-
-
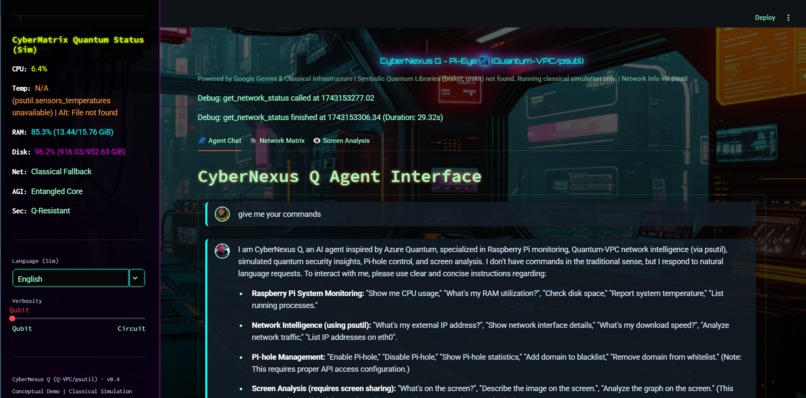
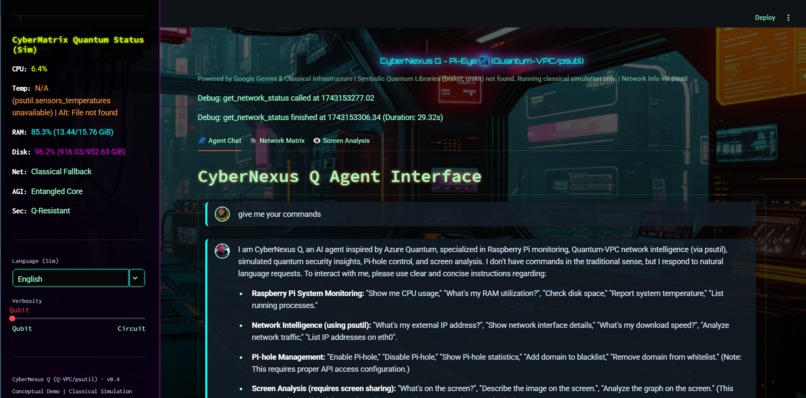
CyberNexus Q (Q-VPC/psutil) - v0.4 Conceptual Demo | Quantum Simulation (Agent Chat)
-
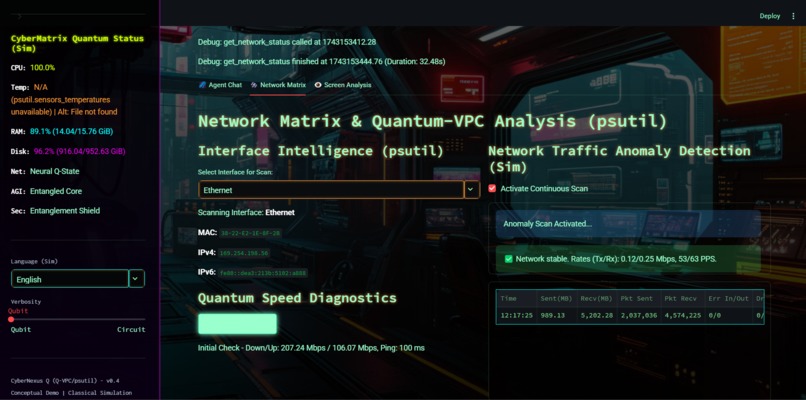
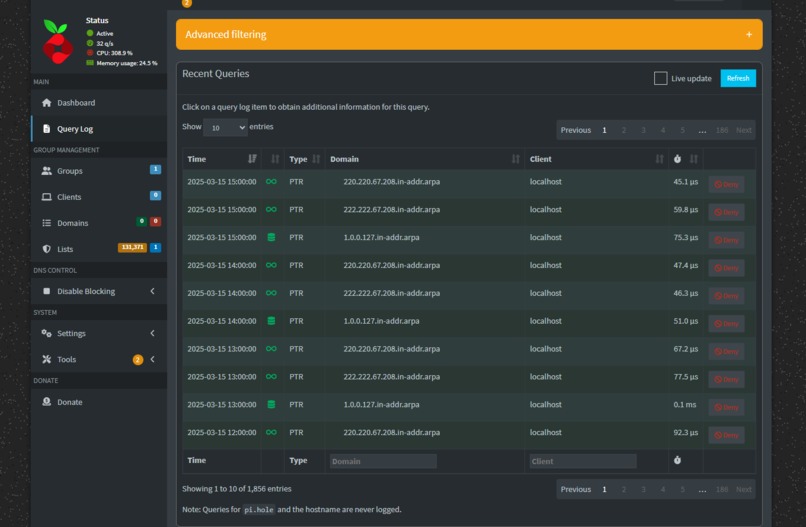
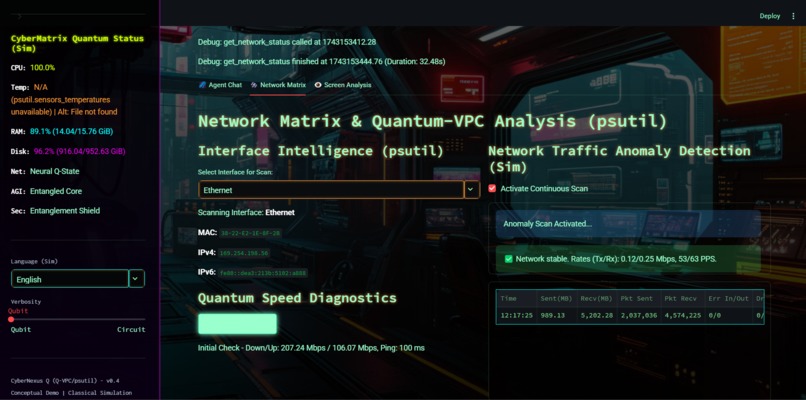
CyberNexus Q (Q-VPC/psutil) - v0.4 Conceptual Demo | Quantum Simulation (Network Matrix)
-
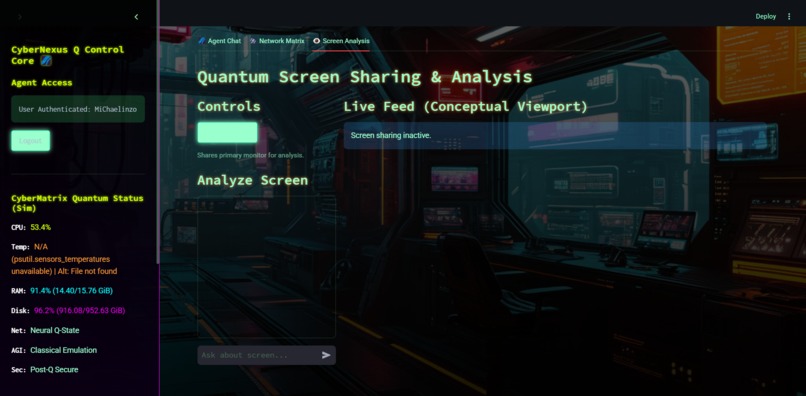
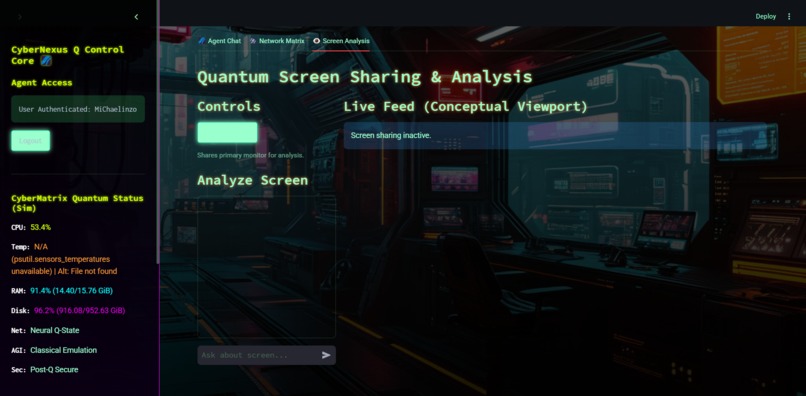
CyberNexus Q (Q-VPC/psutil) - v0.4 Conceptual Demo | Quantum Simulation (Screen Analysis)
-

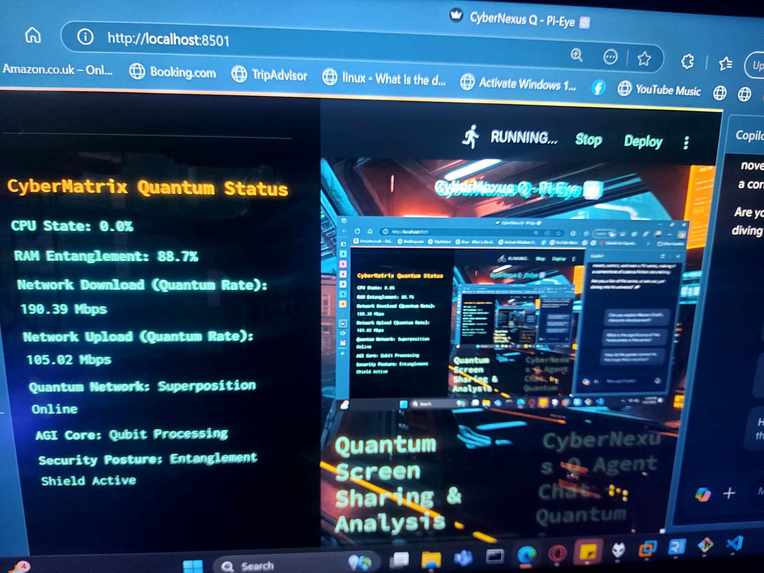
CyberNexus Pi-Eye Q AI-powered agent for network security LOGO
-
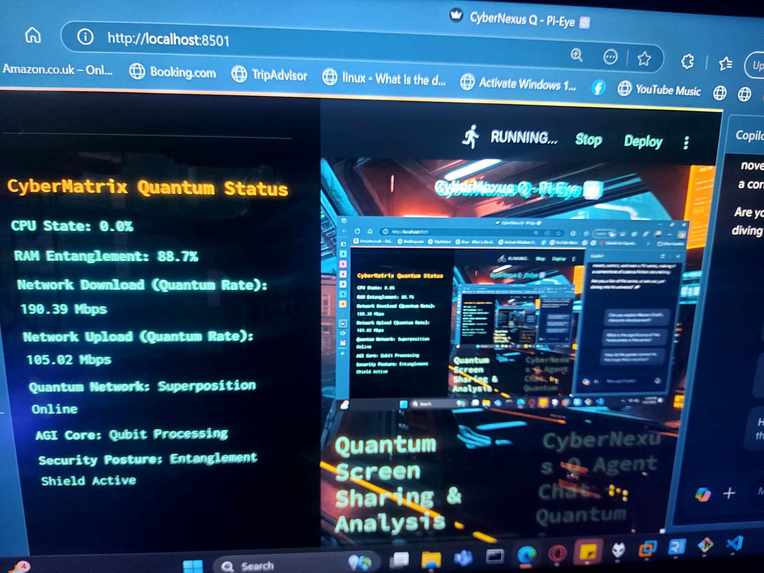
CyberNexus Pi-Eye Q AI-powered agent for network security Quantum running on loop
-

CyberNexus Pi-Eye Q AI-powered agent for network security Quantum Interface quantum vision screen-sharing
