-
-
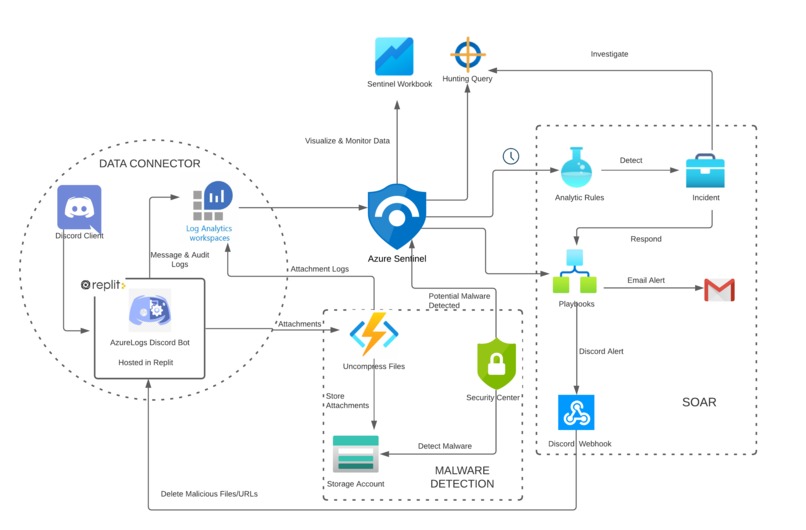
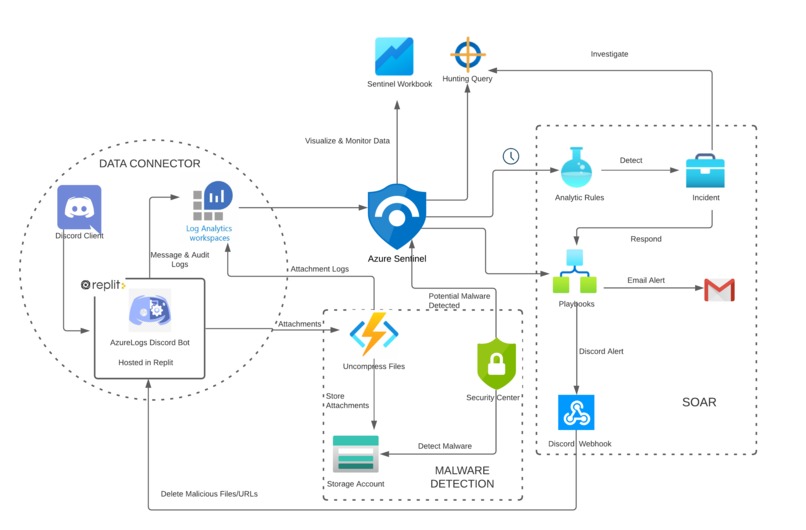
Technical Architecture Overview
-

Discord Audit Workbook - Storage Blob operations
-

Discord Resource Workbook - Function App
-

Malware Response Playbook
-
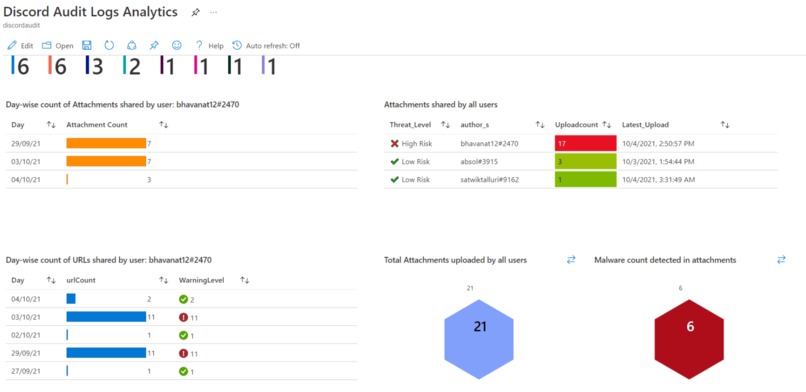
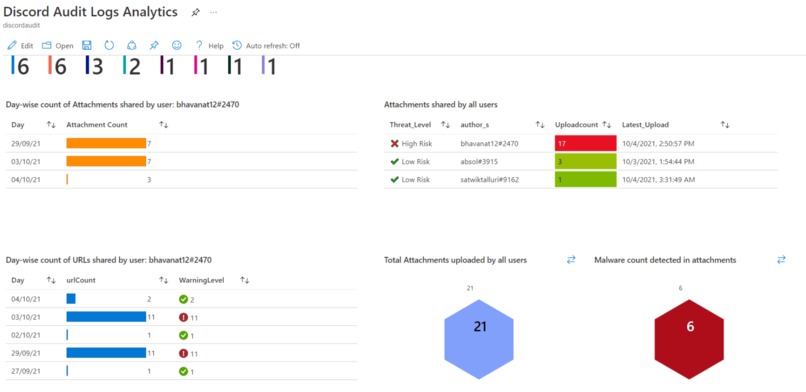
Discord Audit Workbook - Attachment Sharing pattern
-

Hunting Query - User's Full activity
-

Discord Audit Workbook - Domains Shared in messages
-
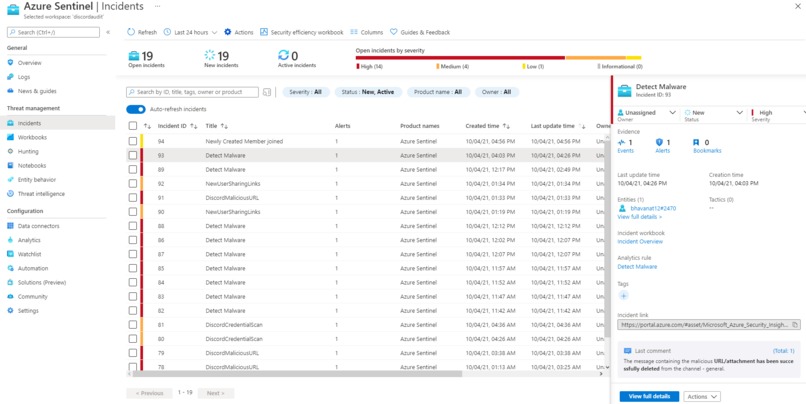
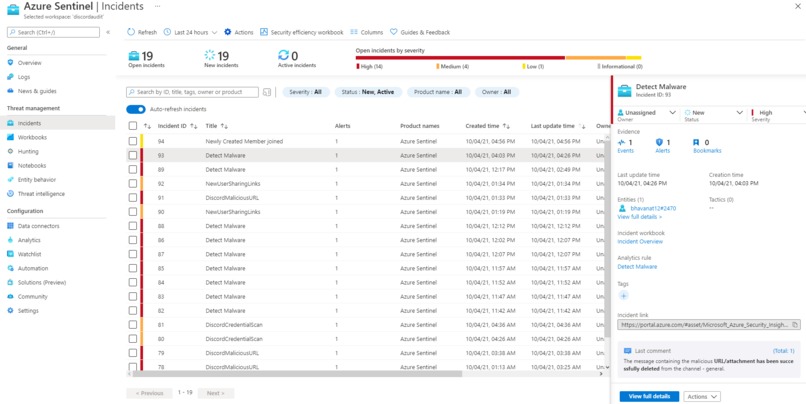
List of incidents
-
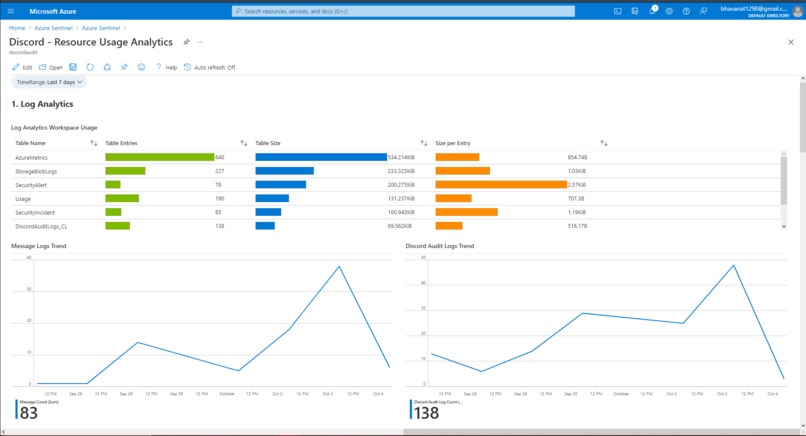
