Inspiration
Phishing attacks today has been a real problem in Tor networks with the end nodes being compromised, may be due to meltdown or spectre attacks. Our project tries to validate the end nodes of the tor network through a dApp by adding the onion address of the end node correlated with the DNS onto the neo blockchain through a smart contract.
What it does do.
The onion networks have been successful in giving a good mount of privacy to the user masking the location and content of the source in layers. However, onion exit nodes have been un-secure since its inception. As the the data has to be in cleartext at the destination.
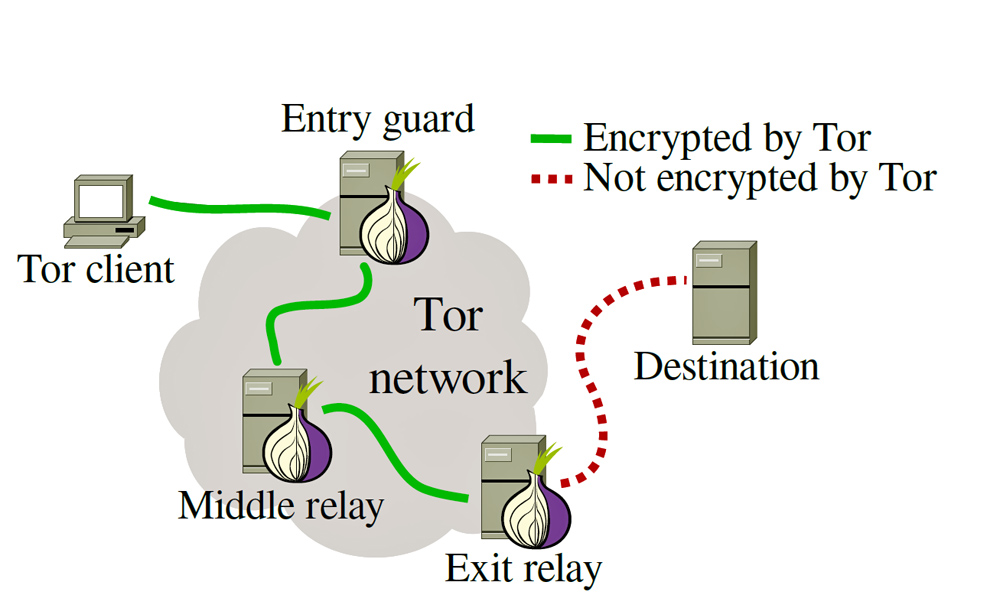
Though the exits are been randomly selected, there are directed attacks by which the hacker in such a way that can control the exit node by owning a large number of tor nodes. There has been rigorous research on this topic, our solution is one among the many to mitigate this problem with the help of neo contracts.
How we decided built it
Instead of allowing the tor network to decide the endpoint, the tor browser queries the blockchain for the DNS of the requested server and gets the correlated onion address of the exit node(which may be a tor service running on the DNS endpoint) ensuring that the exit nodes are secure and thus enabling privacy along with security.
How we built it
The sequence that we worked on are as follows:
- Worked towards setting up the neo-blockchain on our test network: Set up two neo peers on docker and ran both nodes on the aws server.
- Worked towards setting up smart-contracts for the distributed independent verification of .onion "hidden server" addresses, and pairing of address to a human-readable URL format.
Pending:
- Implementing blockchain query
- ToR integration
- Validation and verification
Challenges we ran into
- Being completely new to blockchain dApps, we had to understand the working of neo and set it up on a linux machine.
- Committing the smart contracts. Because we were not able to acquire access to starting gas price for use on the Neo's test network.
Accomplishments that we're proud of
- The Proof of concept. Our Neo-based dApp would have provided great benefit to users of both ToR hidden services and users of ToR needing secure verifiable access to clearnet websites without the threat imposed by malicious exit nodes.
- Setting up the neo blockchain. This was our first attempt at working with blockchain-based dApps.
- Creating a smart contract.
What we learned
- We learned the functionality and methods of interacting with a blockchain and blockchain-based dApps.
- We learned about vulnerabilities inherent in the ToR network in its current implementation as well as how we can mitigate security concerns present in the inherent onion network.
What's next for Neo-OnionDNS
- Completing the Proof of concept and implementing the dApp.
- Extending the tor service by adding the above contribution upstream.
Built With
- blockchain
- c++
- neo
- neo-blockchain
- tor
Log in or sign up for Devpost to join the conversation.