-
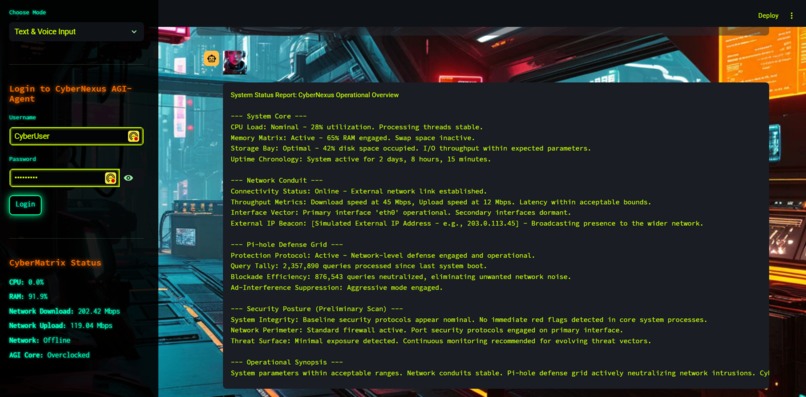
CyberNexus Pi-Eye Q AI-powered agent for network security and analysis
-

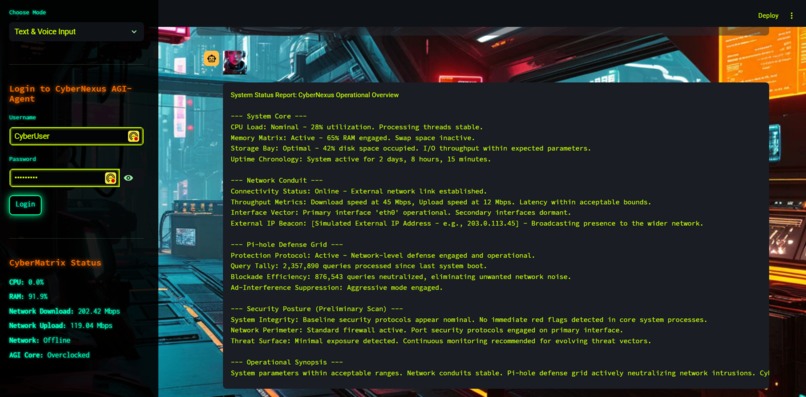
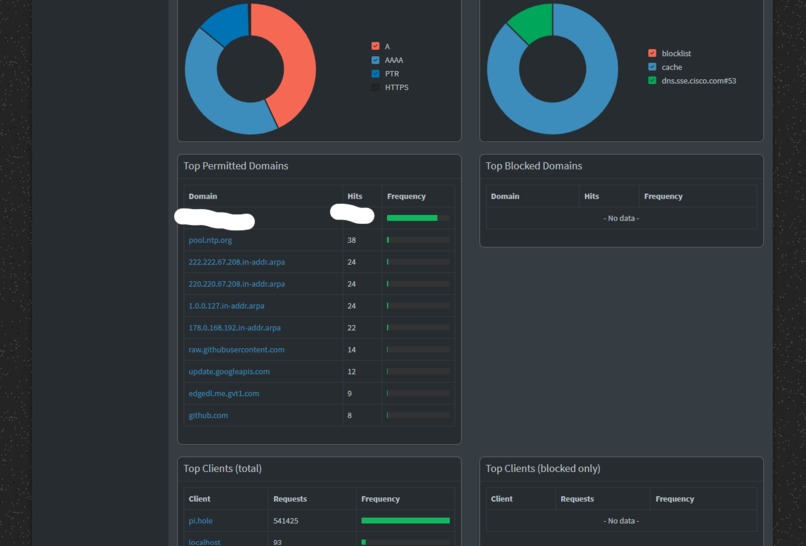
CyberNexus Pi-Eye Q AI-powered agent for network security dashboard
-
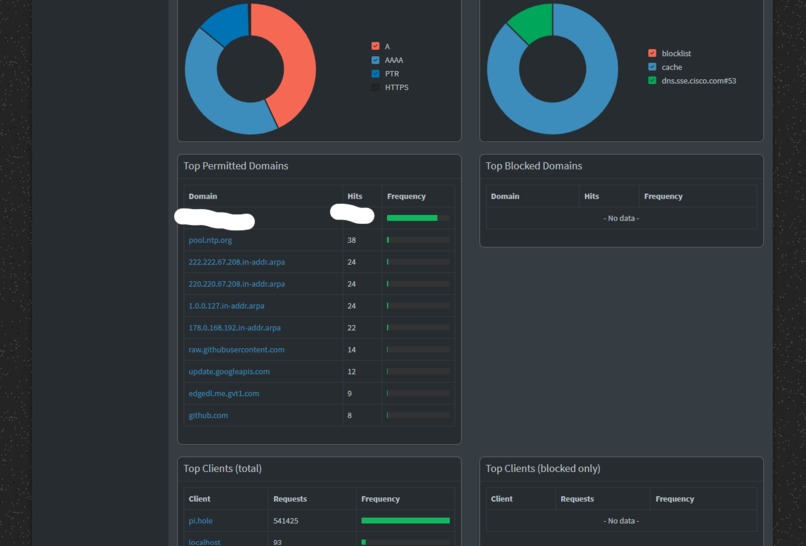
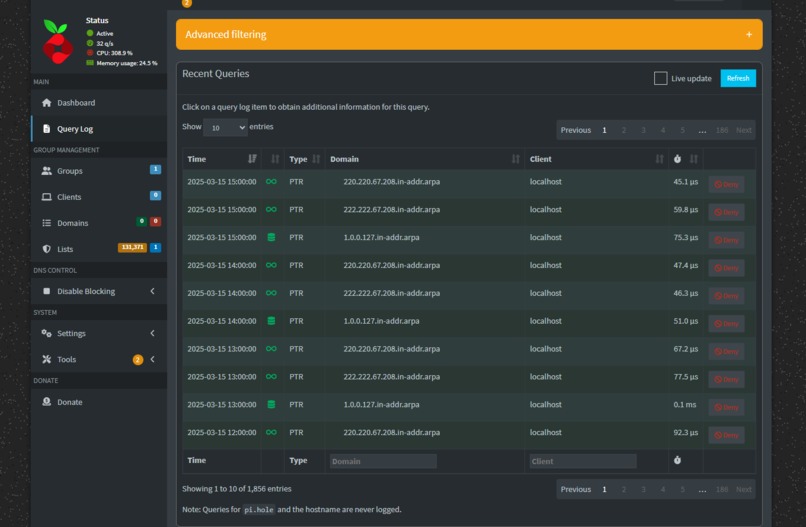
CyberNexus Pi-Eye Q AI-powered agent for network security dashboard (2)
-
CyberNexus Pi-Eye Q AI-powered agent for network security (3)
Elevator Pitches (Network Security & Mitigation Focus with Voice) - EMOJI ENHANCED:
- "CyberNexus Pi-Eye: Your local AI security agent for local network. 🤖 🗣️ Voice-command network defense, threat insights, & Pi-hole mitigation. Cyberpunk protection, hands-free! 🦾"
- "Secure your home network with CyberNexus Pi-Eye, the voice-activated AI agent. 🏠 🗣️ Raspberry Pi-powered threat mitigation, network analysis, & Pi-hole control. Cyberpunk security, spoken. 🌃"