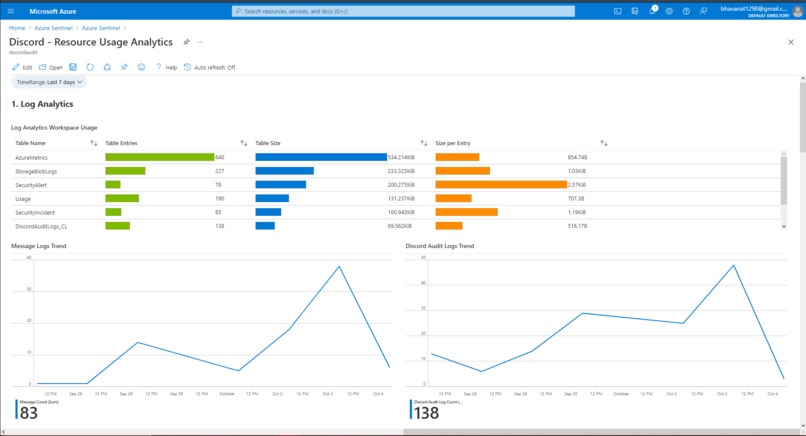
Discord Resource Usage Workbook
Team members
Abhishek Reddypalle (abhishek272000@gmail.com)
Bhavana Talluri (bhavana.t17@iiits.in)
Satwik Talluri (satwiktalluri1@gmail.com)
Inspiration
Due to the ongoing pandemic, several organizations have started to increasingly rely on collaborative platforms for their professional communication. Discord’s main advantage is that its base product is 100% free, easy to setup and thus it's attracting huge number of small and medium scale organizations to choose this platform as the primary source of communication.
