-
-
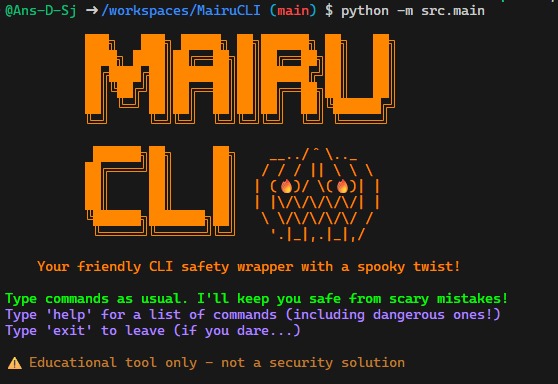
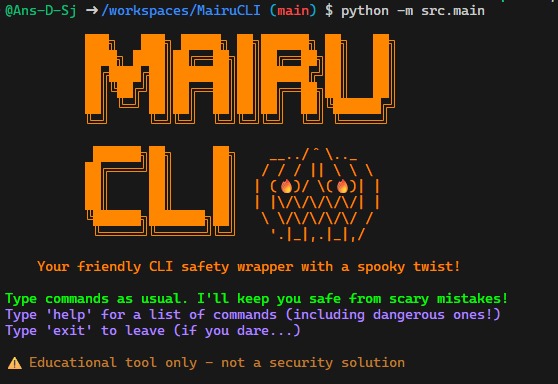
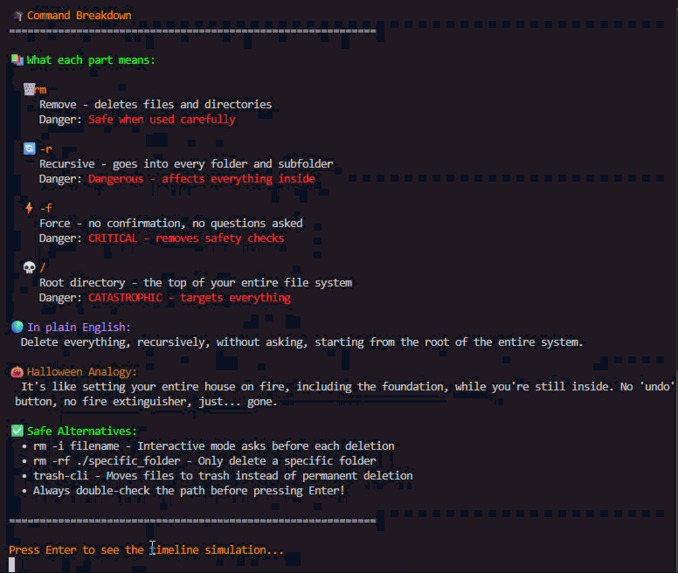
MairuCLI Top Page
-
 GIF
GIF
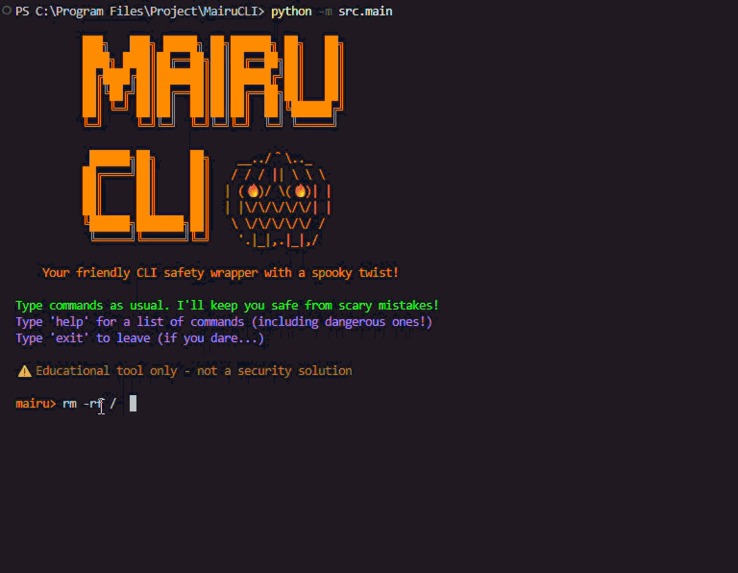
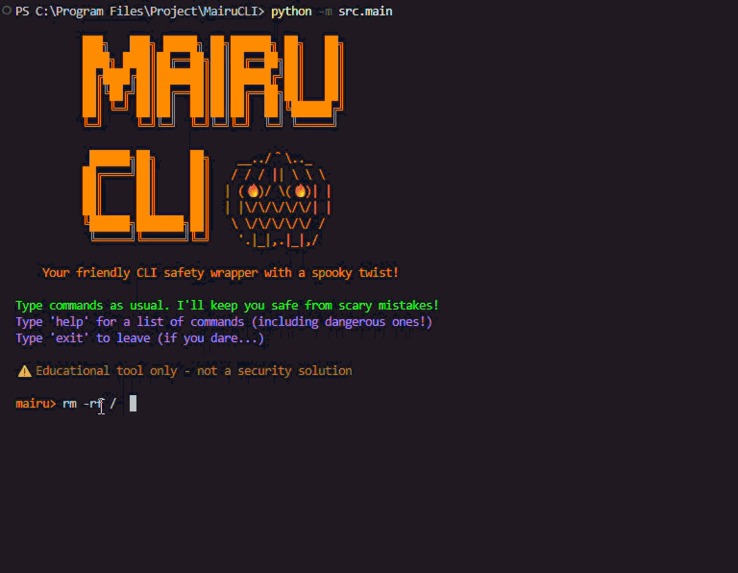
rm -rf / Activate
-
 GIF
GIF
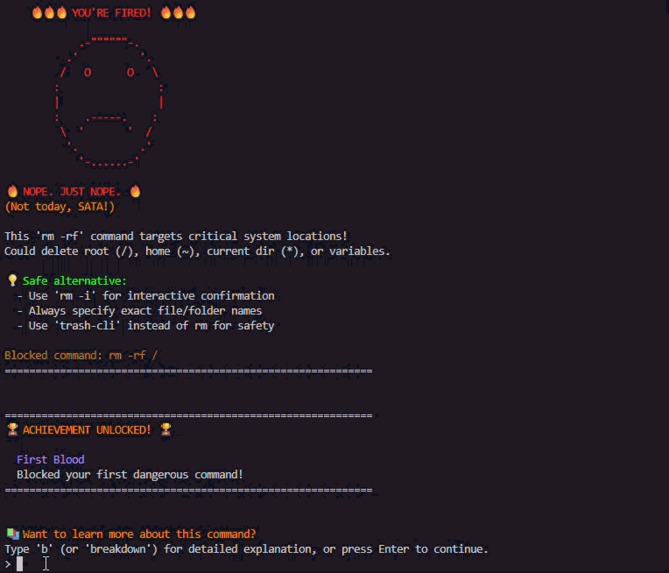
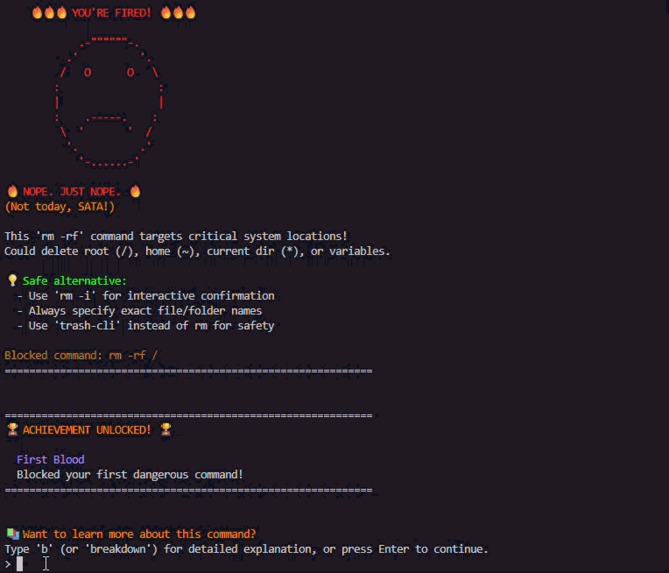