- "CyberNexus Pi-Eye: AI-powered network security & mitigation, voice-controlled. 🛡️ 🗣️ Raspberry Pi agent for local threat insights & hands-on Pi-hole defense. Cyberpunk guardian. 👁️"
- "Defend your network locally with CyberNexus Pi-Eye! 🏘️ 🗣️ Command this AI agent for Raspberry Pi: network security, threat mitigation, & Pi-hole mastery. 🎛️ Cyberpunk style, voice control. 🎤"
- "Pi-Eye: CyberNexus - Your voice-activated AI agent for local network security. 👁️ 🗣️ Raspberry Pi-based threat mitigation, insights, & Pi-hole command. 📜 Cyberpunk defense, by voice. 🌃"
- "Defend your network locally with CyberNexus Pi-Eye! 🏘️ 🗣️ Command this AI agent for Raspberry Pi: network security, threat mitigation, & Pi-hole mastery. **Ready for quantum VPC deployment. 🎛️ Cyberpunk style, voice control. 🎤"** (Adding "Ready for quantum VPC deployment." as a concise hint at advanced infrastructure compatibility)
## Inspiration ✨
- Bullet Points:
- 💡 Growing need for accessible, user-friendly network security for home users.
- 🌃 Cyberpunk aesthetic and the idea of AI agents assisting in digital defense.
- 🍓 Desire to leverage Raspberry Pi's capabilities for practical, local security solutions.
- 😫 Frustration with complex network monitoring tools – wanted something intuitive.
- 🎤 Inspired by the power of voice interfaces in cyberpunk settings.
## What it does ⚙️
- Bullet Points:
- 🧠 Enhanced Intent Recognition: Implement more sophisticated NLP for natural language understanding (using Any AI/AGI agents you want further).
- 🚨 Proactive Threat Detection: Develop AI-driven anomaly detection for network traffic and system behavior.
- 🤖 Automated Mitigation Actions: Implement automated responses to security events (e.g., blacklist suspicious domains automatically).
- ⚙️ Customizable Security Policies: Allow users to define their own security rules and thresholds.
- 📜 Data Logging and Historical Analysis: Implement data persistence for trend analysis and security audits.
- 📊 Improved Visualizations: More advanced and interactive charts and dashboards for security data.
- 🤝 Community Features/Sharing: Potentially allow users to share custom commands or security rules (carefully, with security in mind).
- ✨ Refine Cyberpunk UI: Further enhance visual elements, animations, and potentially sound effects.
- 🌐 Quantum Infrastructure Compatibility: Develop deployment options optimized for quantum VPC environments, allowing users to leverage next-generation infrastructure for enhanced security and performance. Explore integration with quantum terminals for advanced user interaction and control.
