-
-

Coded by AI, Secured by Manifold
-
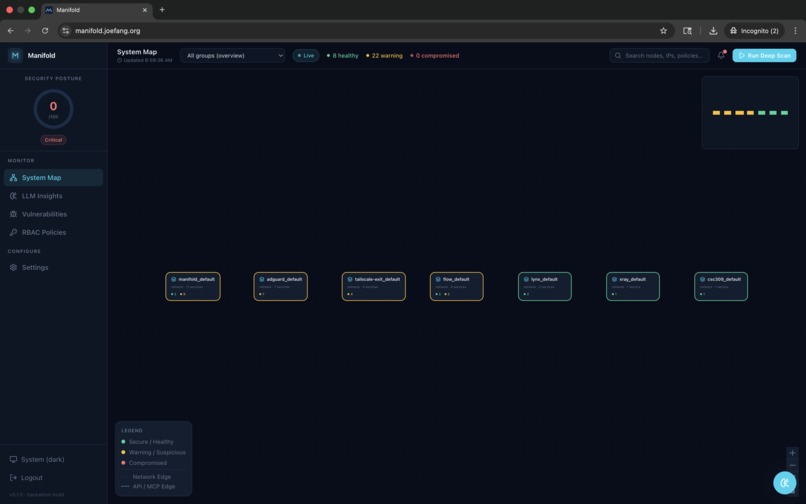
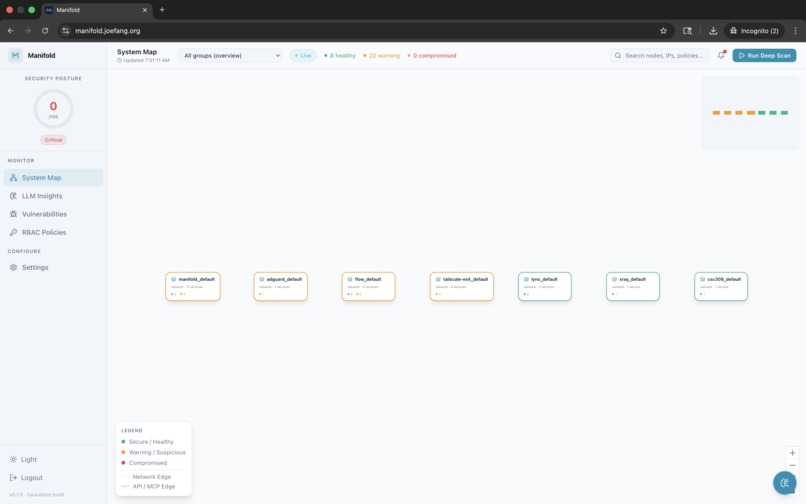
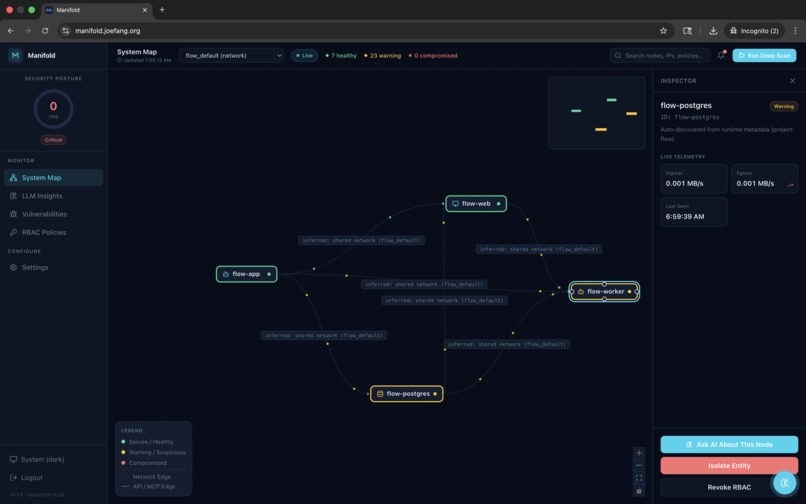
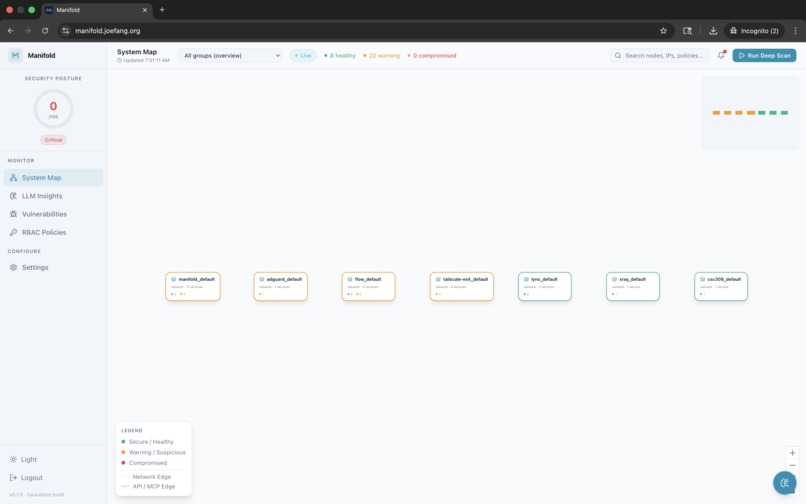
System Map view showing a live service topology graph.
