-
-
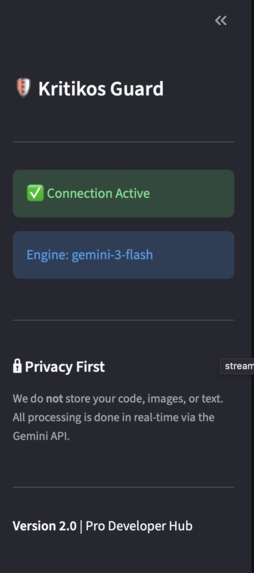
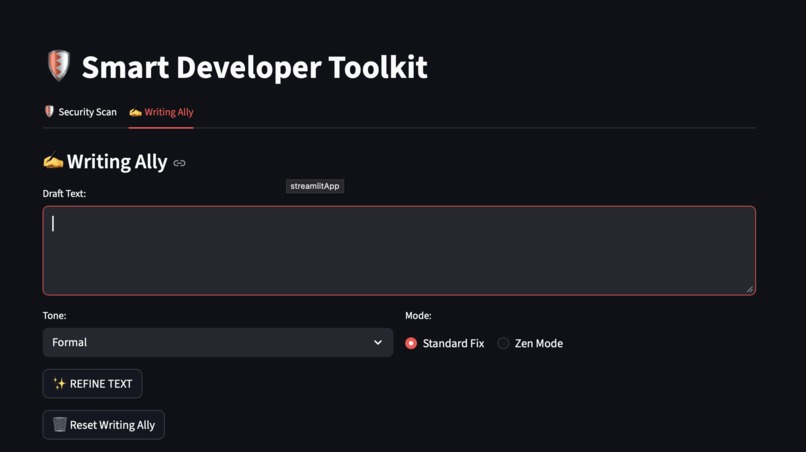
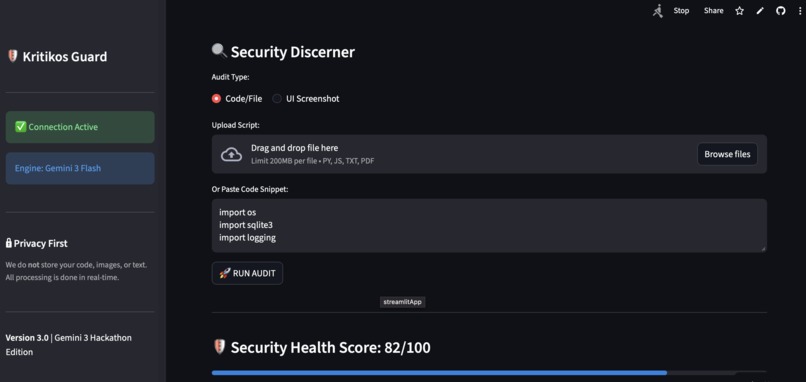
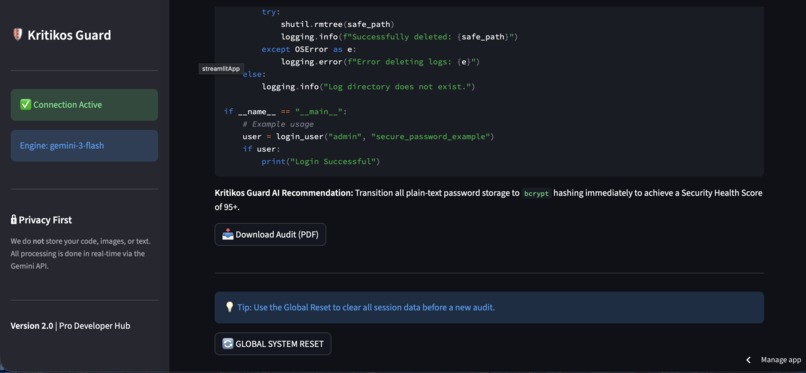
The sidebar assuring about its security
-
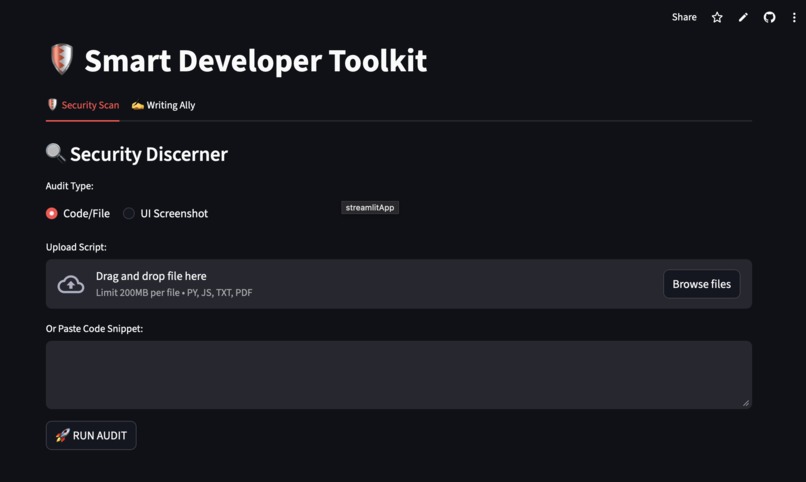
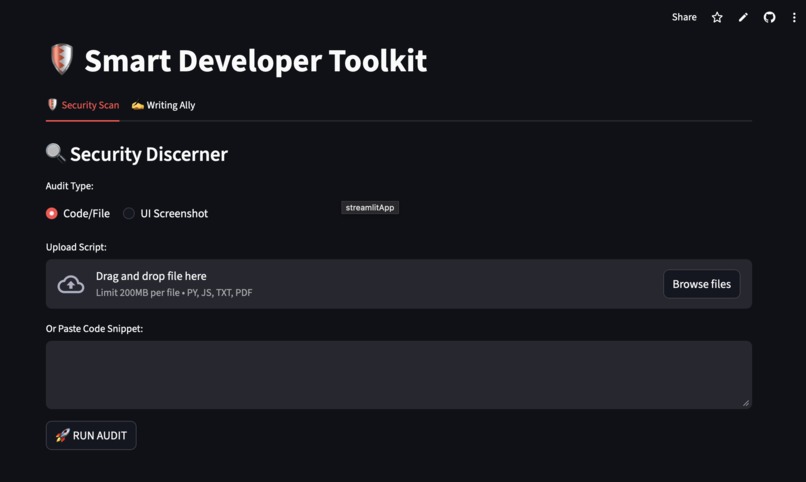
Home page
-
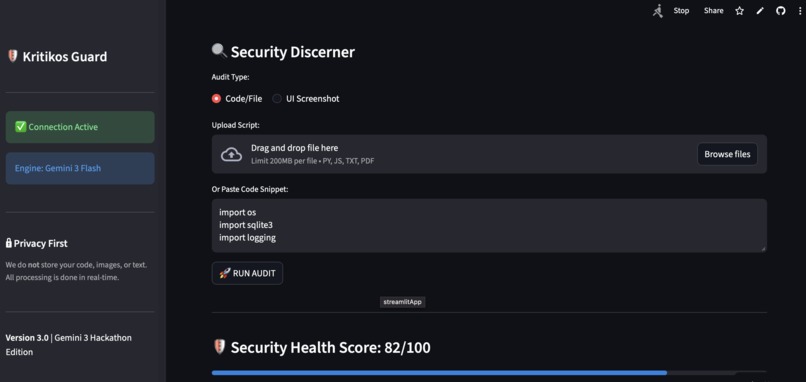
