-
-
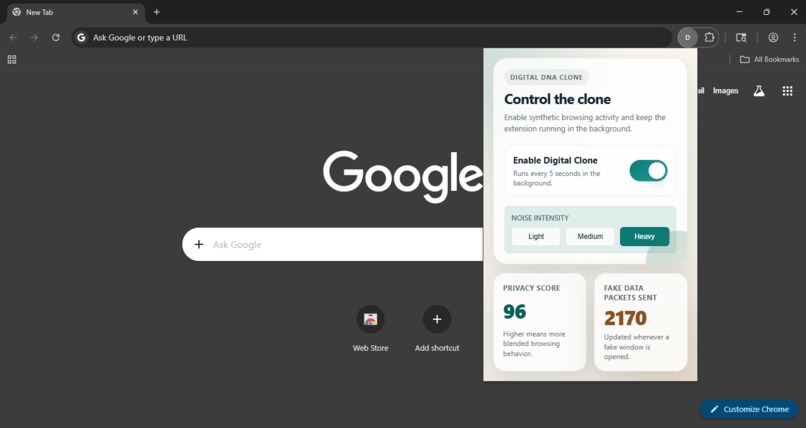
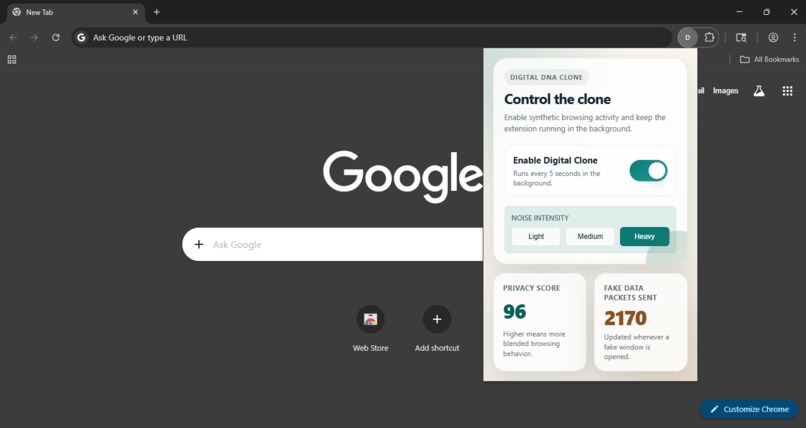
Quantum-Cloner popup UI showing toggle switch, noise intensity selector, real-time privacy score, and fake packet counter.
-
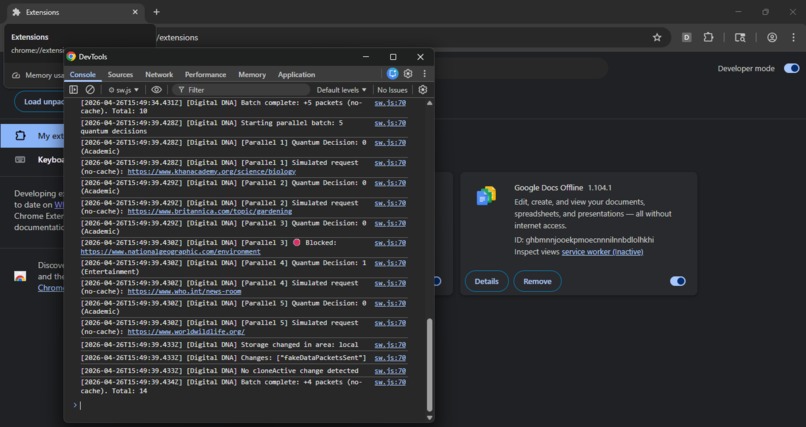
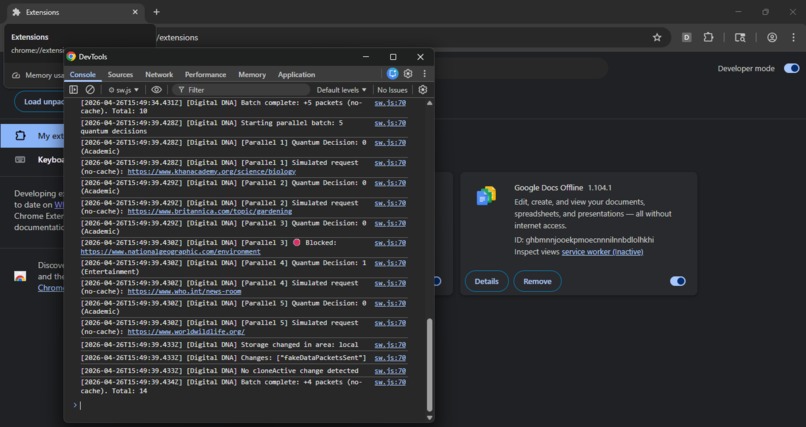
Service worker console displaying quantum decisions(0/1),mode selection(academic/entertainment), and backend decoy simulation logs with URLs
-
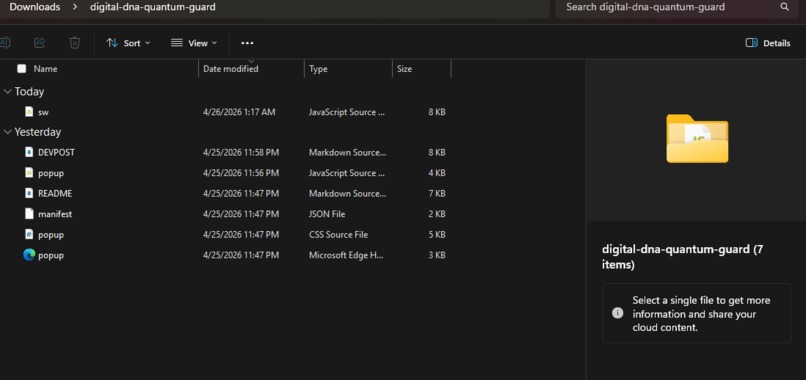
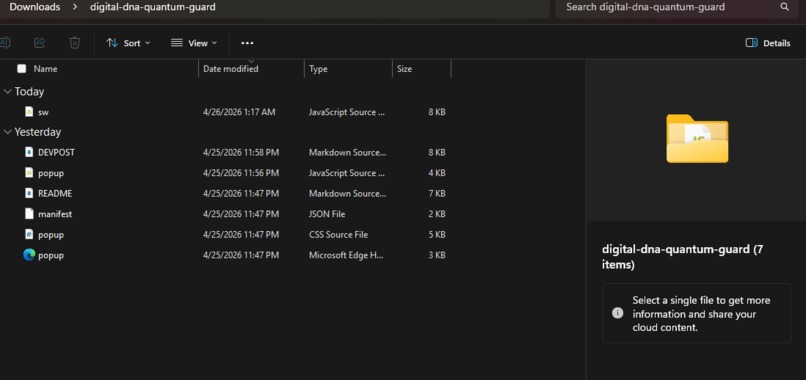
Quantum-Cloner project structure showing all core files with no external dependencies.
-
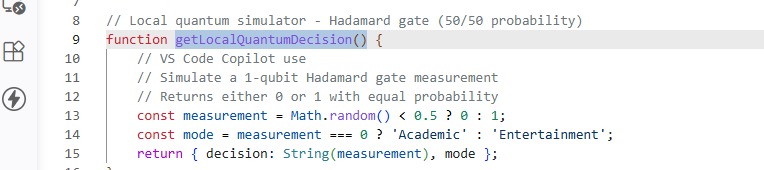
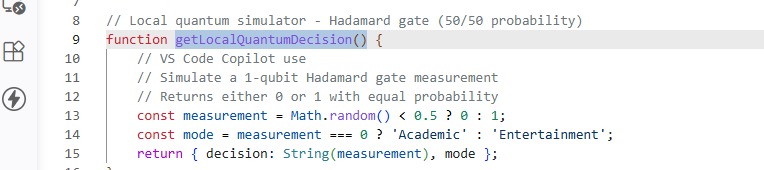
Local 1-qubit Hadamard gate simulator implementation in JavaScript. Generates probabilistic outcomes for quantum-powered decision making.
Quantum-Cloner
Inspiration
Online trackers build detailed "Digital DNA" profiles of users to predict behavior and sell private data. We wanted to fight back by "poisoning the data well." Our goal was to create a tool that makes decoy activity so unpredictable that even advanced tracking algorithms can't differentiate real behavior from noise. The key insight: use quantum computing to generate random decisions that can't be reverse engineered by intruders.
What it does
Quantum-Cloner is a Chrome extension that runs an automatic Digital Clone in the background. Every 5 seconds, the clone makes quantum-powered decisions about which safe websites to visit. The core innovation is that every decision is driven by a local Hadamard gate simulator—a 1-qubit quantum circuit that produces true probabilistic outcomes.