-
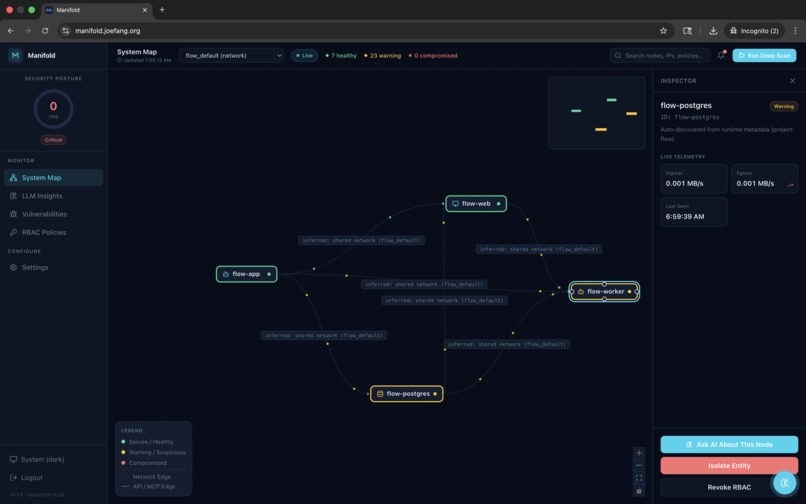
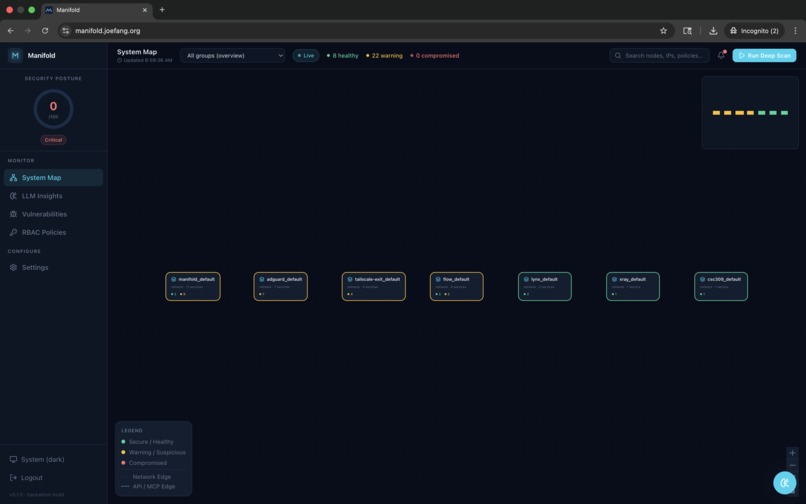
System Map with active threat detection.
