-
-
-

It visualizes the core concept: Constitutional Token Governance for AI Agents, bridging Auth0 Token Vault with ACGS MACI Governance.
-
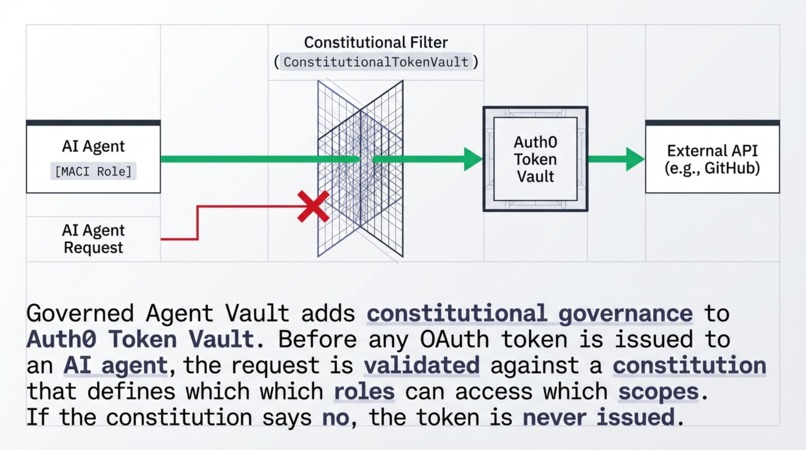
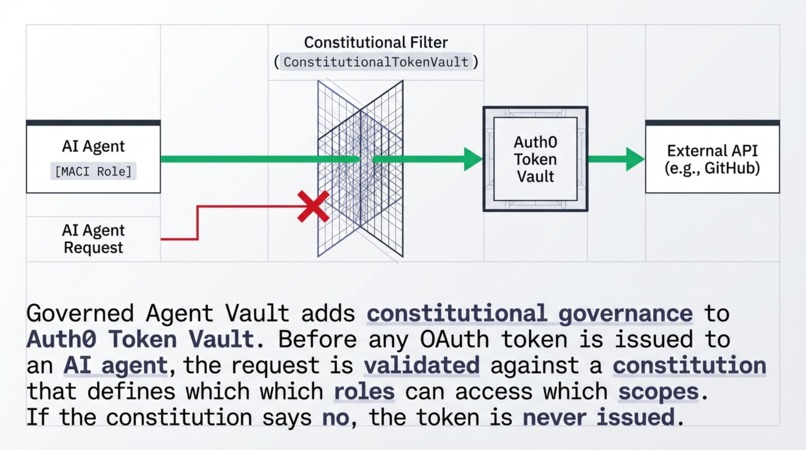
before reaching the Auth0 Token Vault and finally the External API. If the constitution denies the request (red X), no token is issued.
-
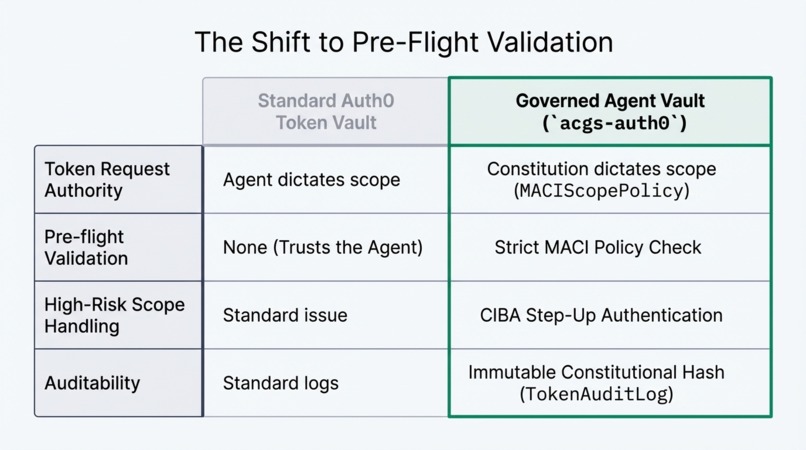
