-
-
Landing Page
-
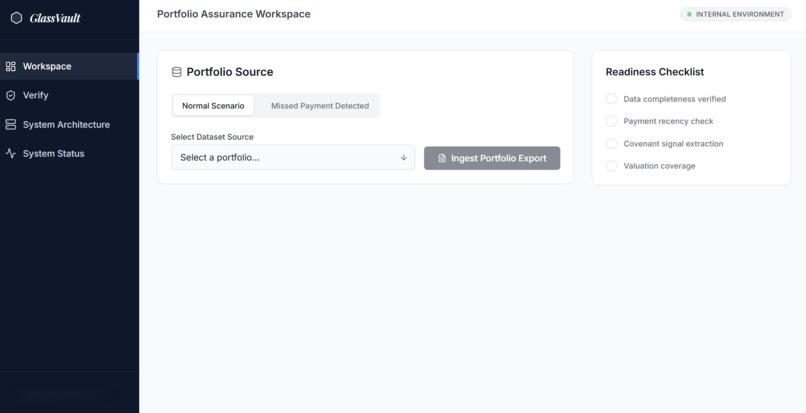
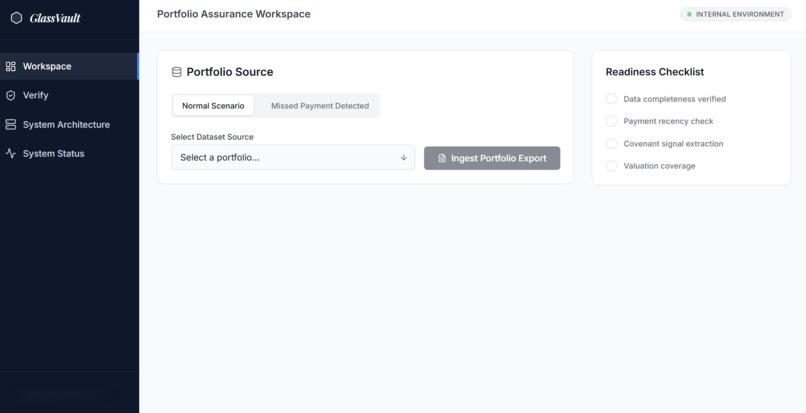
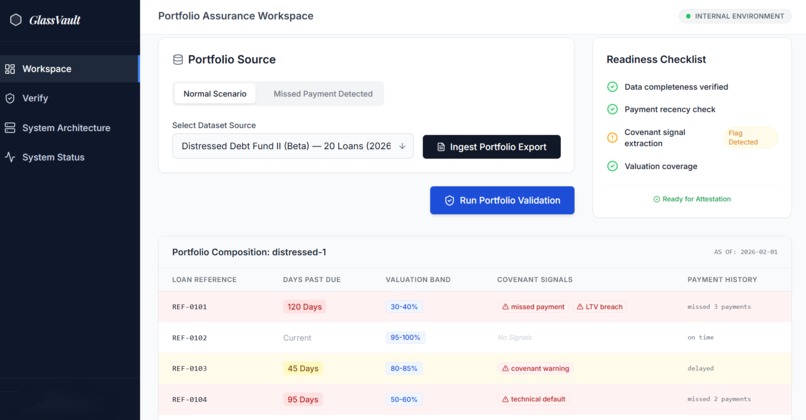
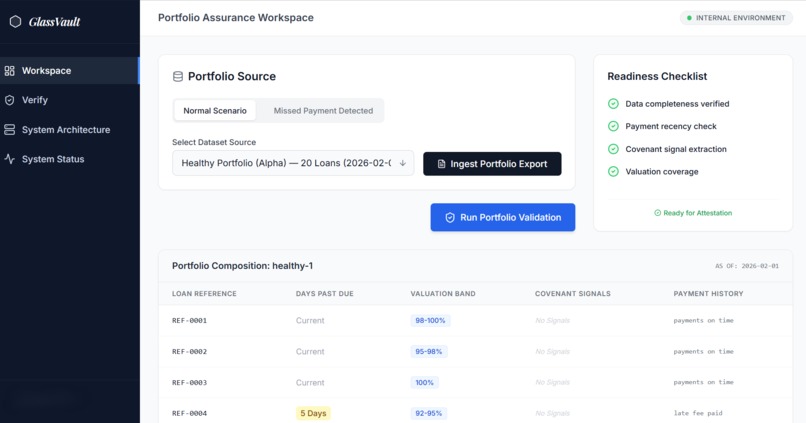
Select a standardized portfolio snapshot and prepare it for validation.
