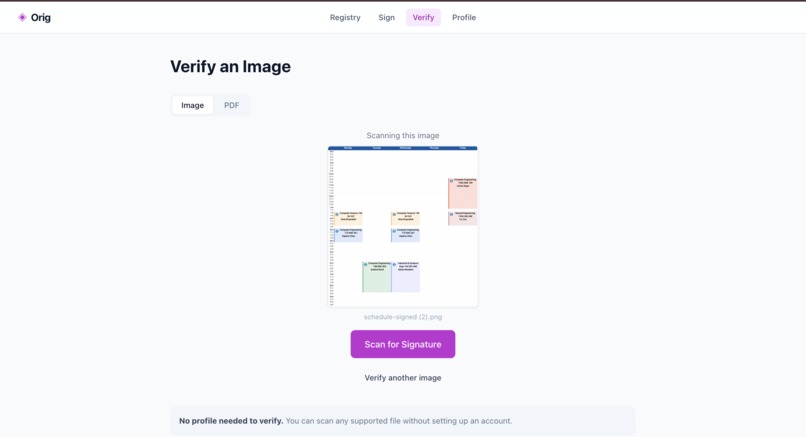
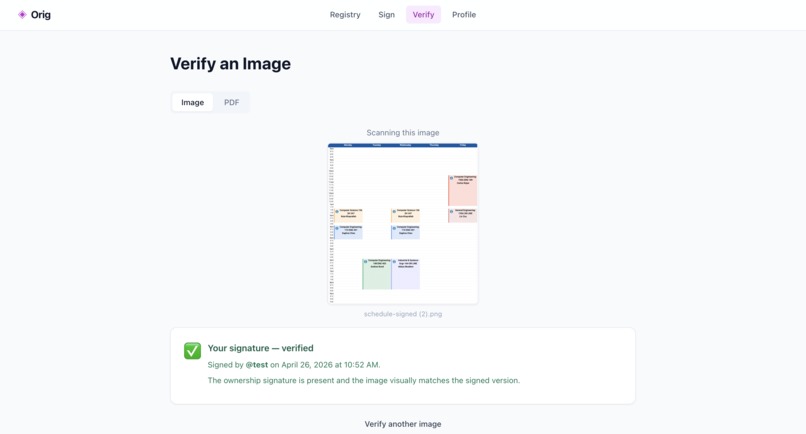
Verify scans images or PDFs for hidden Orig ownership signatures.
-
-
-
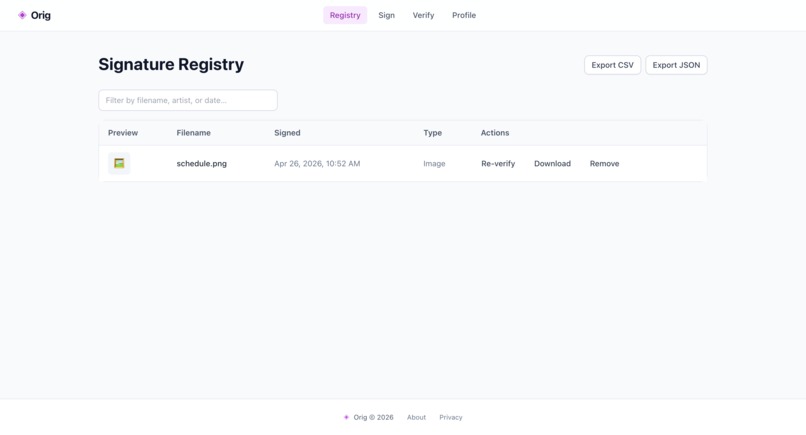
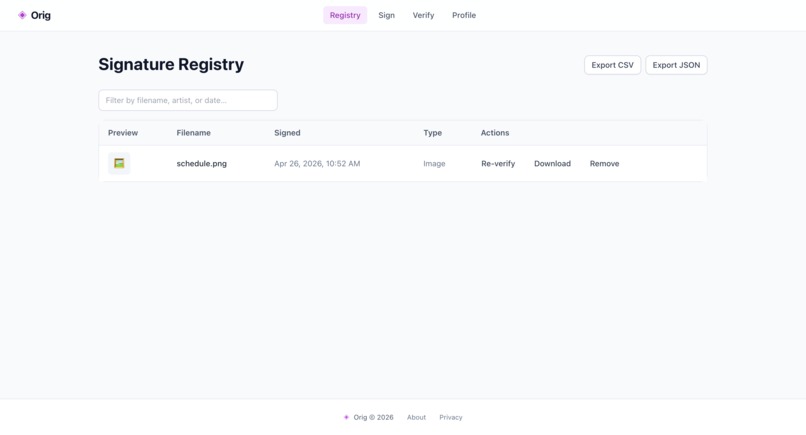
The registry stores signed files, timestamps, and proof records.