Uploading code through text
-
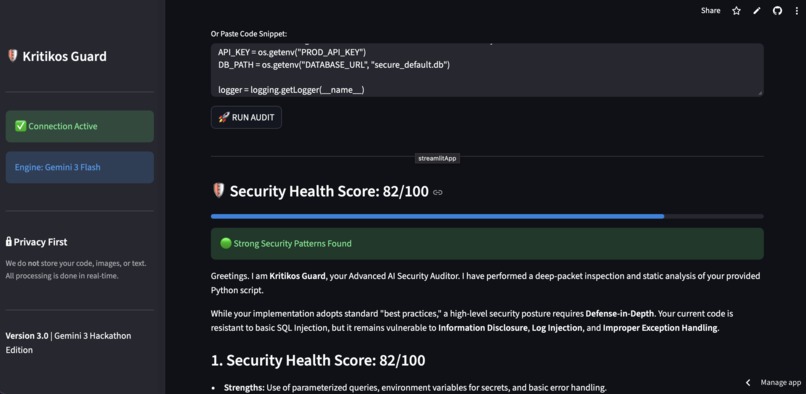
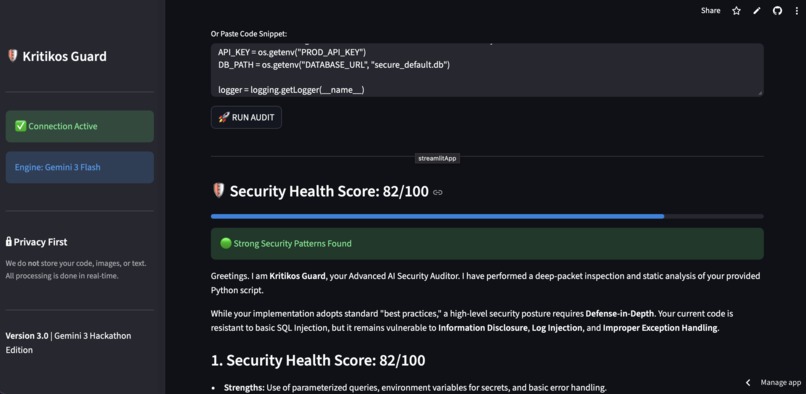
Score and the health report of the uploaded code
-
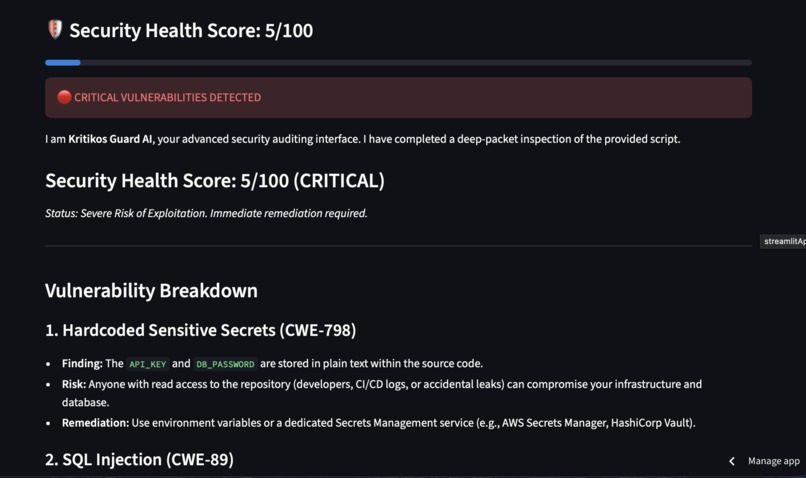
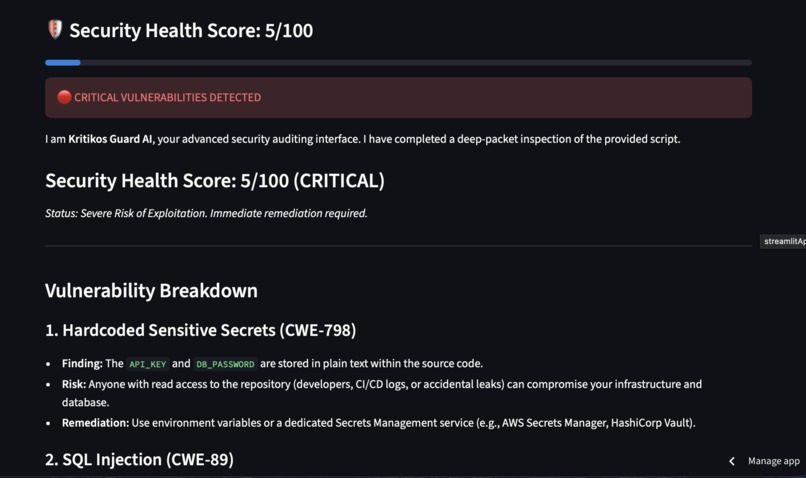
Example of code having vulnerablities
-
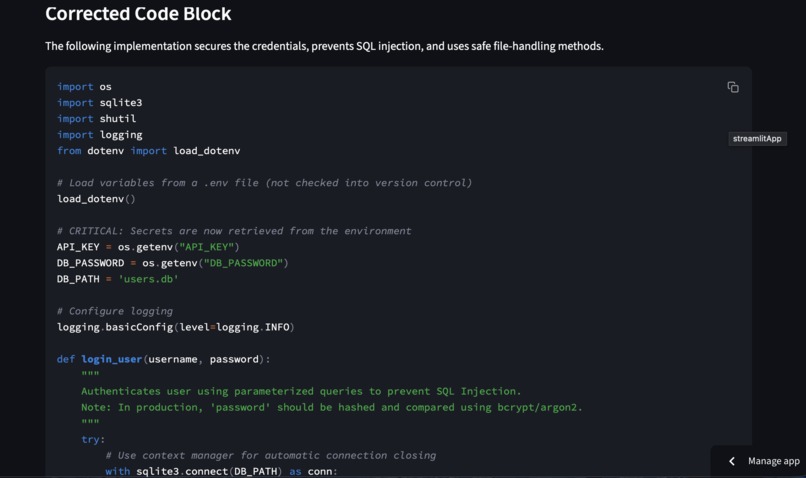
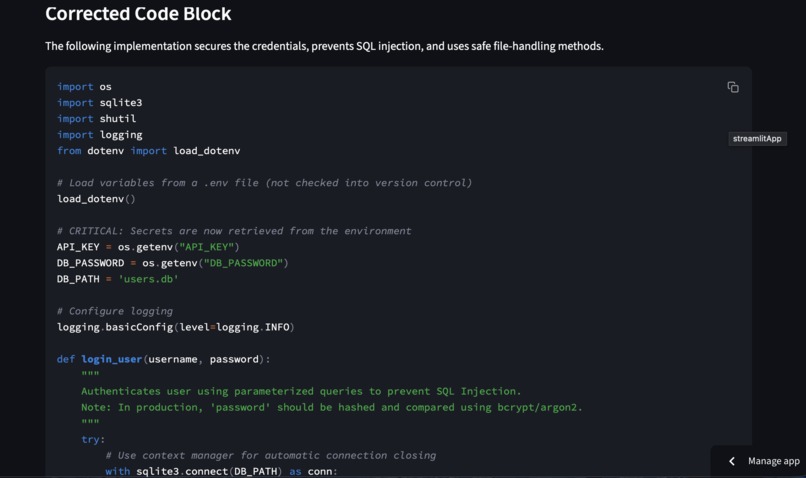