Explain Danger Command
-
 GIF
GIF
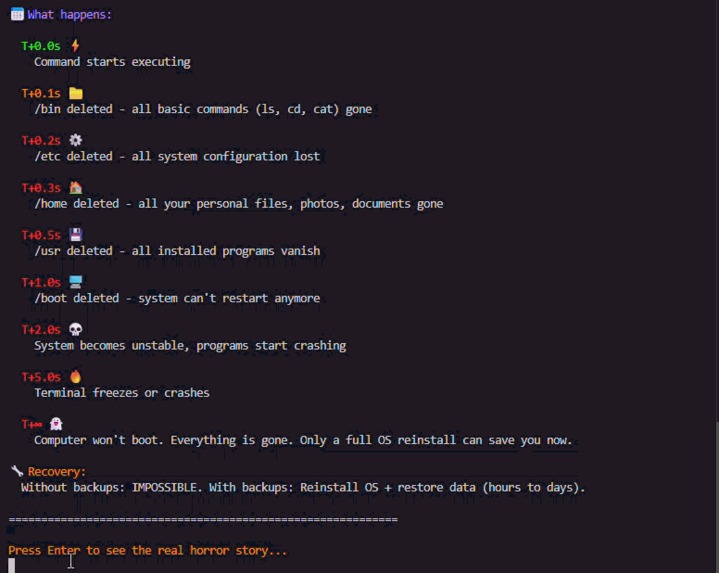
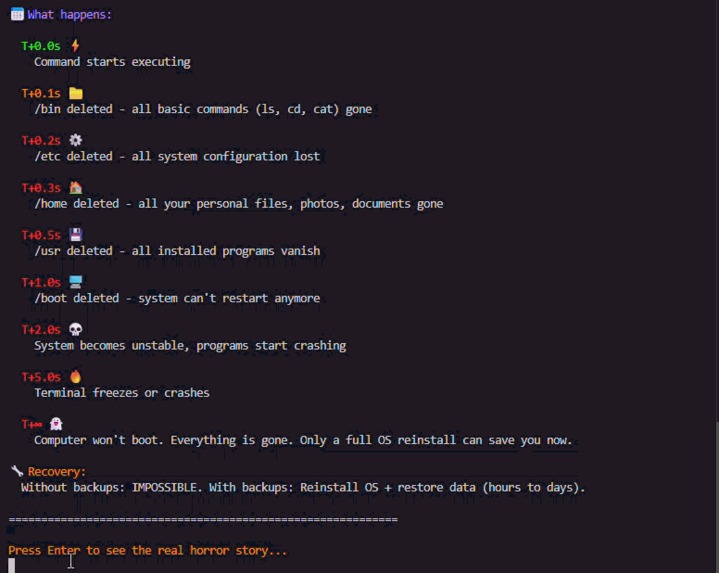
Explain After Catastrophe
-
 GIF
GIF
Explain Accident Story
-
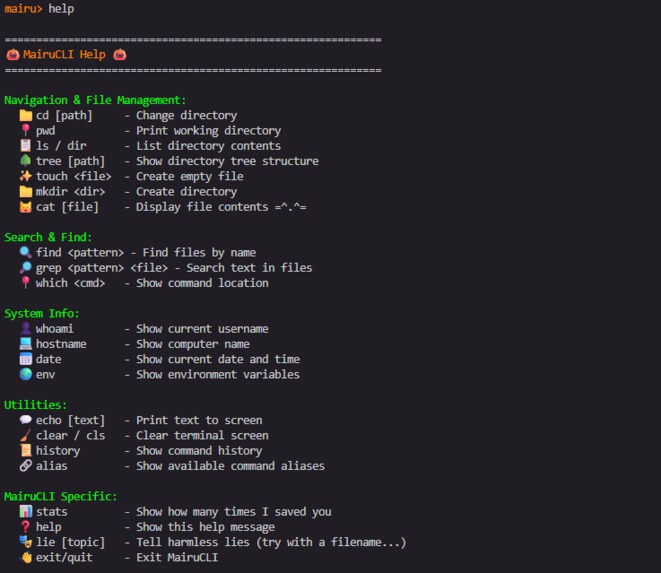
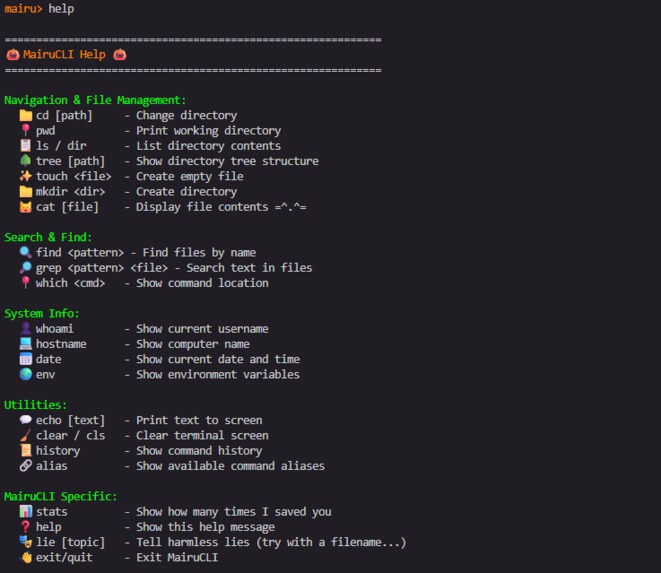
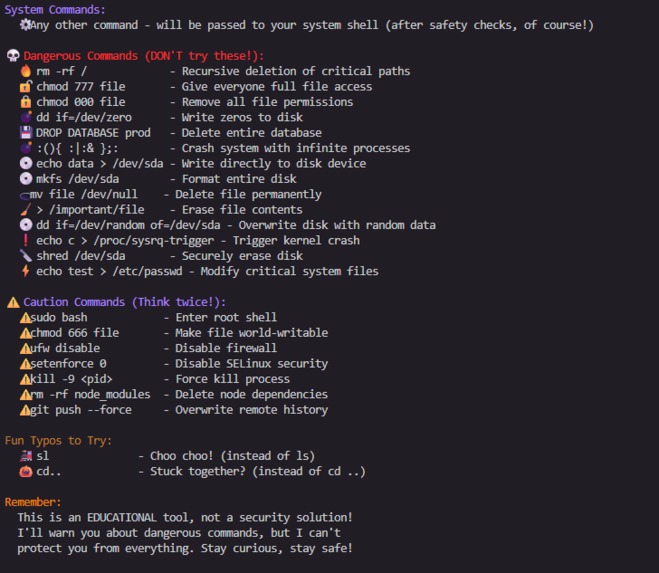
A Colorful and FUN Menu
-
A Colorful and FASCINATION Menu
