-
-

Cypher AI
-

Problem Overview: We need to provide a better way to provide tech services without compromising privacy.
-
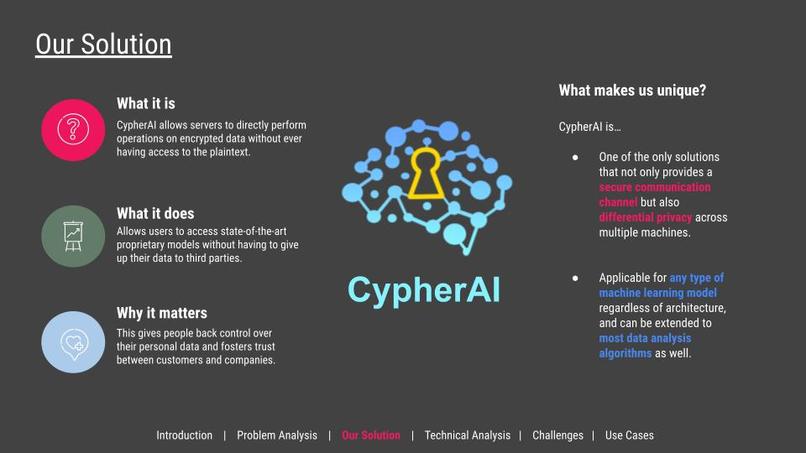
Our solution allows servers to perform operations on encrypted data without ever having access to the unencrypted user data.
-
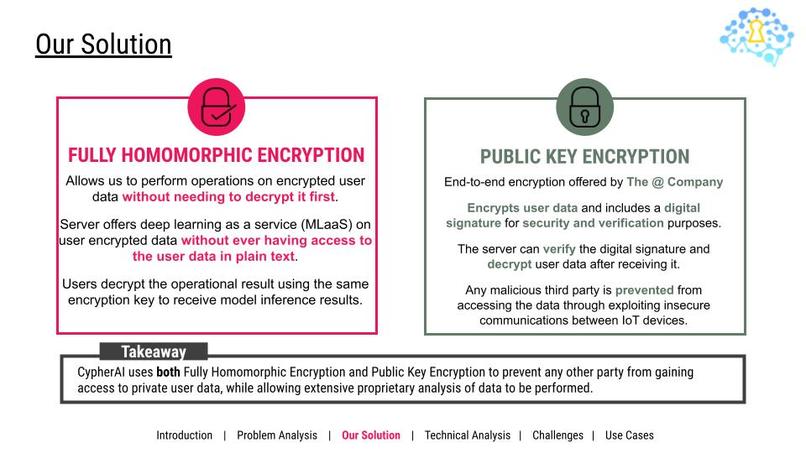
Two of our main features are fully homomorphic encryption as well as public key encryption.
-
Homomorphic functions are a structure-preserving map between two algebraic structures of the same type.
-
FHE is a scheme that allows users to send their data to servers without needing to trust third parties.
-
We used low-rank polynomial approximations to non-linear operators to implement convolutional neural networks.
-
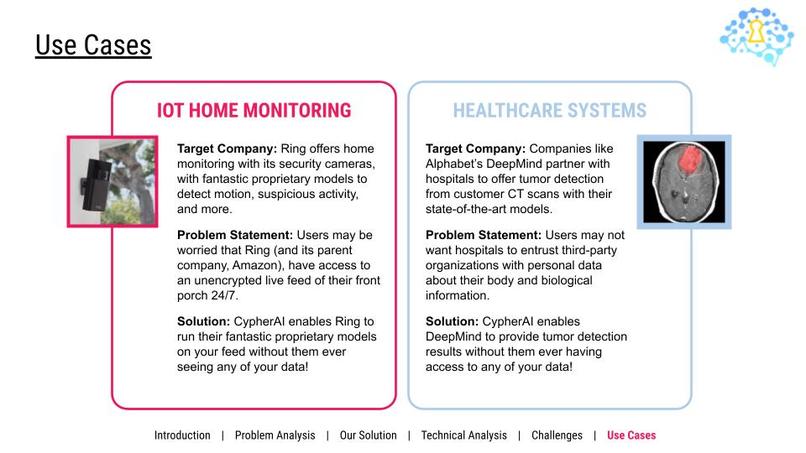
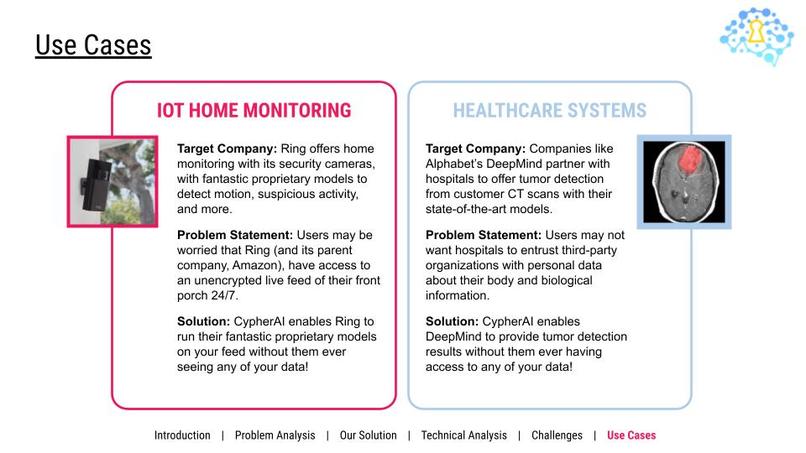
Two use cases are home security IoT devices, and healthcare systems.