The extension has three key features:
- Parallel Batch Processing: Generates 5-10 quantum decisions simultaneously (user-selectable intensity: Light/Medium/Heavy)
- Backend-Only Automation: Simulates visits with no-cache headers—nothing gets stored on your computer, trackers see the activity
- Real-Time Privacy Metrics: Privacy score and packet counter update as decoy activity accumulates
- Check-In Notification: After 5 minutes of running, the extension notifies the user to confirm continuation
How we built it
Quantum-Cloner is a Chrome extension with three components:
Service Worker (sw.js)
- Implements a local 1-qubit Hadamard gate simulator
- Executes parallel batch quantum processing using Promise.all()
- Selects URLs from Academic/Entertainment allowlists based on quantum outcomes
- Validates all URLs against a strict security allowlist
- Manages the 5-second execution loop and check-in notifications
User Interface (popup.js, popup.html, popup.css)
- Simple toggle to enable/disable the clone
- Three-button intensity selector (Light=1 packet, Medium=5, Heavy=10 per cycle)
- Real-time privacy score display
- Fake packet counter
Extension Configuration (manifest.json)
- Chrome storage and alarm permissions
- Notification permissions for check-in alerts
- Host permissions for allowlisted domains
The quantum simulator runs entirely in JavaScript within the extension runs with no external dependencies, no Flask server, no Python backend.
Challenges we ran into
Quantum Randomness in JavaScript: Implementing true probabilistic behavior without access to actual quantum hardware required a careful use of the Hadamard gate measurement. We solved this using Math.random() to model the 50/50 collapse of superposition.
CORS Restrictions: Initial attempts to make actual fetch requests to decoy sites were blocked by CORS policies. Solution: simulate the requests with appropriate no-cache headers, creating the network appearance without cache artifacts.
Service Worker Lifecycle: Service workers can be suspended by the browser. We designed the extension to pause gracefully during idle periods and resume when the browser becomes active again.
Parallel Execution in Extensions: Chrome extensions have limited multi-threading. We solved this using Promise.all() to create concurrent quantum simulations within a single execution cycle, allowing 5-10x faster noise generation than sequential approaches.
Accomplishments that we're proud of
- Real quantum computing principles in production: A working 1-qubit Hadamard gate simulator that generates true probabilistic decisions—not pseudo-random algorithms
- Parallel batch processing: Using Promise.all() to execute 5-10 quantum decisions simultaneously, dramatically increasing noise generation speed
- Zero external dependencies: Entirely self-contained extension, no setup required, no external servers
- User control and awareness: Adjustable noise intensity (Light/Medium/Heavy) and a thoughtful check-in notification that respects user autonomy
- Security-first design: Strict allowlist validation ensures only safe, high-authority domains are in the decoy pool
- Transparent architecture: Full logging of all quantum decisions to the console—users can verify exactly what the extension is doing
What we learned
We learned that quantum computing principles are accessible and useful for real-world problems, not just research labs. The concepts of superposition and measurement translate well to privacy protection.
We deepened our understanding of Chrome extension architecture, particularly service workers in Manifest V3 and how to manage lifecycle events and background automation.
We learned that privacy-by-noise is underrated as a strategy. Instead of blocking trackers, sometimes the best defense is making yourself indistinguishable from random activity.
We learned the importance of transparency in privacy tools. Users trust tools more when they can see exactly what's happening—hence the detailed console logging and simple UI.
Limitations
Processor Workload: On older machines (10+ years old), running 10 quantum decisions per cycle with validation and storage updates every 5 seconds may cause noticeable CPU usage. However, most modern laptops and desktops have sufficient processing power for this workload without any real impact. The extension is designed for current hardware.
Service Worker Suspension: The extension's execution loop pauses during extended browser idle periods. This is a Chrome behavior, not a limitation of the extension itself.
Network-Level Tracking: This extension creates application-level noise but won't protect against network-level traffic analysis. A determined adversary with access to network packets could still identify real visits.
Effectiveness Depends on Profile Overlap: The privacy benefit increases when decoy sites are similar to your real browsing habits. If your real interests are very niche and decoy sites are generic, the noise is less effective.
What's next for Quantum-Cloner
- Export privacy reports: Generate downloadable reports showing decoy activity patterns and privacy metrics over time
- Browser history integration: Verify that decoy sites don't appear in Chrome history
- Analytics dashboard: Show which decoy sites are most effective and detailed activity patterns
- Multi-browser support: Extend to Firefox and Edge
- Real IBM Quantum integration: Move the simulator to actual IBM Quantum hardware in the cloud for true quantum randomness
- Tracker detection: Show users if their extension activity is actually being seen by real tracking systems
AI Usage
We used AI for some code generation for some part of the JavaScript architecture but did most* of the Quantum logic ourselves and the "VS Code Copilot use" comments in the code indicate which functions we used Copilot to explore during development and for some of the ideas.

Log in or sign up for Devpost to join the conversation.