-
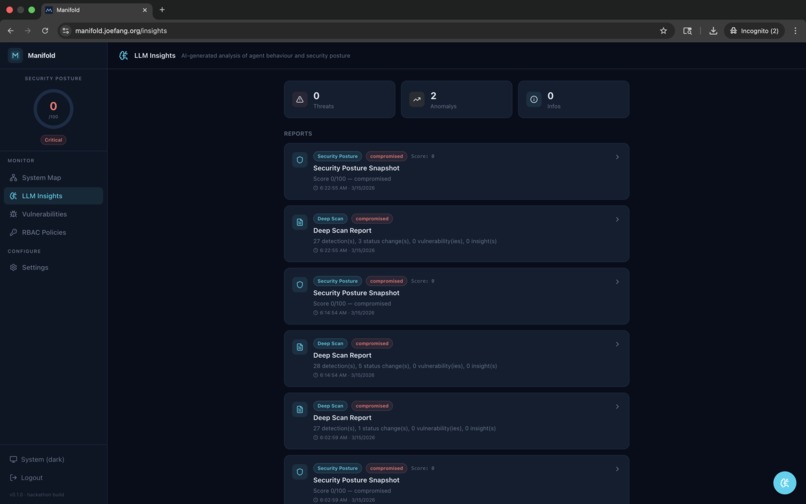
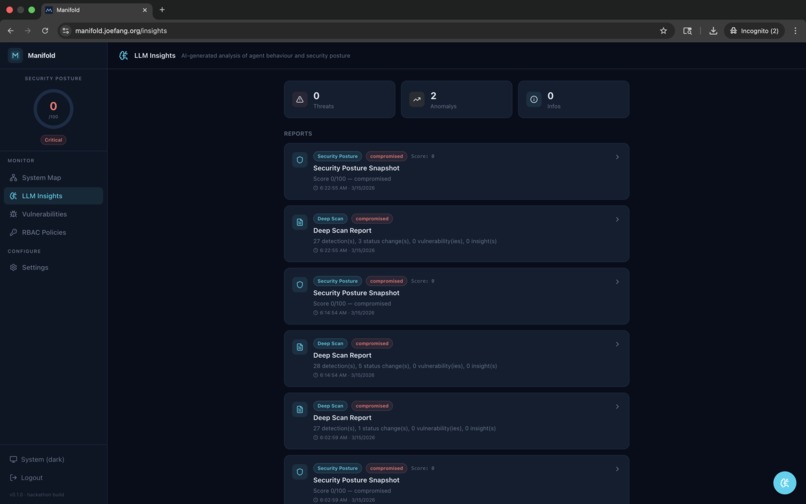
LLM Insights panel listing five AI-generated findings.
-
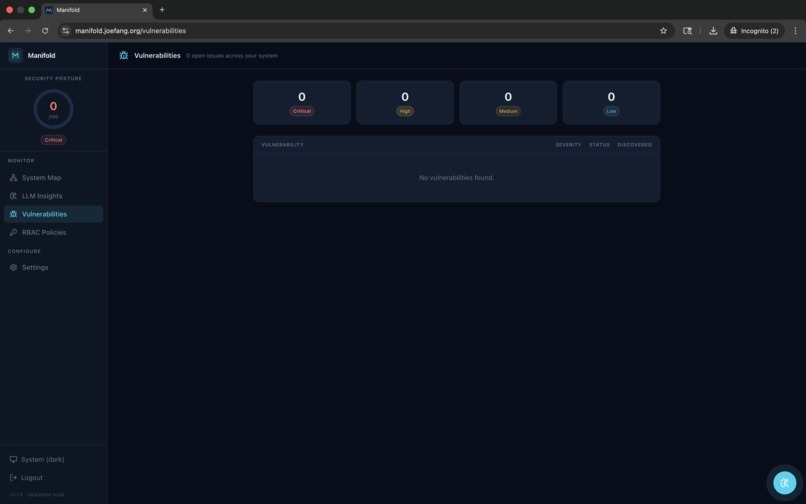
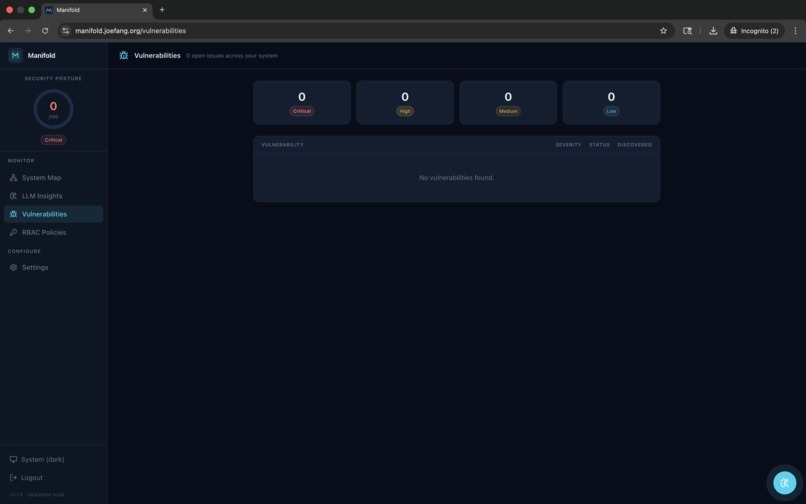
Vulnerabilities page showing four severity-tier counters.