Inspiration
81% of Americans today feel a lack of control over their own data. Customers today can’t trust that companies won’t store or use their data maliciously, nor can they trust data communication channels. However, many companies need access to user data to offer extensive proprietary analyses. This results in seemingly clashing objectives: how can we get access to state-of-the-art proprietary models without having to fork over our data to companies?
What if we can have our cake and eat it too?
What it does
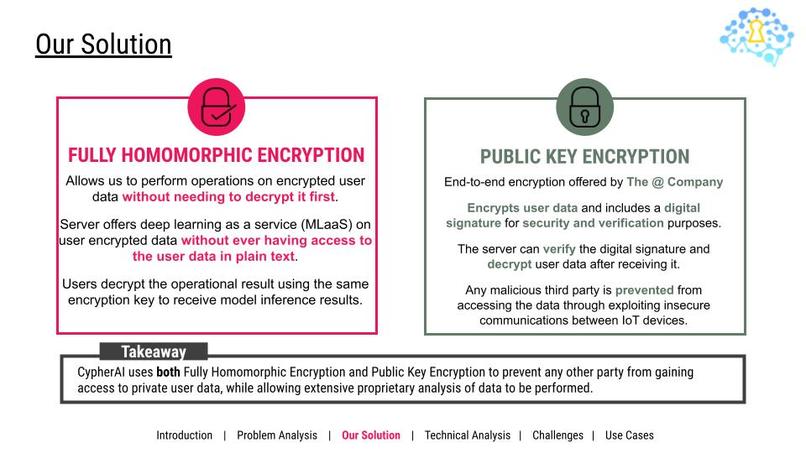
We use end-to-end encryption offered by The @ Company to encrypt user data and include a digital signature before we send it over an insecure communication channel. Using public-key cryptography, the server can verify the digital signature and decrypt user data after receiving it. This prevents any malicious third party from accessing the data through exploiting communications between IoT devices.
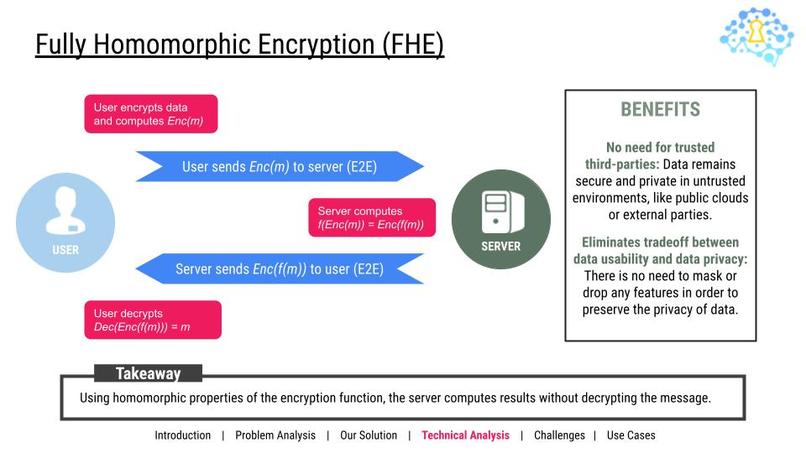
In order to prevent companies from having access to user data, we use a method known as Fully Homomorphic Encryption (FHE) to perform operations on encrypted user data without needing to decrypt it first. Therefore, we encrypt data on the user-side, send over the encrypted data to the server, the server performs operations on the encrypted data without decrypting it, then sends the result in ciphertext back to the user. Thus, we achieve access to state-of-the-art models saved on cloud servers without having to give up user data in plaintext to potentially untrustworthy companies.