-
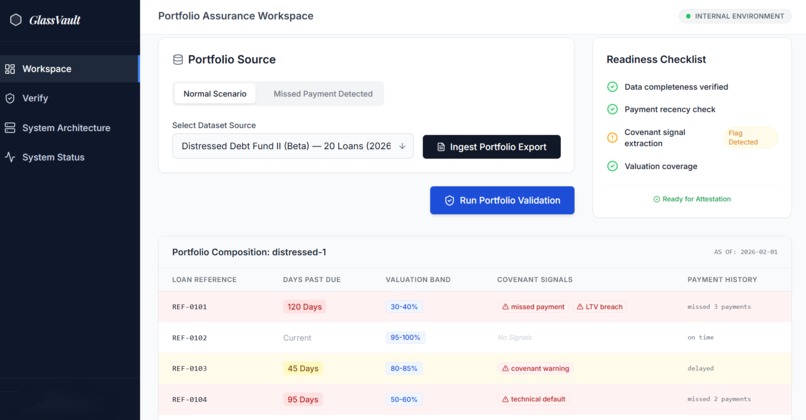
Early risk signals surfaced through anonymized loan-level indicators.
-
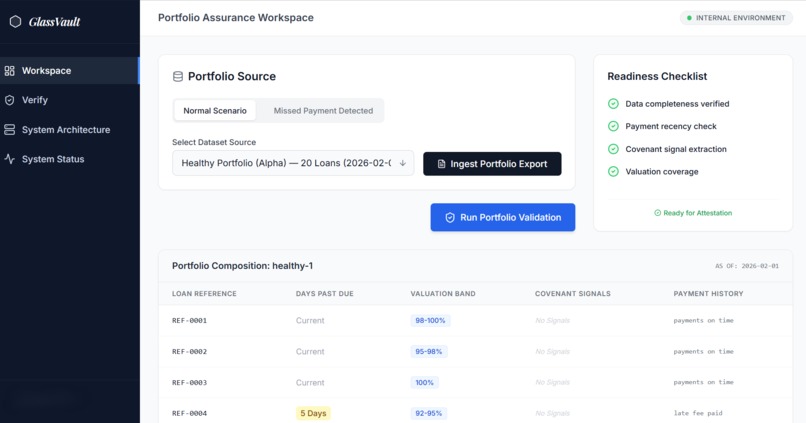
Automated readiness checks confirm data completeness and validation eligibility.