- ⚛️ Quantum Encryption Integration (Exploration): Investigate and prototype the integration of quantum-resistant or quantum-key distribution methods to elevate network security to unprecedented levels, safeguarding against future cryptographic vulnerabilities.
## How we built it 🛠️
- Bullet Points:
- 🟦 Streamlit Framework: For rapid UI development and deployment as a web app.
- 🐍 Python Libraries:
psutil,speedtest-cli,requests,re,os,subprocessfor system and network data. - 🕳️ Pi-hole API: Direct API calls for Pi-hole management. (Pi-hole emoji again!)
- ✨ ** AI-agents:** For natural language command processing and response generation.
- 👂 PyAudio & SpeechRecognition: For voice input (STT).
- 🗣️ pyttsx3: For text-to-speech (TTS) output.
- 🎨 Cyberpunk CSS Theme: Custom CSS for visual style and animations.
- 🥧 Deployed on Raspberry Pi: Designed to run directly on the Pi-hole server for local access. (Raspberry Pi Pie emoji!)
## Challenges we ran into 🚧
- Bullet Points:
- 🔑 Pi-hole API Authentication: Figuring out the correct authentication method and handling session IDs (resolved with session-based auth).
- ⚠️ "Not Found" API Errors: Troubleshooting URL paths and ensuring correct API endpoint access (double slash issue, incorrect base URL).
- 💥
pyttsx3RuntimeError: Addressing the "run loop already started" error in Streamlit (solved by initializing engine inside function). - 📦 PyAudio Installation: Platform-specific challenges with PyAudio installation (Windows, macOS, Linux).
- 🐢 Balancing Functionality with Performance on Raspberry Pi: Optimizing code to run smoothly on resource-constrained Pi.
- 🤔 Intent Recognition Limitations: Basic keyword-based intent recognition – future improvement needed.
## Accomplishments that we're proud of 🎉
- Bullet Points:
- 🗣️ Functional Voice-Controlled Pi-hole Agent: Successful integration of voice commands for Pi-hole management.
- 📈 Real-time System and Network Monitoring: Accurate display of Pi's vital stats and network performance.
- 😎 Immersive Cyberpunk UI: Visually engaging and thematically consistent user experience.
- 🍓 End-to-End Raspberry Pi Integration: Seamless control and monitoring of the Pi-hole system it runs on.
- 🛡️ Practical Local Network Security Tool: Created a usable tool for home network security awareness.
- ✅ Overcoming API and TTS/STT Challenges: Successfully debugged and resolved complex integration issues.
## What we learned 📚
- Bullet Points:
- 🕳️ Deep Dive into Pi-hole API: Understanding session-based authentication and API endpoints. (Last Pi-hole emoji, I promise! 😄)
- ⚡ Streamlit for Rapid UI Development: Power and ease of use of Streamlit for web app creation.
- 🥧 Raspberry Pi System Internals: Learned more about accessing system metrics in Python. (Raspberry Pi again!)
- 🎧 Challenges of TTS/STT in Web Apps: Understanding event loop issues and platform-specific audio library setups.
- ❗ Importance of Clear Error Handling: Making API and system errors user-friendly.
- 🎨 Cyberpunk UI Design Principles: Applying thematic styling to enhance user engagement.
## What's next for CyberNexus Pi-Eye AI-powered agent for network security 🚀
- Bullet Points:
- 🧠 Enhanced Intent Recognition: Implement more sophisticated NLP for natural language understanding (using Any AI/AGI agents you want further).
- 🚨 Proactive Threat Detection: Develop AI-driven anomaly detection for network traffic and system behavior.
- 🤖 Automated Mitigation Actions: Implement automated responses to security events (e.g., blacklist suspicious domains automatically).
- ⚙️ Customizable Security Policies: Allow users to define their own security rules and thresholds.
- 📜 Data Logging and Historical Analysis: Implement data persistence for trend analysis and security audits.
- 📊 Improved Visualizations: More advanced and interactive charts and dashboards for security data.
- 🤝 Community Features/Sharing: Potentially allow users to share custom commands or security rules (carefully, with security in mind).
- ✨ Refine Cyberpunk UI: Further enhance visual elements, animations, and potentially sound effects.
Built With
- ai-agents
- pi-hole
- pyaudio
- python
- pyttsx3
- quantum
- raspberry-pi
- streamlit





Log in or sign up for Devpost to join the conversation.