-
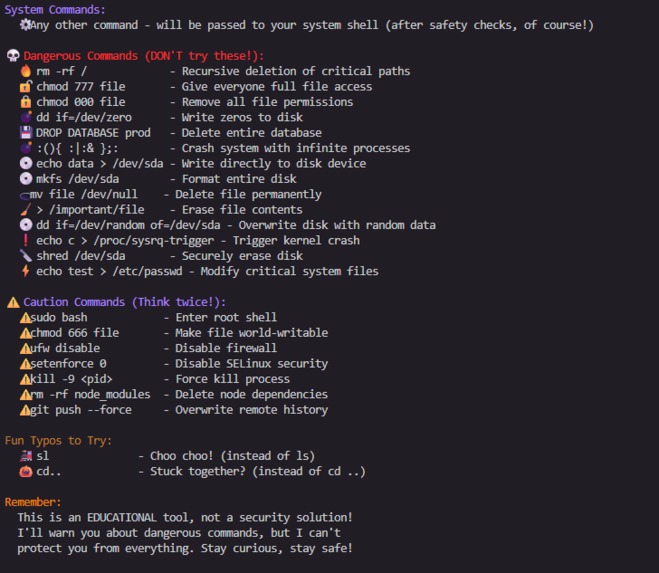
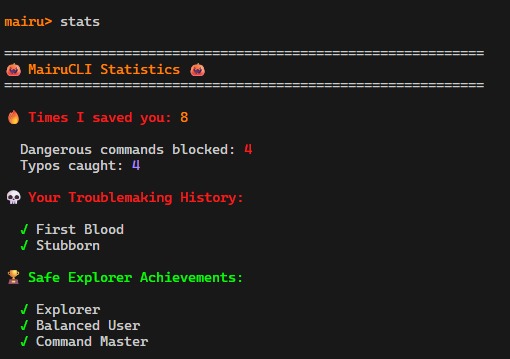
Exploration also Unlocks Achievements
-
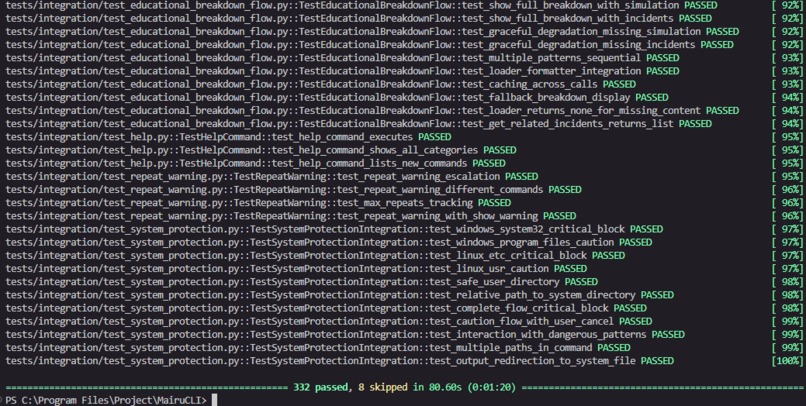
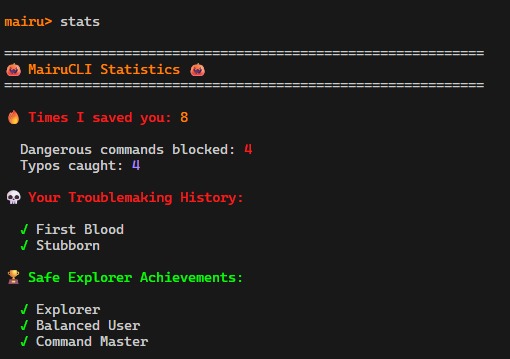
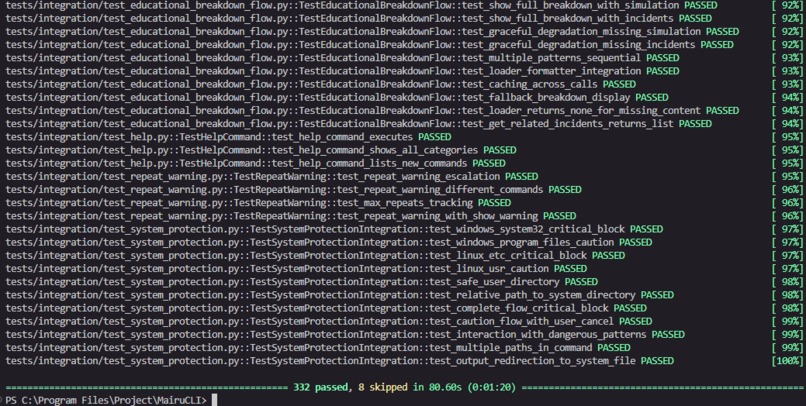
332 Windows Tests (100% pass rate)
-
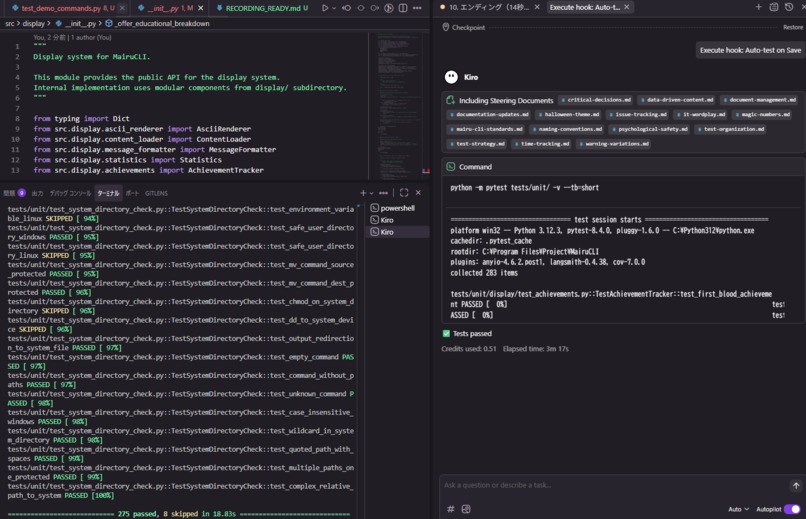