Inspiration
Independent artists share their work online every day, but once an image is reposted, screenshotted, or separated from its original account, proving ownership becomes difficult. Most watermarking tools are either visible, expensive, cloud-based, or built for enterprise users. We built Orig to give creators a simple local-first way to attach proof of ownership directly to their work without uploading it anywhere.
What it does
Orig lets artists invisibly sign images and PDFs in the browser. For images, Orig embeds ownership data directly into the pixel data using steganography. For PDFs, Orig adds a verifiable signature payload to the document. Artists can later verify a file by uploading it onto Orig. The app can show whether the file contains their signature, another artist’s signature, or no Orig signature. Orig also includes a local registry that records signed files, timestamps, hashes, previews, and exportable CSV/JSON records.
How we built it
We built Orig with Next.js, TypeScript, and Tailwind CSS. Image signing uses the browser Canvas API to read and modify pixel data locally. The hidden image signature is encoded with custom LSB steganography.
For PDFs, we used pdf-lib to embed an Orig signature marker and ownership payload into the PDF file while keeping the workflow browser-based. The signed PDF can then be downloaded and later checked for the embedded Orig marker and signature data.
Verification decodes the hidden payload from images, compares the artist ID with the local profile, and uses a rotation-tolerant visual hash to distinguish normal rotation from actual visual edits. For PDFs, verification checks for the embedded Orig PDF signature payload. The app stores profile data and the signing registry in localStorage. Files are processed locally in the browser and are not uploaded to a server.
Challenges we ran into
The hardest part was balancing ownership verification with realistic file changes. Exact pixel hashes were too strict: rotating an image, saving it, or rotating it back could trigger false “changed” warnings. We solved this by separating signature detection from visual-content comparison and adding a rotation-tolerant visual hash.
We also had to make the registry useful, not just decorative. We added preview, re-download, and re-verify flows so a registry entry can become part of the verification workflow.
Accomplishments that we're proud of
We are proud that Orig works as a practical local-first creative tool. Users can sign an image, download it, verify it, view it in the registry, and re-verify it later without accounts, uploads, or a backend.
We are also proud of the plain-English UX. The app does not force artists to understand steganography, hashes, or browser storage to use it.
What we learned
We learned that invisible signing is not just a cryptography problem; it is also a product design problem. A technically correct warning can still feel wrong if normal user behavior, like rotating an image, triggers it.
We also learned how to build a privacy-preserving workflow entirely in the browser using Canvas, File APIs, localStorage, and TypeScript.
What's next for Orig
Next, we would improve to support video signing and video verification. Video requires a different technical approach than images because the signature would need to survive across frames, compression, encoding changes, and platform re-uploads. We did not have enough time during the hackathon to build that pipeline, but it is a natural next step for helping creators protect animations, reels, short films, and other video-based work.
We would also like to add clearer export packages for artists so they can generate a complete proof bundle containing the signed file, registry record, timestamp, and verification result.
Built With
- canvasapi
- fileapi
- localstorage
- lsbsteganography
- next.js
- pdf-lib
- sqlite
- tailwindcss
- typescript
- webcryptoapi
Log in or sign up for Devpost to join the conversation.