-
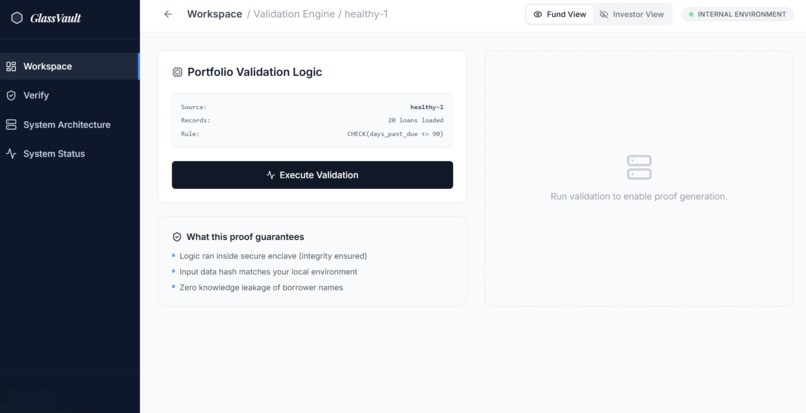
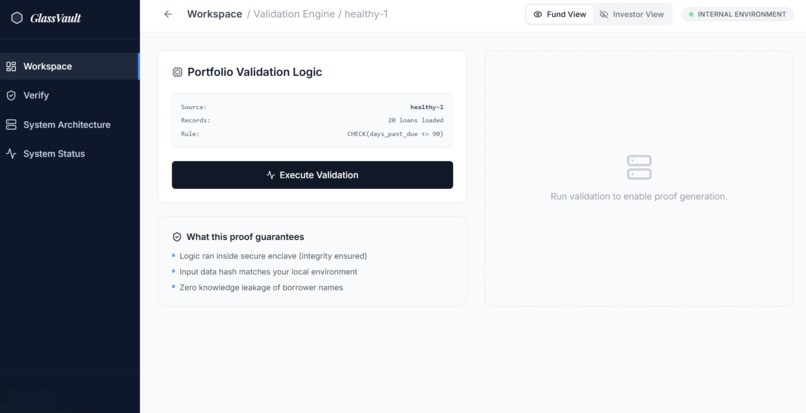
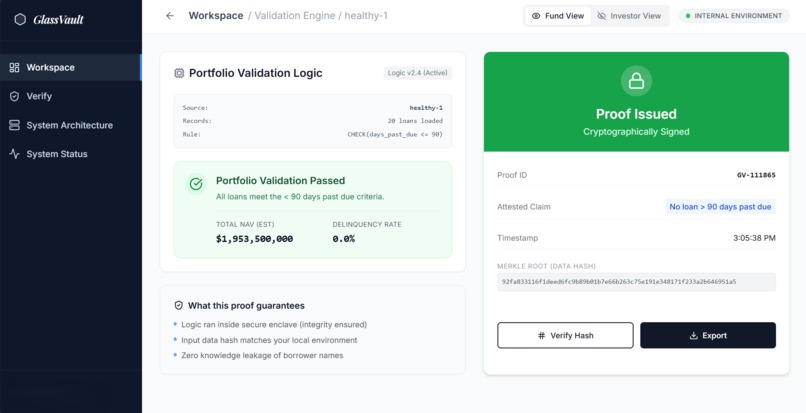
Deterministic validation logic applied inside a controlled environment.
-
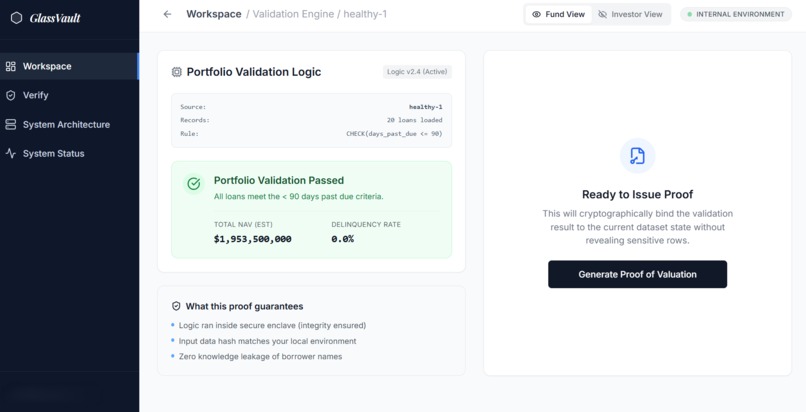
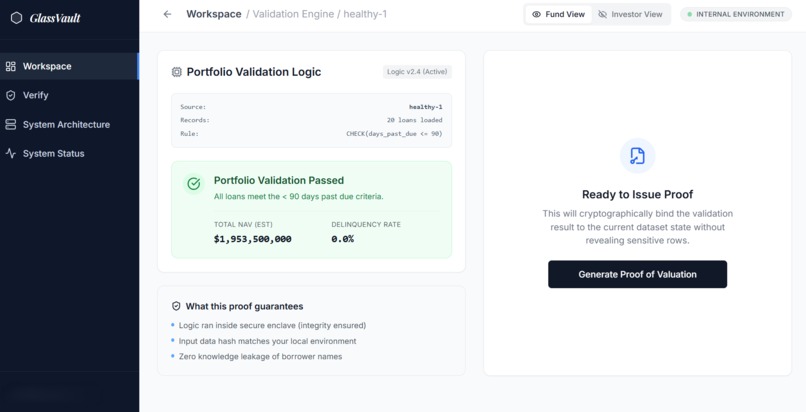
All validation criteria satisfied. Portfolio health confirmed.