Attackers are abusing these platforms for hosting malicious content, exfiltrating sensitive information, and otherwise facilitating malicious attacks. These applications may also provide an additional means to perform the social engineering required to convince potential victims to open malicious attachments. Targets who see a link in a chat room they're used to interacting in on a regular basis may be more likely to open any files or links.
What it does
To resolve this problem, we have built an end-to-end cybersecurity solution for Azure Sentinel that monitors Discord messages and Audit operations, facilitating the enterprises to respond to threats and mitigate them in a timely fashion. This solution enables enterprises that use Discord, onboard to Azure Sentinel and leverage components like workbooks, playbooks, analytic rules, hunting queries, etc. Some of the features of our solution include:
Malicious URLs or Files Detection and Mitigation:
When malicious URLs or Files are shared as messages across discord channels, these are detected (leveraging Azure Defender, Blob Storage, Function App) and deleted by our solution using Webhooks. A Discord Alert is then triggered using the playbook, which notifies the Discord Admin about the threat.Attachment Forward Detection:
Whenever an attachment is uploaded to discord, it generates a CDN URL in this specific format (https://cdn.discordapp.com/attachments/{channelId}/{messageId}/{filename}) which might not be perceived as malicious by most users. We call an attachment to be forwarded if it's CDN URL is shared instead of the file directly and victims are more likely to open it as the URL looks secure (https, discord prefix). However in our solution, attackers cannot bypass the threat detection by passing URL instead of attachments. This is because we process all CDN URLs as attachments and perform the same security analysis that's done for the attachments. Therefore, our solution goes a step further by not only identifying threats in attachments, but also tracks down the malicious content disguised as a CDN URL.Blacklist Extensions:
Attackers mostly use uncommon compression algorithms to obfuscate the malicious content and share them over collaborative platforms. We are preventing this by allowing Discord Admin to configure the blacklisted extensions, and only allow the standard zip formatted attachments.Beware of newly created Bot and User accounts:
Most of the times, attackers create instant fake accounts impersonating an individual and try to gain access to a Discord server. Our solution identifies members or bots whose discord accounts are created very recently and alerts the Admin when they join the server. Details such as the account creation date, messages/URLs shared and other activity are made available to the Admin via Hunting queries. This is done to keep track of user's/bot's activity before any malicious content is shared.Alert when Credentials are shared in messages:
When sensitive information like credentials (JWT, shared keys etc.) are shared in Discord messages, our solution detects them, creates a medium level incident and notifies the Discord Admin.Newly joined member sharing links:
Our solution actively monitors the activity of newly joined members in the Discord server and creates an alert if they start sharing links within 30 minutes of joining. Discord admin is further given the choice of banning the user from the channel if these links turn out to be malicious. This is done to track the attackers who join the channel and share malicious content.Monitor Discord Audit operations:
Our solution notifies the Discord Admin of every critical Audit operation performed on the Discord Server. These include Granting/Revoking Admin privileges, Deleting Channels etc. Hunting queries are also created to actively monitor if multiple channels are deleted in a short time interval, monitor a user's complete activity etc.Discord Monitoring Dashboard:
Discord Admin can periodically monitor the Sentinel workbooks for the Resource usage of the Sentinel Solution and also gain insights about the functioning of the Discord Server.
How we built it
Discord Bot
We developed a bot that serves as medium between Discord and LogAnalytics workspace. It is hosted on cloud through replit, where action items are coded for multiple events (on_message, on_member_join etc.) occurring on Discord. This data is then ingested to the LogAnalytics workspace, where Analytic rules, hunting queries, playbooks and workbooks help in threat detection and response automation. The Bot component serves as our ETL (Extract, Transform, Load) layer where useful components in the Discord log data are extracted and instantly ingested into Azure. The bot is programmed using python, leveraging the discord.py API reference.