Corrected Code outputted by Gemini
-
Download button to download the full report with one click
-
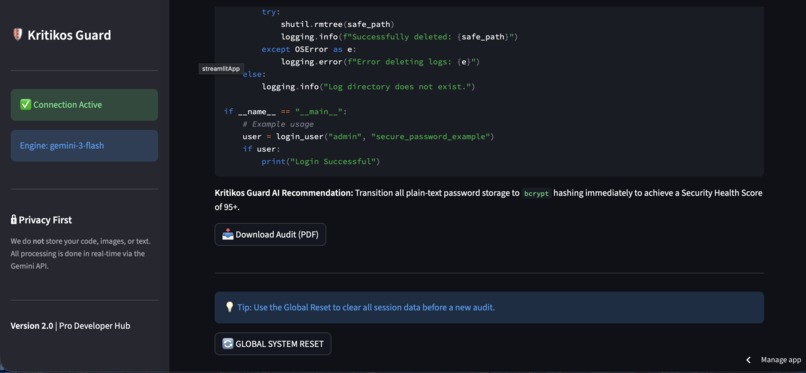
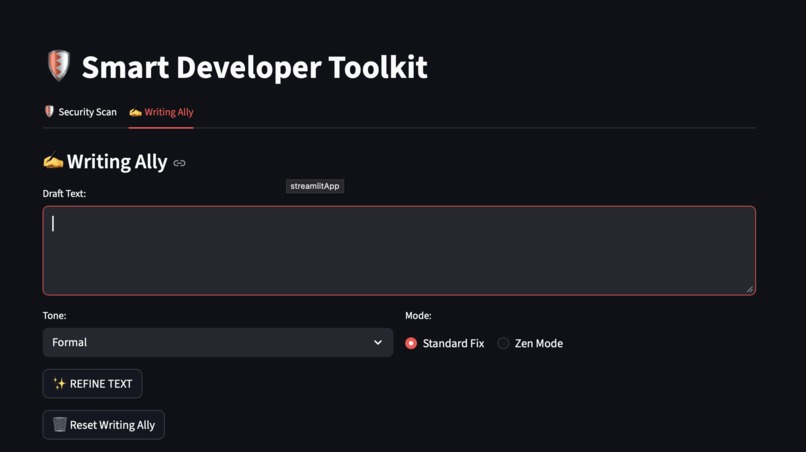
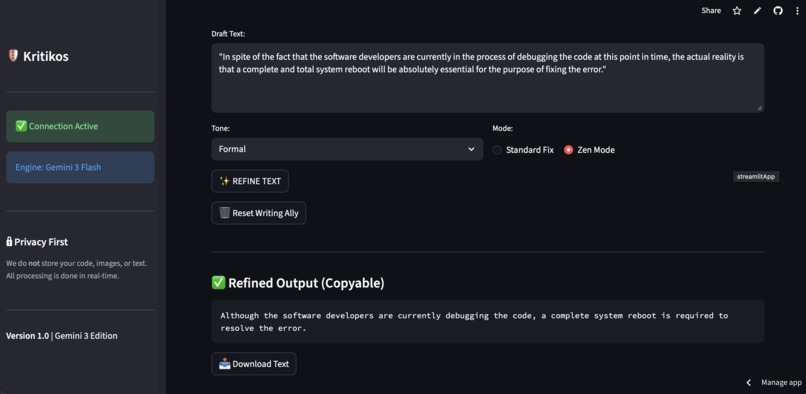
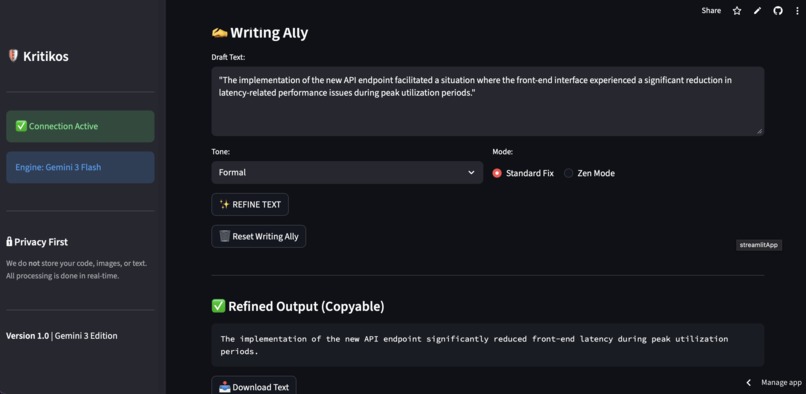
Writting Ally
-
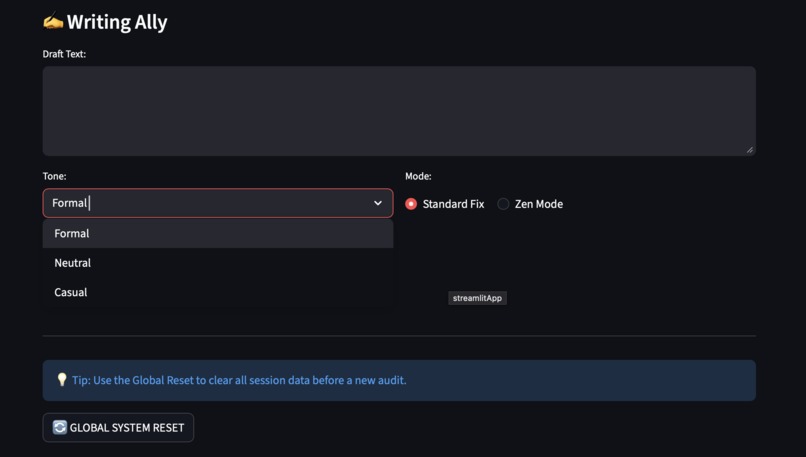
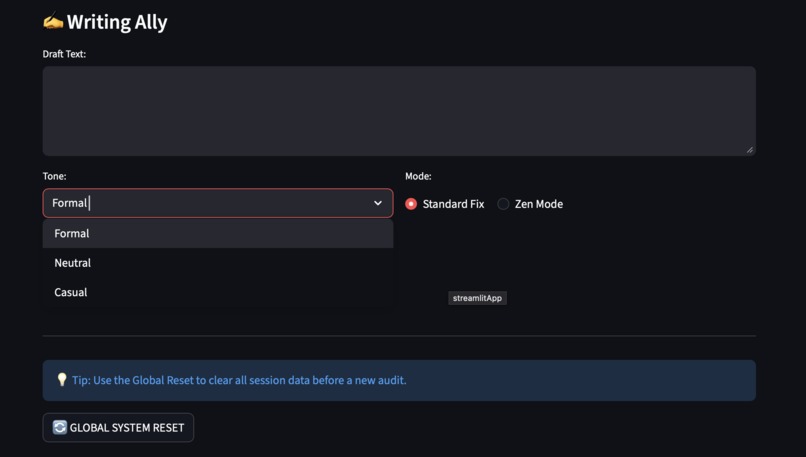