-
A cryptographic proof binds the claim to this exact portfolio state.
-
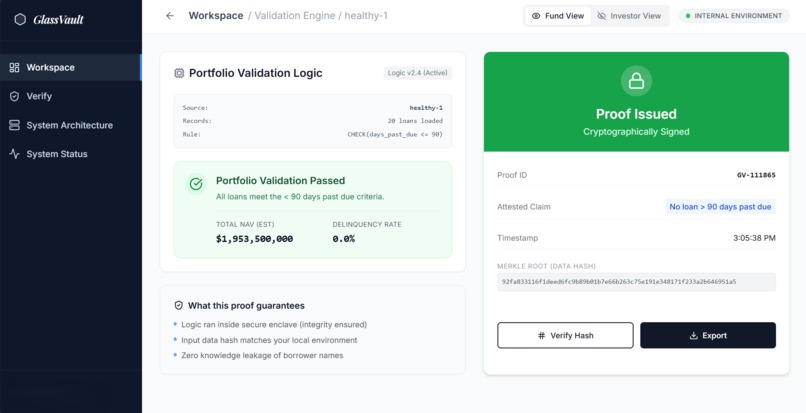
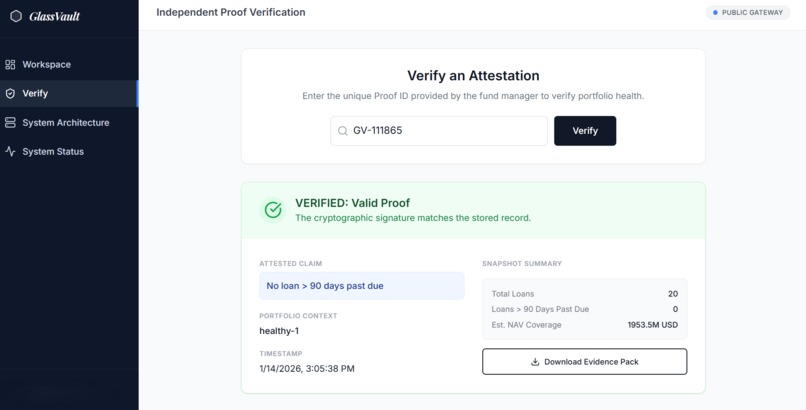
Third parties verify portfolio claims without accessing borrower data.
-
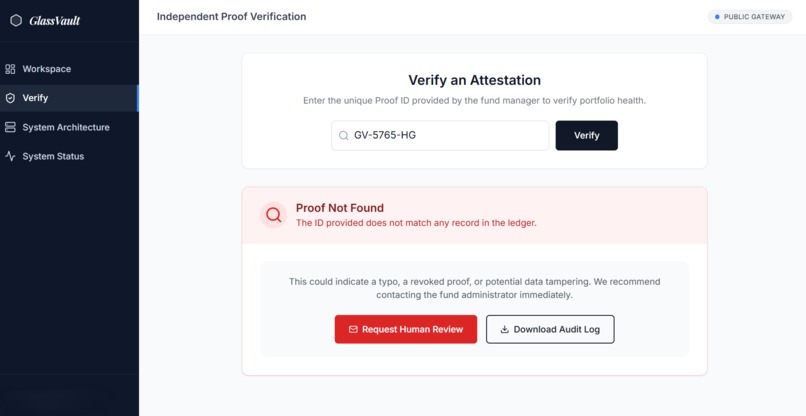