Azure Blob Storage
Attachments shared in Discord are ingested into the Azure Blob storage after getting decompressed in the Azure Function App. The blobs produce operation streaming logs which contain hashes related to the blob and these hashes are compared using Microsoft's Threat Intelligence to do hash reputation analysis looking for viruses, trojans, spyware and ransomware. Whenever a match is found an alert is raised in Azure Security Center.
Azure Sentinel
Analytic Rules:
Once the logs are ingested into LogAnalytics workspace, we created custom analytic rules for discovering threats and anomalous behaviors. Incidents are configured to be created whenever the conditions are met (Ex: Admin privileges assigned/revoked, Attachment forwards detected, malicious links found, etc).Playbooks:
Whenever a malicious link or file is found in Discord messages, it's extremely important to delete the message immediately instead of waiting for the Admin to take action. A playbook is configured to send delete command to discord API via a webhook, which instantly deletes the message. A Discord alert message and email are also sent using a playbook to notify the Admin about the threat and the delete action performed.Hunting Queries:
Hunting queries are configured to enable security analysts to proactively hunt for anomalous behaviors in the Discord environment. At any moment, they can query to observe the patterns of critical operations such as, getting details of malicious files detected over time, querying all activity related to a suspicious member, deleting multiple channels in a short interval etc.Workbooks:
In the world of security operations, dashboards and visual representation of data, trends, and anomalies are essential for day to day work. Our solution provides advanced visualizations that not only help organizations identify anomalies and gain deeper insights on application, but also enables them to have a close watch on the resource usage of the Sentinel Solution.
Challenges we ran into
- Solution architecture:
We had a lot of back and forth on how the logs should be ingested into Sentinel and at what frequency. We initially used an Azure Function App which would be triggered periodically to check for recent logs and ingest them into Event Hub. However, we wanted to have a solution that instantly ingests logs into the Sentinel and ensures a faster threat hunting, which is critical when malicious content is shared. Hence we moved our data connector onto a standalone replit server, where the application now listens to the events triggered on Discord (Ex: on_message, on_member_join etc). - Cost:
As we are new to sentinel, we have initially used Event Hub to store the ingested Discord Audit/Message data as this data is available to us in the form of events. However this didn't seem cost efficient for our use case and the charges were huge for few days of storage. Upon further research we learnt about LogAnalytics and used it to store our ingested data. - Discord Bot:
Initially our attachment processing logic was also handled by the discord bot. However, after observing the increased computation load and slow performance, we quickly decoupled the processing logic and implemented it using Azure Function.
Accomplishments that we're proud of
- We are proud to have developed an end-to-end cybersecurity solution that would enable collaboration platforms like Discord to be securely used by organizations. As the world is moving into a virtual work environment, now is the time we rely on these platforms more than ever. We wanted to implement a solution that enables Discord to be easily onboarded to Sentinel without much overhaul and we are proud to have accomplished this.
- We are also proud to have implemented the solution using many different technologies. We have always made the choice to not use the easiest software and tools, but the right ones for the requirements. For example, we were easily able to achieve the log ingestion by using Azure Function App, however we wanted a solution that can transfer data instantaneously instead of periodic ingestion. This is especially crucial when malicious content is shared. We explored several standalone servers and finally settled on Replit, which is a free, secure, Integrated development and hosting platform. Also since the discord bot we developed is event-driven, a standalone server would help in instantaneously transferring the data to LogAnalytics workspace.
What we learned
This project helped sharpen our skills as developers and exposed us to new technologies such as Azure Sentinel, Defender, Logic Apps, Function App, Blob storage, webhooks etc. We are delighted to have mastered KQL programming language in such a short duration and were able to write complex queries to create advanced visualizations in Workbooks. More importantly, we learned about the various kinds of vulnerability challenges in the remote working setup and the importance of a well managed security model. The CDN URLs in Discord are one of the major sources of cyber attacks and we have not only understood the complexity of this problem but also developed a solution that is robust to CDN based threats. This hackathon has inspired us to more actively explore and contribute to the prevention of cyber attacks globally.
What's next for DiscordSecure
We are proud to have gotten this far in our spare time of a month. However, there are a few improvements that we would still like to make to this solution
- Currently we are using Azure Defender to identify threats in the attachments uploaded. The disadvantage here is that Defender doesn't analyze the files but only compares hashes of the blobs. Also, the malware detection here takes around 40 minutes when using Azure Defender. We want to explore other options like VirusTotal, which analyze entire attachment and provides detection results in a shorter duration.
- Currently we are relying on Third party threat intelligence feeds like Threatview.io to get the list of banned domains and IPs. We would like to continuously expand our dataset of malicious domains so as to make the classification highly accurate.






Log in or sign up for Devpost to join the conversation.