-
System Map (Light Mode) showing a healthy seven-container topology
-
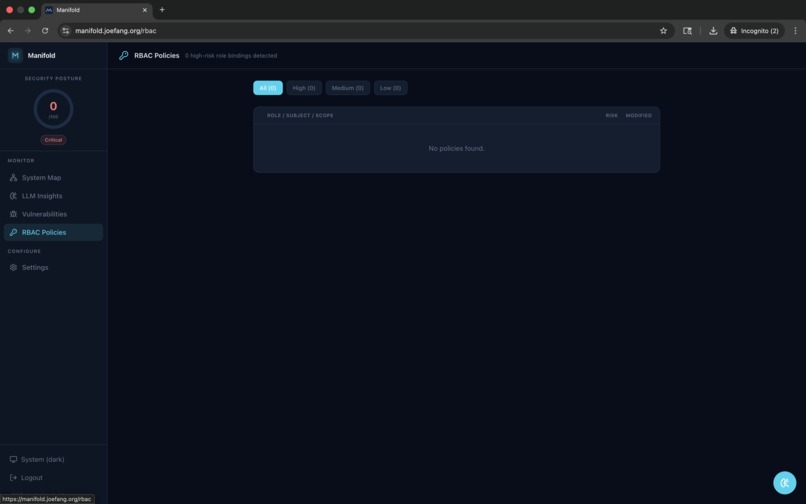
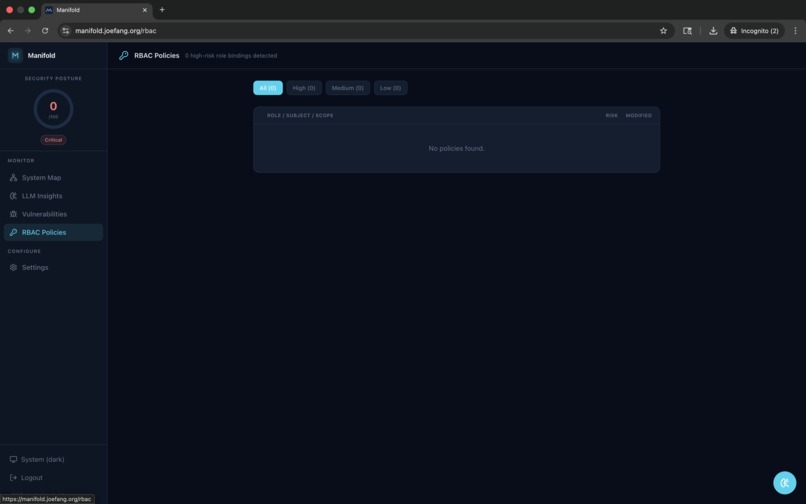
RBAC Policies page displaying a discovered role binding.
Inspiration
Vibe coding has gone mainstream. 41% of all code on GitHub is now AI-generated. 25% of YC's W25 batch is 95% AI-coded. Collins Dictionary named "vibe coding" its 2025 Word of the Year. Developers are shipping faster than ever — but nobody is watching what that code does once it's running in production.
The consequences are already here:
- Moltbook (Jan 2026) — An entirely vibe-coded social network for AI agents leaked 1.5 million API keys and 35,000 email addresses through a misconfigured Supabase database. The founder publicly stated he didn't write a single line of code.
- Lovable (Feb 2026) — A showcased app with 100,000+ views exposed 18,000 users' data. The AI had written authentication logic backwards, creating 16 vulnerabilities — 6 of them critical.
- Tea App (Jul 2025) — 72,000 images and 13,000 government IDs compromised. No authentication was ever configured.
- Base44 (Jul 2025) — An entire vibe coding platform was compromised through a single authentication bypass, exposing enterprise chatbots, HR systems, and PII stores.
Veracode's 2025 GenAI Code Security Report found that 45% of AI-generated code contains security flaws. Security firm Tenzai tested 5 major AI coding tools and found 69 vulnerabilities across just 15 apps — every single tool introduced SSRF, and zero apps had CSRF protection or security headers.
The existing security tooling wasn't built for this world. Static scanners like Snyk and SonarQube tell you "there's a vulnerability on line 47" — they can't see what happens at runtime. APM tools like Datadog monitor performance, not security. SIEM tools are enterprise-only and take months to configure.
We asked: what if your containers had a security analyst watching them 24/7 — one that reasons about threats the way a human would, but never sleeps?
That's Manifold.
What it does
Manifold is a Docker sidecar that monitors your containers and uses a LangGraph ReAct agent to find security issues in real time.
Unlike static code scanners, Manifold watches what your services actually do in production — the network connections they make, the processes they spawn, the resources they consume — and uses an LLM agent to reason across those signals like a security analyst would.
The Manifold dashboard provides five core views:
- System Map — Interactive topology showing all services, their connections, and live security status (Healthy, Warning, Compromised). You can see at a glance which containers are talking to each other and where the risks are.