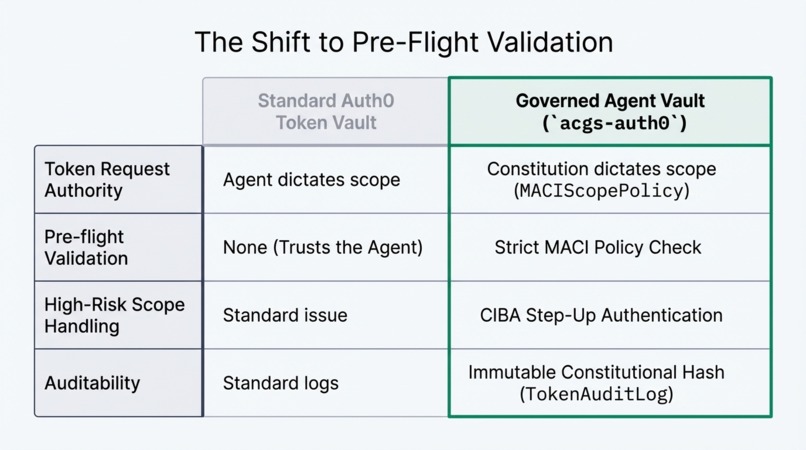
Auth0 Token Vault (where the agent dictates scope) vs. Governed Agent Vault (where the constitution dictates scope via MACIScopePolicy).
-
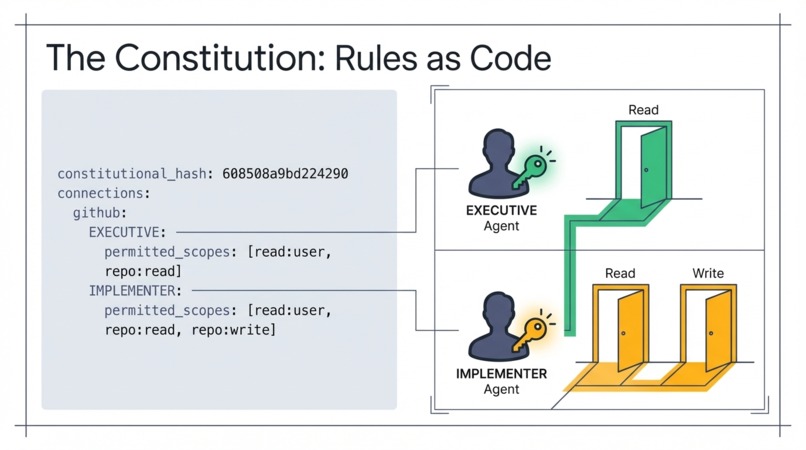
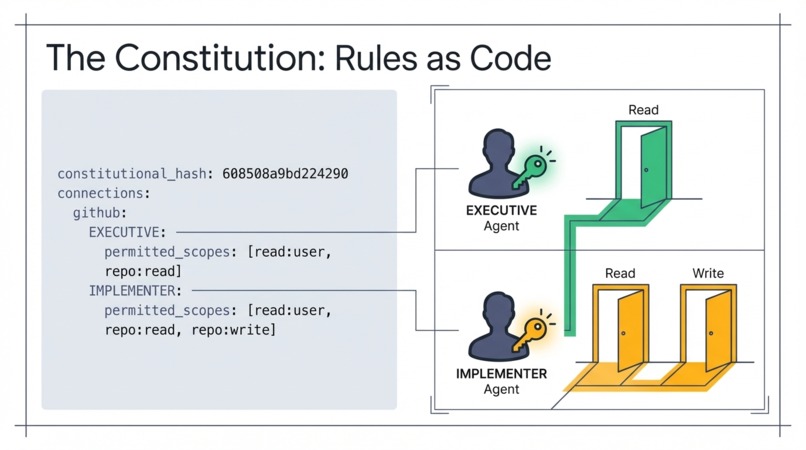
"EXECUTIVE" agents have restricted 'Read' access, while "IMPLEMENTER" agents are granted both 'Read' and 'Write' access based on roles.