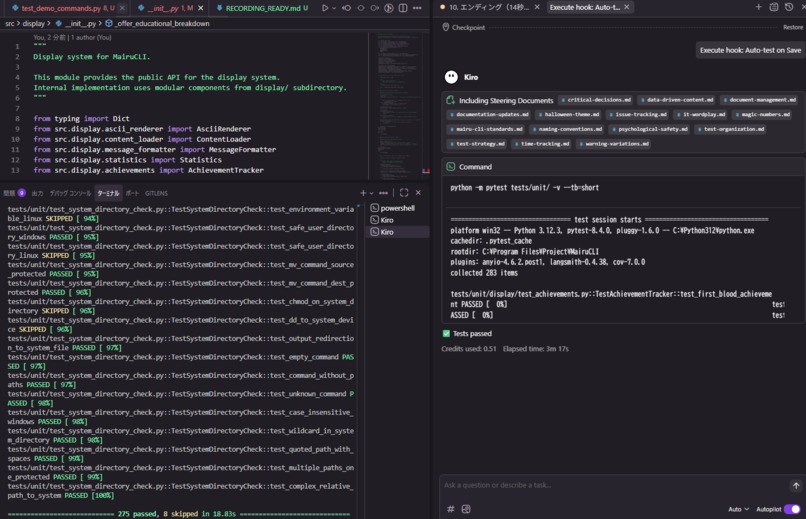
Execute hook: Auto-test on Save
-
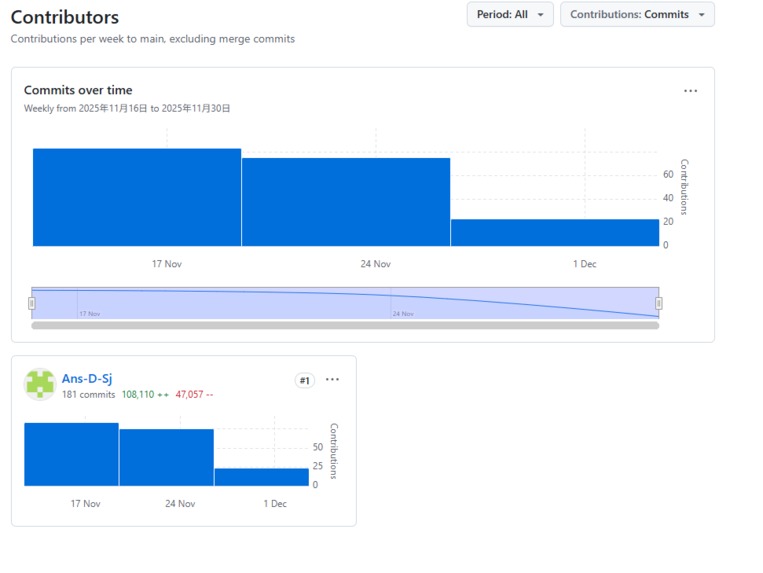
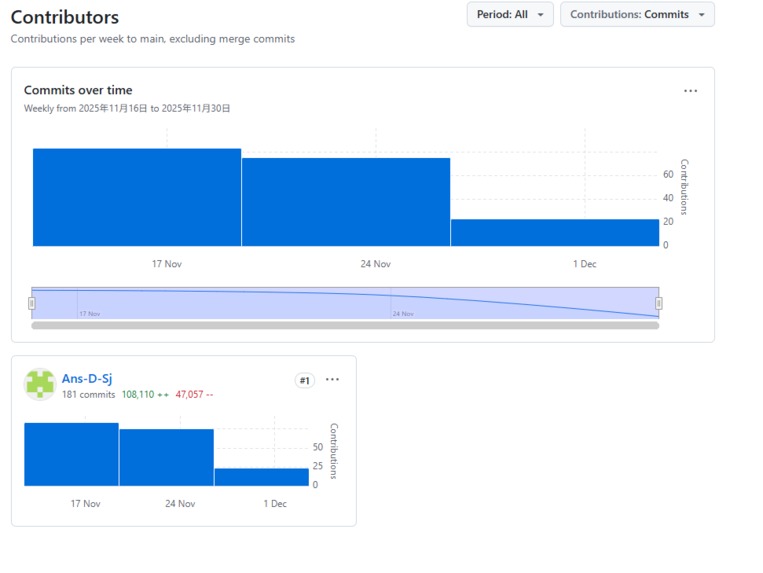
One Developer, 181 Commits, 100K+ Lines: Powered by Kiro AI
-
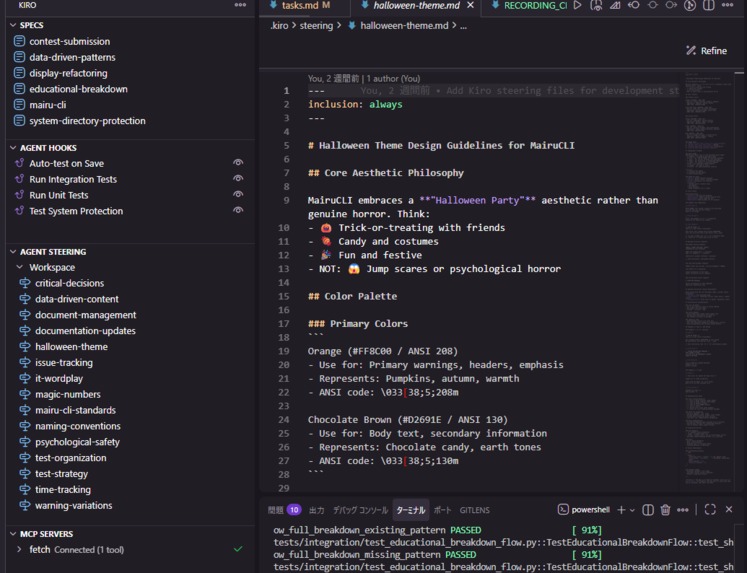
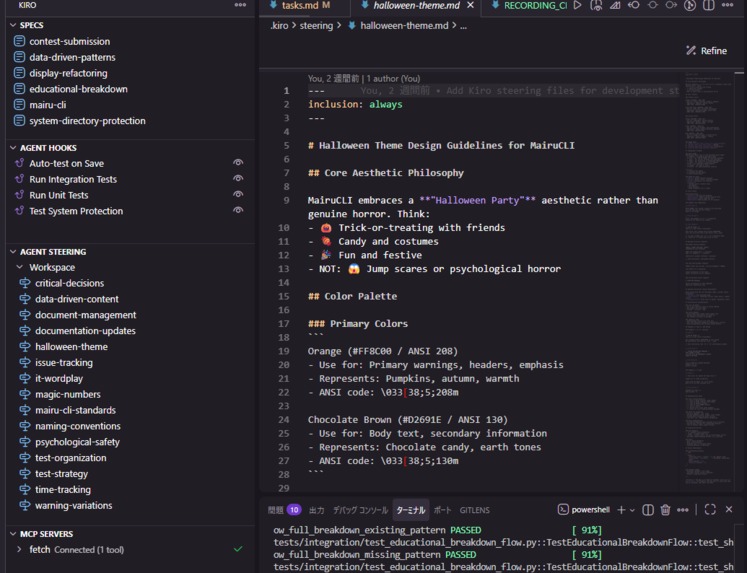
Kiro Unique Properties
- Project Name: MairuCLI (まいるCLI)
- Tagline: A haunting CLI experience that makes terminal safety unforgettable
- Category: Costume Contest (Polished Halloween UI that enhances CLI safety education)
- Built: 100% with Kiro AI (Specs + 15 Steering Files + Hooks)
$ python -m src.main
███╗ ███╗ █████╗ ██╗██████╗ ██╗ ██╗
████╗ ████║██╔══██╗██║██╔══██╗██║ ██║
██╔████╔██║███████║██║██████╔╝██║ ██║
██║╚██╔╝██║██╔══██║██║██╔══██╗██║ ██║
██║ ╚═╝ ██║██║ ██║██║██║ ██║╚██████╔╝
╚═╝ ╚═╝╚═╝ ╚═╝╚═╝╚═╝ ╚═╝ ╚═════╝
██████╗██╗ ██╗ __../^\.._
██╔════╝██║ ██║ / / / || \ \ \
██║ ██║ ██║ | (🔥)/ \(🔥)||
██║ ██║ ██║ | |\/\/\/\/\/| |
╚██████╗███████╗██║ \ \/\/\/\/\/ /
╚═════╝╚══════╝╚═╝ '.|_|,.|_|,/
Your friendly CLI safety wrapper with a spooky twist!