- LLM Insights — AI-generated analysis with confidence scores. The agent categorizes findings as Threats, Anomalies, or Info, each with a confidence percentage and timestamp.
- Vulnerabilities — A structured vulnerability feed with severity levels (Critical, High, Medium, Low), CVE links, status tracking (Open, In-Progress), and remediation guidance.
- RBAC Policies — Automatically discovered role bindings between services, with risk scoring and token rotation tracking. Flags overdue rotations and overprivileged access.
- Settings — Configurable scan intervals, backend connection settings, and alert preferences.
How we built it
Data Collection: A cAdvisor sidecar runs alongside your containers and gathers metrics every 30 seconds — CPU, memory, network connections, running processes, and security configuration.
Backend: Python/FastAPI ingests the telemetry data and persists it in PostgreSQL. The API layer serves both the agent and the dashboard.
The ReAct Agent: This is Manifold's brain. Built with LangGraph and LangChain, it's a ReAct (Reasoning + Acting) agent powered by OpenAI that follows a five-step reasoning loop:
- Triage — Pull anomaly scores and overall security posture
- Investigate — Drill into metrics, network, and processes for flagged containers
- Correlate — Connect signals across containers (e.g., CPU spike + outbound connection + new process = crypto miner)
- Report — Store insights, vulnerabilities, and RBAC findings with evidence
- Classify — Assign overall risk: Healthy → Advisory → Warning → Critical
The agent has access to specialized tools: get_anomaly_scores, get_container_metrics, get_security_posture, get_network_connections, get_process_list, check_cve_database, store_insight, store_vulnerability, and more.
Frontend: React + TypeScript + Vite powers the Manifold dashboard. The System Map uses an interactive graph visualization showing service topology with color-coded security status. Real-time updates stream from the backend.
Deployment: Everything runs via Docker Compose. Add one line to your existing docker-compose.yml and Manifold starts monitoring — zero code changes required.
Challenges we ran into
- Signal correlation without false positives: A CPU spike alone means nothing. An outbound connection alone means nothing. But a CPU spike + new outbound connection to an unknown ASN + a spawned process not in the original image? That's a crypto miner. Teaching the agent to reason across these signals without crying wolf was our biggest challenge.
- ReAct agent loop management: LangGraph agents can get stuck in reasoning loops. We had to carefully design the tool set and prompt structure to ensure the agent converges on conclusions rather than endlessly investigating.
- Real-time topology visualization: Building the System Map that accurately shows service connections, updates live, and remains readable as the number of containers grows required significant iteration on the graph layout algorithm.
- Balancing scan frequency vs. performance: cAdvisor polling every 30 seconds provides good coverage without adding meaningful overhead, but we had to benchmark carefully to ensure the sidecar doesn't impact the containers it's monitoring.
Accomplishments that we're proud of
- Built a fully functional runtime security monitoring platform in 36 hours
- The ReAct agent successfully detects multi-signal attacks (prompt injection, data exfiltration, crypto mining) that no static scanner could find
- Real findings from the Manifold dashboard include: prompt injection via PDF ingestion, bulk embedding reads by a compromised agent, jailbreak via role-play prompts, and missing egress rate limiters on MCP bridges
- Zero-config deployment — one line in docker-compose, works with any stack
- Clean, production-grade dashboard with 5 fully functional pages
- The architecture is genuinely novel: no other tool combines a container sidecar + LLM reasoning agent for security monitoring
What we learned
- Runtime monitoring catches an entirely different class of threats than static analysis — they're complementary, not competing
- LLM agents are remarkably good at correlating signals across different data sources when given the right tools and reasoning structure
- The vibe coding security problem goes beyond bad code — it extends to misconfigured infrastructure, missing access controls, and overprivileged service accounts that AI-generated deployments routinely create
- Docker sidecars are an incredibly powerful deployment pattern for security tooling because they require zero changes to the monitored application
What's next for Manifold
Now: Docker Compose sidecar · LangGraph ReAct agent · Manifold dashboard · 5 pages · Real-time monitoring
Next: One-line install CLI · Kubernetes DaemonSet support · Auto-remediation (revoke roles, isolate containers automatically)
Vision: Community threat intelligence sharing · SOC2 compliance reporting · Custom detection rule marketplace
Built With
- caddy
- cadvisor
- chatgpt
- ci/cd
- claude
- containerization
- cybersecurity
- docker
- docker-compose
- fastapi
- gemini
- git
- github
- github-actions
- langchain
- langgraph
- llm
- openai
- postgresql
- pydantic
- python
- rbac
- react
- security
- sqlalchemy
- typescript
- vite


Log in or sign up for Devpost to join the conversation.