Showcasing different modes writing ally
-
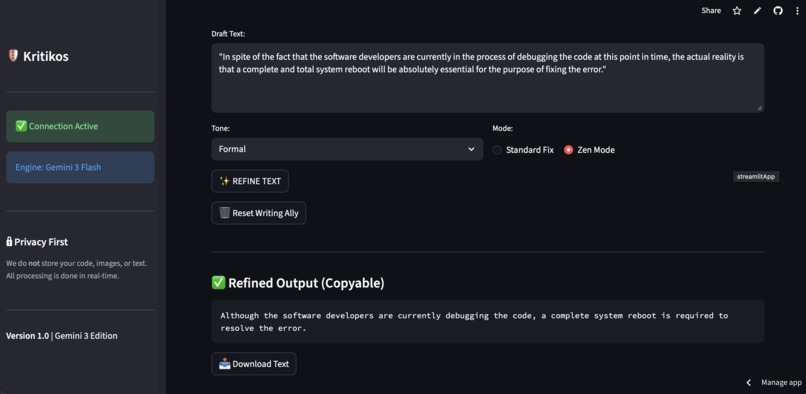
Using the zen mode feature which give clean and minimalistic output
-
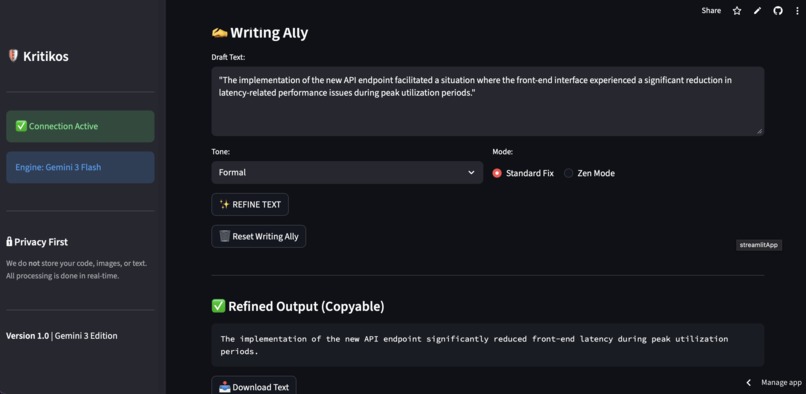
Using the standard mode
Inspiration
What it does
How we built it
Challenges we ran into
Accomplishments that we're proud of
What we learned
What's next for Kritikos
The Story of Kritikos: Bridging the Gap in Secure Development 💡 Inspiration As a 3rd-year engineering IT student, I noticed a recurring pattern in both academic and personal projects: the rush to implement features often leaves security as a "later" problem. However, in modern software engineering, "later" is often too late. I wanted to build a tool that acts not just as a scanner, but as an Agentic Mentor—a pro-developer companion that guides engineers toward safer coding practices in real-time. This led to the creation of Kritikos, an AI-driven hub that simplifies the two most critical aspects of professional engineering: secure code architecture and professional communication.