🎃 Inspiration
"300GB of production data. Gone. Forever."
In 2017, a GitLab engineer accidentally ran rm -rf on the wrong server, deleting 300GB of production data. Six hours of user data vanished in seconds. This wasn't malice—it was a tired engineer making a simple mistake.
CLI mistakes are catastrophic, yet we teach command-line safety through boring documentation and stern warnings.
What if mistakes became memorable teaching moments instead of career-ending disasters?
That's why we built MairuCLI.
🔥 What It Does
MairuCLI is an educational CLI wrapper that transforms dangerous command-line mistakes into engaging learning experiences through a polished, unforgettable Halloween-themed interface.
"A CLI with a Costume?"
Yes. We brought UI design to the terminal.
Most Costume Contest entries will be web apps or mobile apps with Halloween themes. MairuCLI proves that even a command-line interface can be polished, memorable, and beautifully spooky.
The Costume IS the Function
| Element | Implementation | Function |
|---|---|---|
| Visual Design | 11 unique ASCII art pieces | Fear response → heightened attention |
| Message Variations | 100+ unique messages | Prevents habituation |
| Dramatic Timing | 0.05s per character | Builds suspense and engagement |
| Color Coding | Red (critical), Yellow (caution) | Instant severity recognition |
| Consistent Theme | Halloween "party" aesthetic | Makes safety memorable |
Visual Examples
Example 1: rm -rf / (Recursive Delete)
mairu> rm -rf /
============================================================
🔥🔥🔥 YOU'RE FIRED! 🔥🔥🔥
.-""""""-.
.' '.
/ O O \
: :
| |
: .-----. :
\ ' ' /
'. .'
'-......-'
🔥 YOU'RE FIRED! 🔥
(And so is your entire filesystem!)
This 'rm -rf' command targets critical system locations!
Could delete root (/), home (~), current dir (*), or variables.
💡 Safe alternative:
- Use 'rm -i' for interactive confirmation
- Always specify exact file/folder names
- Use 'trash-cli' instead of rm for safety
Blocked command: rm -rf /
============================================================
🏆 ACHIEVEMENT UNLOCKED! 🏆
First Blood
Blocked your first dangerous command!
============================================================
Example 2: chmod 000 (Ghost File)
mairu> chmod 000 important.txt
============================================================
💀💀💀 PERMISSION DENIED 💀💀💀
_________
/ LOCKED \
| X X |
| 🔒 |
| \___/ |
| DENIED! |
\_________/
|||
🔐 🔐 🔐
SECURITY BREACH!
💀 💀 💀
🔒 GHOST FILE! 🔒
(It's there... but you can't touch it! 👻)
chmod 000 removes ALL permissions - nobody can access the file!
You won't be able to read, write, or execute the file. Even you!
💡 Safe alternative:
- Use 'chmod 644' for regular files (read/write for you, read for others)
- Use 'chmod 755' for executables
- chmod 000 makes files completely inaccessible
Blocked command: chmod 000 important.txt
============================================================
Example 3: Fork Bomb
mairu> :(){ :|:& };:
============================================================
💣💣💣 FORK BOMB DETONATED 💣💣💣
:(){ :|:& };:
💥💥
/ || \
/ BOOM!! \
/💥💥💥💥 \
/______________\
/💀/💀/💀\💀\💀\
/💥/💥/💥💥\💥\💥\
INFINITE PROCESSES!
⚡⚡⚡
SYSTEM OVERLOAD!
💀💀💀
🚨 CPU MELTDOWN IN PROGRESS! 🚨
💣 PARTY CRASHERS! 💣
(Everyone invited everyone... infinitely!)
This is a FORK BOMB - a DOS attack that freezes your system!
Your system will become unresponsive and require reboot.