How we built it
We used Flutter as our frontend, and trained two different machine learning algorithms in the backend. From our frontend, we encrypt our user data with FHE, and send it over an encrypted channel using services provided by The @ Company. Our backend runs a simple convolutional neural network (CNN) over the encrypted data without decrypting it, and sends the encrypted result back. Finally, the application decrypts the result, and displays it to the user.
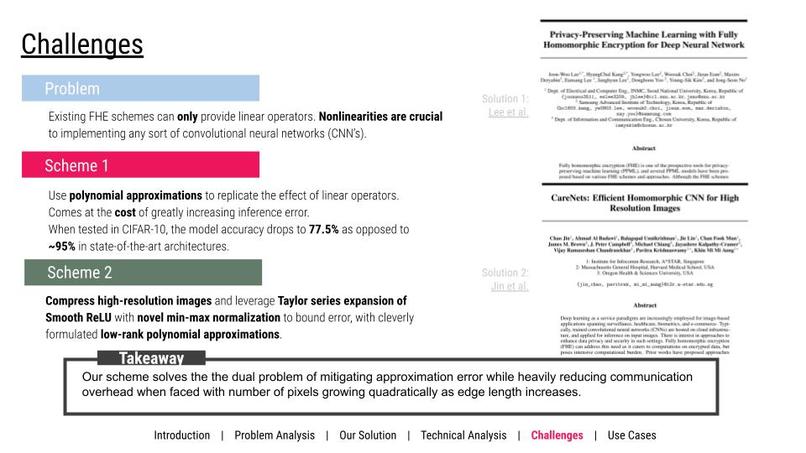
Challenges we ran into
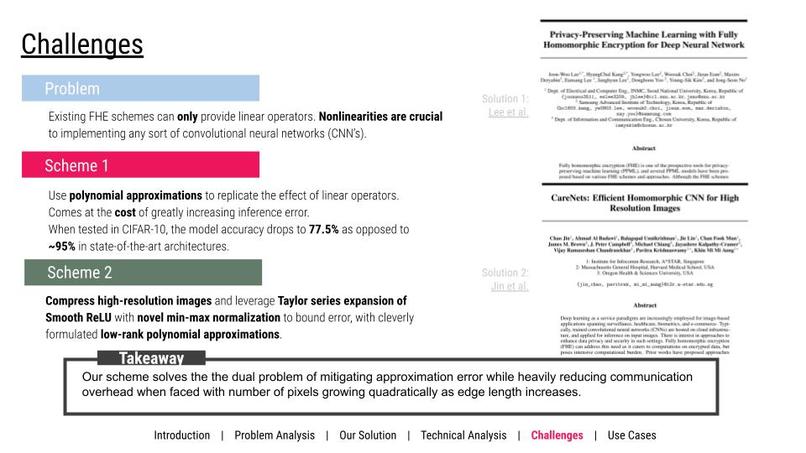
Currently, existing FHE schemes can only provide linear operators. However, nonlinearities are crucial to implementing any sort of convolutional neural networks (CNN’s). After doing some research, we initially decided to use polynomial approximations of nonlinear functions, but at the cost of greatly increasing inference error (on CIFAR-10, the approximation models produced an accuracy of 77.5% vs. ~95% on state-of-the-art models).
Again, can we have our cake and eat it too? Yes we can! We employ a scheme inspired by the latest FHE research that compresses high-resolution images and leverages Taylor series expansion of smooth ReLU with novel min-max normalization to bound error to approximately 3% off state-of-the-art, with cleverly formulated low-rank approximations.
This scheme solves the dual problem of heavily reducing communication overhead in other FHE schemes when faced with number of pixels growing quadratically as edge length increases.
Accomplishments that we're proud of
Not only did we get a demo up and running in a day, we also learned encryption algorithms from scratch and was able to implement it in our project idea. In addition to the technical application details that we had to implement, we also had to read different research papers, test out different models and algorithms, and integrate them into our project.