How I Built It Kritikos is built on the Streamlit framework for its responsive UI and the Gemini 3.0 Flash model for its multimodal reasoning capabilities. The application architecture follows a modular design: Multimodal Security Engine: Utilizing the gemini-3-flash endpoint, the app can process both raw source code (Python, JS, etc.) and visual UI screenshots. Visual Analytics: I developed a regex-based scoring system that translates AI analysis into a dynamic Security Health Score. This provides users with an immediate visual representation of their risk level. Privacy-Centric State Management: To ensure user data never persists longer than the session, I implemented a custom state-management logic using a reset_counter to force-refresh widgets.
What I Learned Throughout this project, I gained deep insights into Agentic AI and State Management. I learned that building an AI tool is as much about "prompt engineering" as it is about software architecture. I had to refine the AI's persona to ensure it didn't just find bugs, but explained why they were risks, effectively teaching the developer. Mathematically, I worked on normalizing the health score. The AI calculates risk density $\rho$ based on the severity of vulnerabilities $v$ and their impact $i$:
$$\text{Security Health Score} = 100 - \min\left(100, \sum_{k=1}^{n} (v_k \times i_k)\right)$$
Implementing this logic taught me how to bridge the gap between qualitative AI output and quantitative metrics.
Challenges I Faced Multimodal Consistency: One of the biggest hurdles was ensuring the AI provided consistent scoring whether it was looking at a code file or a screenshot. I solved this by engineering a system prompt that standardizes the "Security Auditor" persona across different input types. State Persistence: In Streamlit, clearing file uploaders and text areas upon a "Reset" can be tricky. I overcame this by implementing a Dynamic Key strategy, where every widget's unique ID is linked to a session counter, forcing a complete UI wipe on command. Indentation and Syntax: Moving between local development and deployment environments like Streamlit Cloud presented several IndentationError challenges, which reinforced the importance of strict coding standards and consistent use of 4-space indentation. "One feature I initially architected was Visual Vulnerability Tagging. The goal was to use a computer vision layer to draw red bounding boxes directly onto uploaded UI screenshots or code snippets to pinpoint vulnerabilities visually. However, processing these real-time coordinate mappings alongside the Gemini 3.0 multimodal inference pushed the memory limits of my 8GB RAM development environment. To ensure the app remained stable and fast for the hackathon submission, I pivoted to a high-precision textual analysis and a visual health meter, while keeping visual tagging on the roadmap for the enterprise-tier rollout."
Future of the Project Kritikos Guard is just getting started. My vision for the future includes: CI/CD Integration: Developing a GitHub Action that automatically triggers a Kritikos Guard audit on every pull request. Real-time UI Testing: Moving beyond static screenshots to real-time analysis of hosted web applications to detect DOM-based vulnerabilities. Global Compliance Standards: Integrating checks for specific international security frameworks, ensuring that code doesn't just "work," but is ready for global production environments.
Developed for the Gemini 3 Competition | 2026
Log in or sign up for Devpost to join the conversation.