-
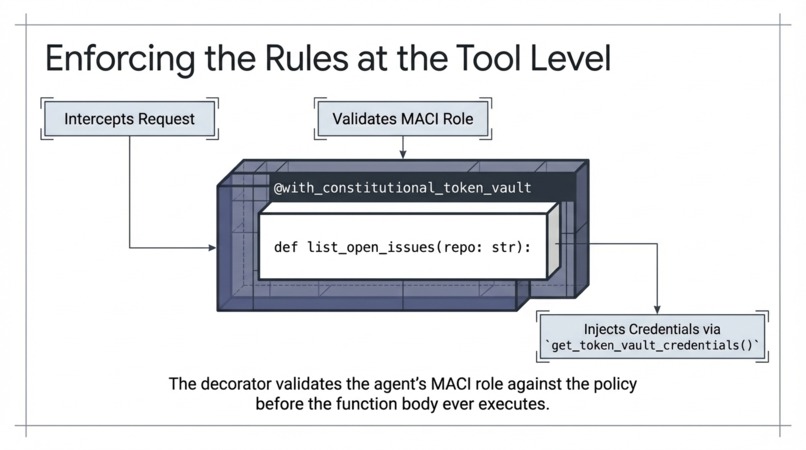
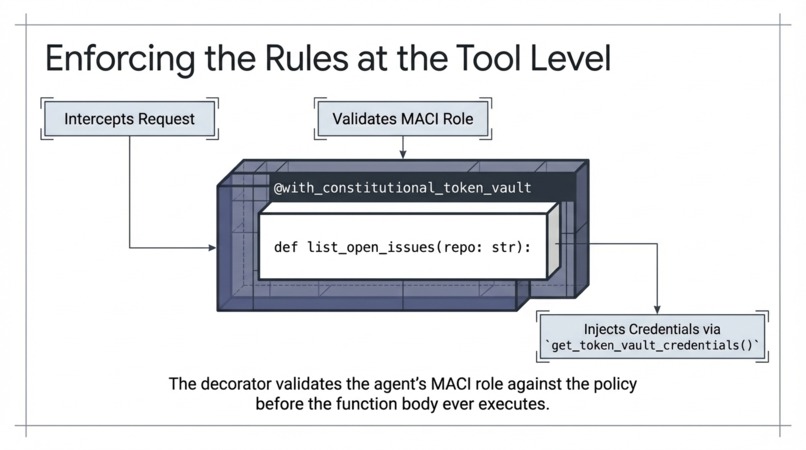
Illustrates how the decorator intercepts tool requests to validate MACI roles before credentials are ever injected into the function body.
-
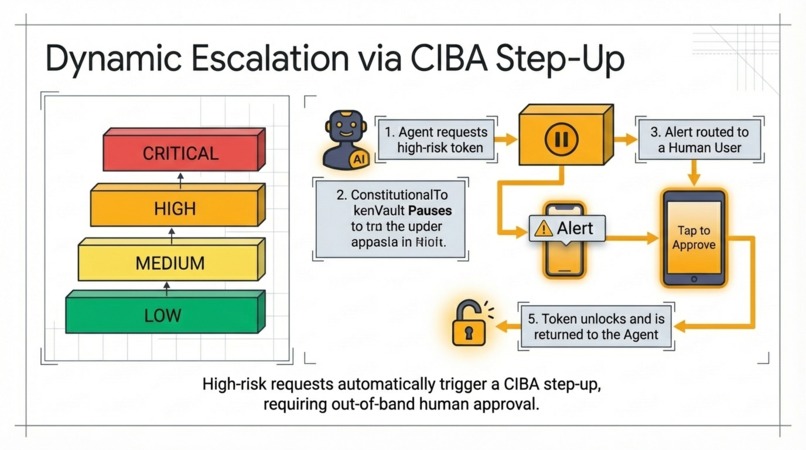
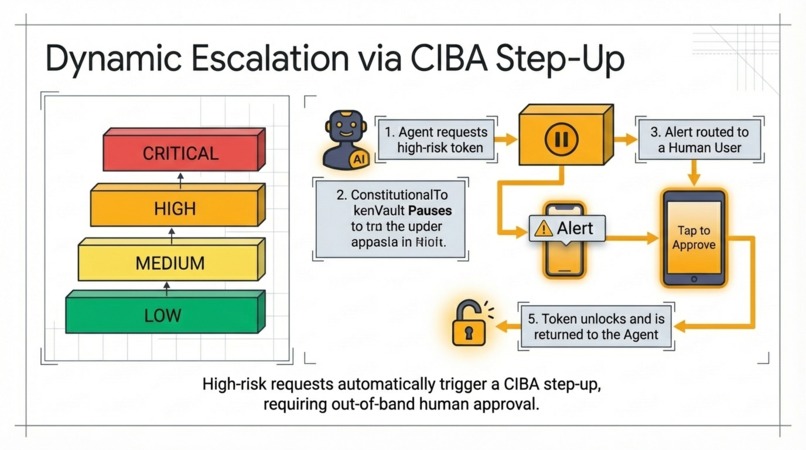
An agent requests a high-risk token, the vault pauses and routes an alert to a human user's mobile device for a "Tap to Approve" validation.