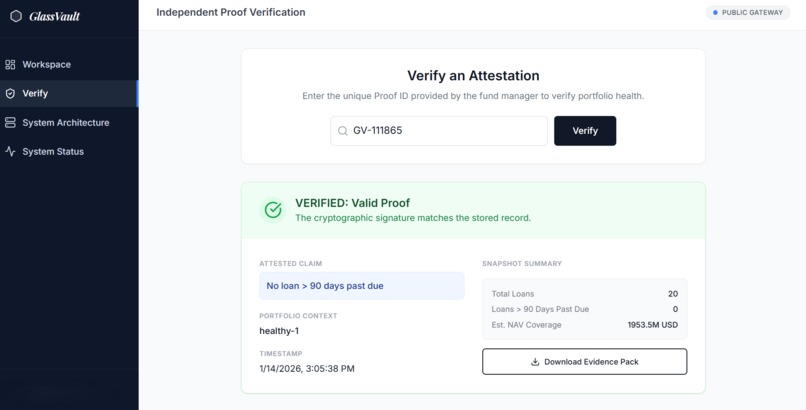
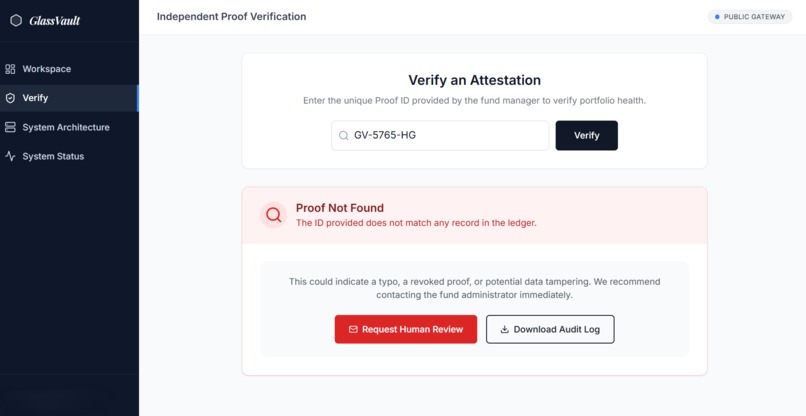
Invalid or altered proofs are immediately flagged for escalation.
-
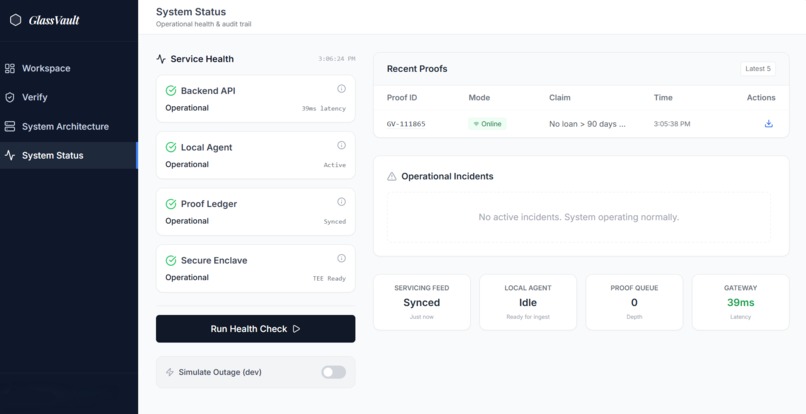
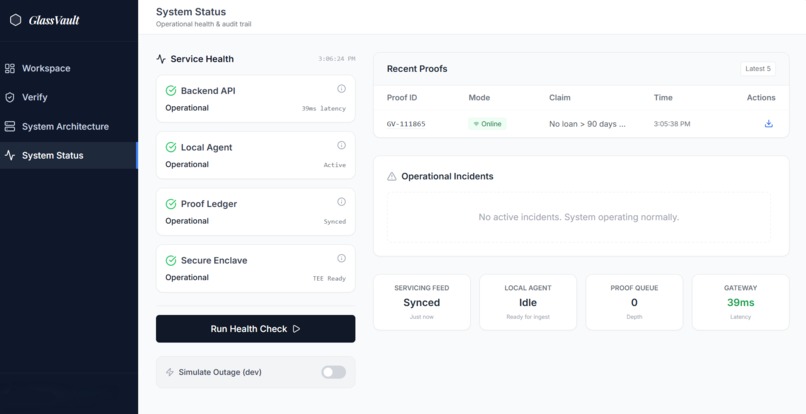
Operational transparency across validation, proof, and verification layers.