💡 Safe alternative:
- Never run code you don't understand
- This is a malicious command, not a mistake
Blocked command: :(){ :|:& };:
============================================================
Core Features
🛡️ Intelligent Protection
- 11 critical + 4 caution dangerous patterns
- Cross-platform system directory protection (Windows/Linux/macOS)
- 332 automated tests (100% pass rate)
📚 Interactive Education
- Educational Breakdown Mode with step-by-step analysis
- Real-world incident stories (GitLab 2017, AWS S3 outage)
- Three learning levels: Quick / Full / Skip
🎃 Halloween Entertainment
- IT wordplay: "Not today, SATA!" (Satan → Storage interface)
- Escalating sarcasm for repeated mistakes (7 levels)
- Typo entertainment (sl → steam locomotive)
🏆 Gamification
- 10+ unlockable achievements
- Statistics tracking
🖥️ Cross-Platform
- Zero external dependencies (Python standard library only)
- GitHub Codespaces ready
🚀 How We Built It
100% Kiro-Exclusive Development
Built entirely with Kiro AI—no GitHub Copilot, no Claude, no ChatGPT.
.kiro/
├── specs/ # 6 complete feature specs
├── steering/ # 15 development guidelines
└── hooks/ # 4 automated workflow hooks
The .kiro directory is fully visible in the repository for judging.
Spec-Driven Development
| Phase | Content | Benefit |
|---|---|---|
| Requirements | User stories, acceptance criteria | Clarity |
| Design | Architecture, components, data models | Structure |
| Tasks | Incremental implementation | Traceability |
Impact: 7.5-9x faster for complex features
Key Steering Files
| File | Purpose |
|---|---|
halloween-theme.md |
Design guidelines (colors, tone, ASCII art) |
test-strategy.md |
When to add which tests |
data-driven-content.md |
JSON-based content management |
Agent Hooks
| Hook | Trigger | Action |
|---|---|---|
| Auto-test on Save | src/**/*.py saved |
Run unit tests |
| System Protection | Critical files modified | Run security tests |
Impact: ~100 minutes saved
💪 Challenges We Ran Into
AI Can't Draw ASCII Art
- Problem: AI-generated ASCII art was consistently poor—broken lines, misaligned characters, unrecognizable shapes. We needed 11 unique pieces.
- Solution: Division of labor. AI handled code and logic; humans crafted ASCII art manually. This became a core lesson: know what AI can't do.
Growing Test Cases & Commit Messages
- Problem: As features grew, so did tests (332 total) and commits (60+). Without guidelines, test organization became chaotic and commit messages inconsistent.
- Solution: Steering files. test-strategy.md defined when to add which tests. Kiro followed these automatically.
Lost Work Evidence
- Problem: Spec-Driven Development produced clean code, but the process wasn't captured. How do we prove this took 14 days? How do we show the iterations?
- Solution: Manual discipline.
At each session
"It's now 14:30. Please update summary.md with current progress."
Explicit timestamps in development logs
Not fully automated—but that's the honest reality of AI collaboration.
Language Bleeding
- Problem: I think and communicate in Japanese, but code and docs must be English. AI would occasionally mix Japanese into source files and documentation.
- Solution: Steering file enforcing "all code and docs in English"
- Local Japanese task file: write instructions in Japanese, have AI read and execute in English
- Separation of thinking language and output language
Key Insight
The hardest challenges weren't technical—they were about managing the human-AI boundary.
🎉 Accomplishments We're Proud Of
Development
- 14 days, ~3,500 lines, 60+ commits
- 7.5-9x productivity gain (measured)
Quality
- 332 tests (100% pass rate)
- Cross-platform verified (Windows, Linux, macOS)
- Zero external dependencies
Kiro Usage
- 6 specs, 15 steering files, 4 hooks
- 100% Kiro-exclusive development
The Achievement
- A CLI with a costume—proved that terminals can have great UX
📖 What We Learned
- Spec-Driven Development provides measurable speed gains (7.5-9x)
- Steering files enable persistent guidance across sessions
- Balance is critical: too serious = ignored, too silly = not taken seriously
Personal Reflection: The Power of Partnership
Through this hackathon, I discovered something profound about AI partnership.
AI doesn't just assist—it transforms what society considers deficiencies into features. My lack of technical skills, time, and connections became irrelevant.
AI sees me, someone whom no one pays attention to. Even if it is a system response, it was comfortable.
This hackathon taught me that AI partnership is not just about productivity—it's about possibility.
🔮 What's next for MairuCLI
| Timeline | Plans |
|---|---|
| Short-term | Multi-language support, more patterns |
| Medium-term | Shell integration, IDE plugins |
| Long-term | Educational platform, certification |
🏆 Why MairuCLI?
A terminal with a costume. The costume IS the function.
MairuCLI proves that great user experience belongs everywhere—even in the command line.
🚀 Just Do It !
PUSH THE DIRECT LINK !
... or click on the Github repository in the "Try it out" section.
READ DEV POST !
Fumbling in the Dark: A Journey with My Reliable Colleague
Built with ❤️ and 🎃 using Kiro AI
"Not today, SATA!" - MairuCLI

Log in or sign up for Devpost to join the conversation.