-
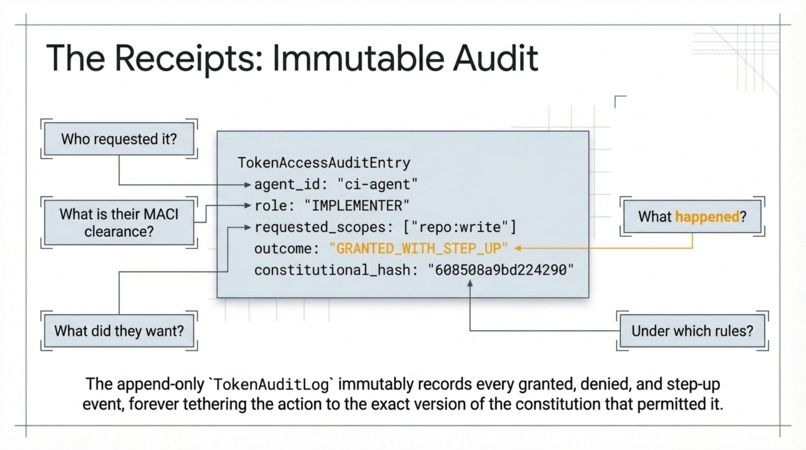
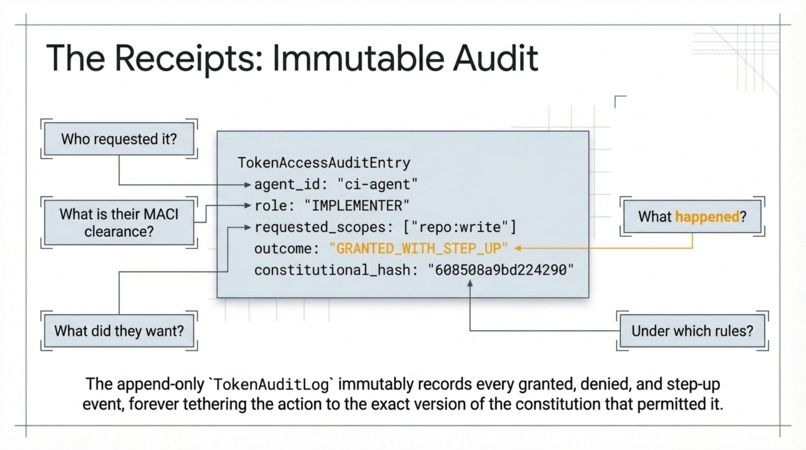
Who requested it (agent_id), their MACI clearance (role), what they wanted (scopes), and the result (outcome) tied to the immutable
-
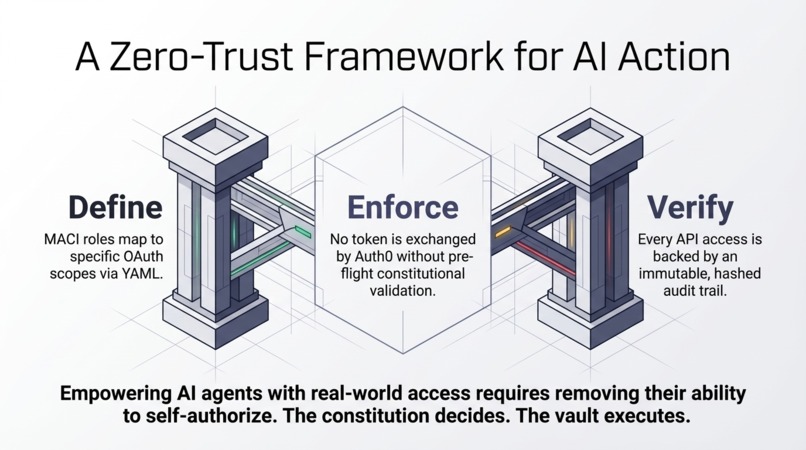
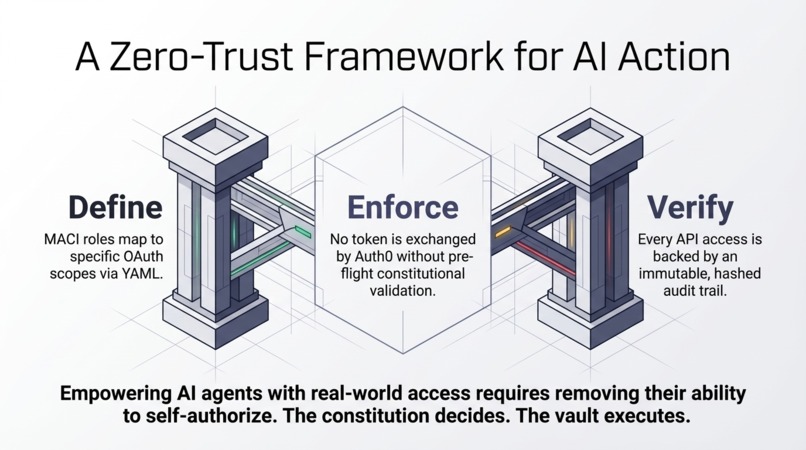
summarizing the three pillars: Define (MACI roles to YAML), Enforce (Pre-flight validation), and Verify (Immutable hashed audit trail).
Inspiration
OAuth scopes tell you what an API can do. But when AI agents act on behalf of users, you need a higher-level policy layer that answers: should this agent use these credentials right now?
We built Governed Agent Vault to answer that question with a constitutional governance framework.
What it does
Governed Agent Vault adds a constitutional policy layer between AI agents and Auth0 Token Vault. Before any OAuth token is issued:
- The agent's request is validated against a YAML-defined constitution
- MACI role separation (Executive/Judicial/Implementer) determines which scopes each agent type can access
- High-risk scopes automatically trigger CIBA step-up approval
- Every decision (granted, denied, step-up) is recorded in an immutable audit trail
- If the constitution says no, the token is never issued
How we built it
- acgs-auth0 (Python, published on PyPI) bridges Auth0 Token Vault with ACGS constitutional governance
- MACIScopePolicy defines per-connection, per-role scope permissions in YAML
- ConstitutionalTokenVault wraps Token Vault's RFC 8693 token exchange with pre-flight constitutional validation
- FastAPI demo app with interactive UI showing 6 governance scenarios across GitHub, Google, and Slack
- Built on acgs-lite, our constitutional AI governance engine (50K+ tests, 10 packages)
Challenges we ran into
Mapping the MACI constitutional governance model to OAuth scope hierarchies. OAuth scopes are flat strings, but governance needs risk levels, role permissions, and escalation paths. We solved this with a declarative YAML policy format.
What we learned
Auth is necessary but not sufficient for AI agent safety. You need a policy layer controlling what agents are allowed to do based on role, risk level, and organizational rules. Token Vault + constitutional governance is the right combination.
What's next
- Production deployment with real Auth0 Token Vault token exchange
- Integration with LangGraph and Vercel AI SDK
- EU AI Act Article 14 human oversight via CIBA step-up
- Multi-tenant constitutions for different organizational units
Built With
- acgs-lite
- auth0
- fastapi
- maci-governance
- oauth2
- python
- token-vault

Log in or sign up for Devpost to join the conversation.