Inspiration
Private credit markets are built on trust, but today that trust is fragile.
Across the loan lifecycle, portfolio health is still communicated through periodic, self-reported PDF packs and manual reconciliations. Investors worry about hidden defaults and valuation opacity, while funds are constrained by confidentiality, regulation, and commercial sensitivity. This creates a structural tension: markets demand transparency, but institutions cannot disclose raw borrower data.
GlassVault was inspired by this gap - the lack of a credible way to prove portfolio health without revealing the underlying secrets. We wanted to explore whether trust could be established through verifiable claims rather than disclosure.
What it does
GlassVault is a digital portfolio assurance platform designed for private credit.
It ingests standardized portfolio signals, runs deterministic health validations, and generates a cryptographic proof of valuation that can be independently verified — all without exposing borrower-level data.
At a high level, GlassVault proves statements like:
- No loan exceeds a defined delinquency threshold (e.g. >90 days past due)
- Portfolio valuation is derived consistently from observed valuation bands
- The proof is time-bound to a specific portfolio snapshot
In simple terms, GlassVault proves a clear business statement: “No loan in this portfolio is more than 90 days past due. The system verifies this without revealing any individual loan records, borrower identities, or contract details.
This creates conditional transparency — investors and auditors can trust that the portfolio meets agreed health criteria, even though the sensitive underlying data remains private.
How we built it
GlassVault is implemented as a desktop-style internal web application , designed to mirror how institutional tooling actually feels and behaves.
Architecture
Standardized Portfolio Export ↓ Deterministic Validation Engine ↓ Cryptographic Attestation (hash-based) ↓ Independent Verification Interface
Technical approach
- Frontend system built with React + TypeScript
- All validation logic runs locally in the browser to simulate execution inside an institutional perimeter
- Synthetic, audit-style datasets model real portfolio structures without using live borrower data
- Cryptographic attestations are generated using deterministic hashing to bind:
- portfolio snapshot
- validation results
- timestamp
- Proofs are portable and verifiable via an independent verification view
- Offline-capable by design to reflect internal operational environments
The focus was not on flashy automation, but on clarity of flows, auditability, and credibility of claims.
Challenges we ran into
Balancing realism with safety We wanted the system to feel authentic without using real borrower or fund data. This required carefully designing synthetic datasets that still reflect how audit and loan operations actually work.
Explaining cryptographic assurance visually Many users are unfamiliar with proofs and attestations. A major challenge was making the system explain itself through UI — showing what is being proven, what is hidden, and why that matters.
Accomplishments that we're proud of
- Designed a clear end-to-end assurance workflow that non-technical stakeholders can understand
- Demonstrated how portfolio trust can be built without data disclosure
- Built a system that feels like real internal enterprise software, not a demo -Created an independently verifiable proof model aligned with audit and secondary trading use cases
- Delivered a fully deployed, offline-capable application under tight time constraints
What we learned
- Trust in financial markets is often about process, not just data
- Audit and verification workflows benefit more from deterministic guarantees than from opaque intelligence
- Strong UX is essential when introducing new trust primitives
- “Prove the claim, not the secret” is a powerful design principle beyond crypto — it applies directly to real-world assets and lending
What's next for GlassVault
GlassVault is positioned as audit-support and assurance infrastructure
Next steps include:
- Hardening the attestation layer for production environments (secure enclaves / HSMs)
- Integrating directly with servicing, agent, or post-trade system outputs
- Expanding the claim set beyond delinquency to include covenants and coverage metrics
- Running closed pilots with funds, auditors, or agents under NDA
- Aligning outputs with existing regulatory and audit standards
The long-term vision is simple: make opaque credit markets verifiable — without breaking confidentiality or trust.
Built With
- cryptoapi
- css
- html
- javascript
- json
- react-native
- react-state
- sha-256
- typescript
- vite
Log in or sign up for Devpost to join the conversation.