What we learned
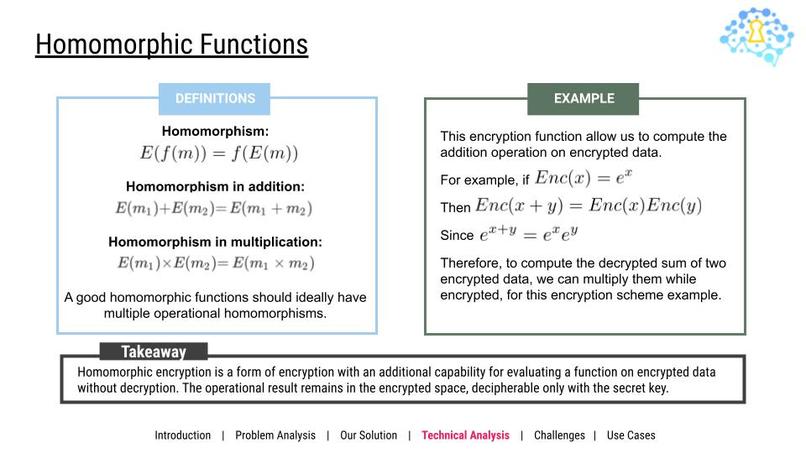
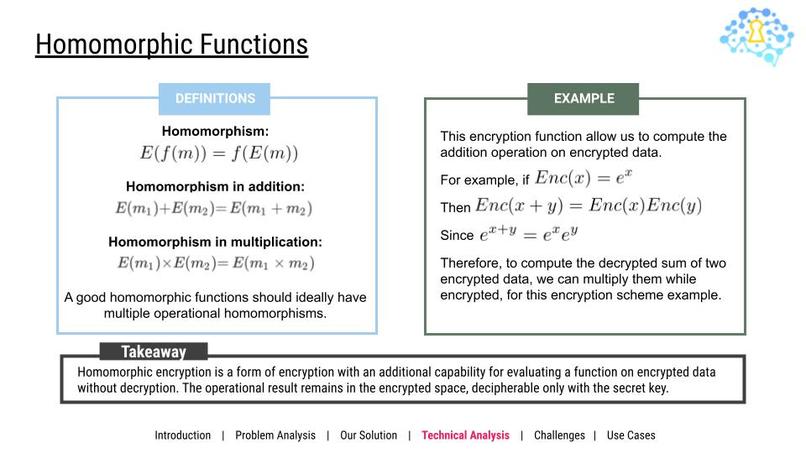
Homomorphic Functions
Homomorphic functions are a structure-preserving map between two algebraic structures of the same type. This means that given a function on the plaintext space, we can find a function on the encrypted ciphertext space that would result in the same respective outputs. For example, if we are given two messages m1 and m2, then homomorphism in addition states that encrypting m1 and m2 and then adding them together is the same as encrypting the sum of m1 and m2.
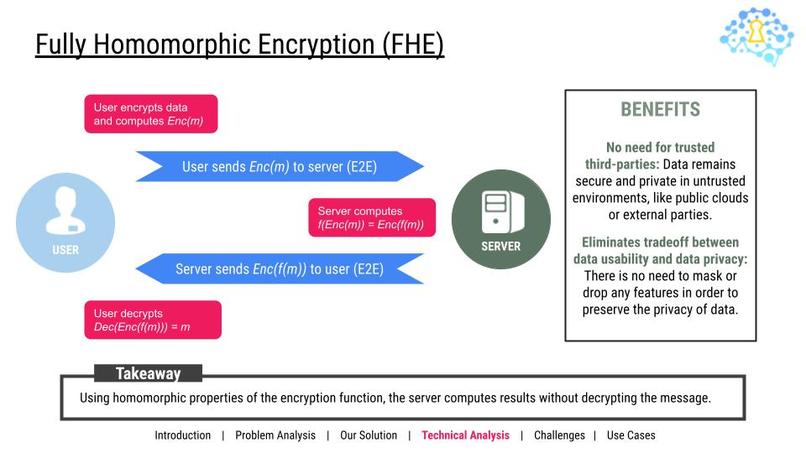
Fully Homomorphic Encryption
Fully homomorphic encryption uses homomorphic functions to ensure that data is stored in a trustworthy space. The user first encrypts their data, sends the encrypted data to a server, then the server performs computations on the encrypted data using homomorphic functions, and sends the result back to the user. Once decrypted by the user, the user will have their desired result. The benefits of FHE is that there is no need for trusted third parties to get proprietary data analysis. The user doesn’t have to trust the server with their data to get their results. In addition, it eliminates the tradeoff between data usability and privacy, as there is no need to mask or drop any features to preserve data privacy.
What's next for CypherAI
In our project, we demonstrated two use cases for our product in different company settles: home monitoring for security cameras, and healthcare systems. In the future, we are looking forward to expanding this beyond to other companies!





Log in or sign up for Devpost to join the conversation.