-
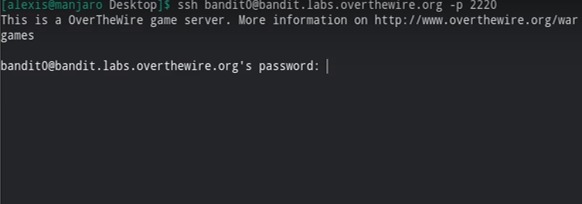
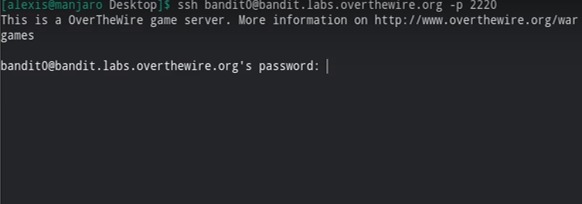
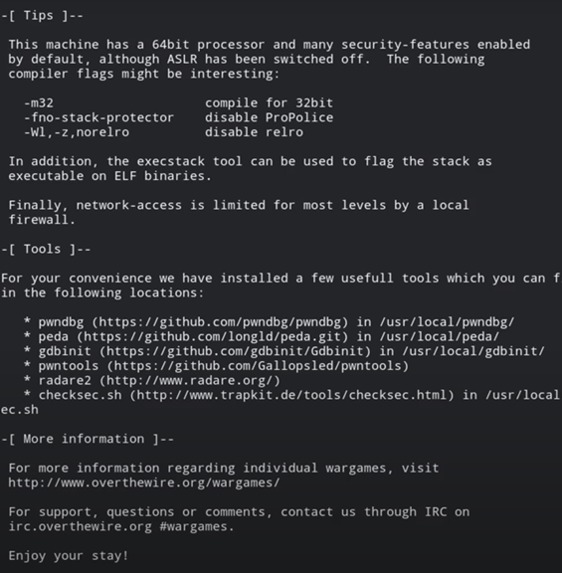
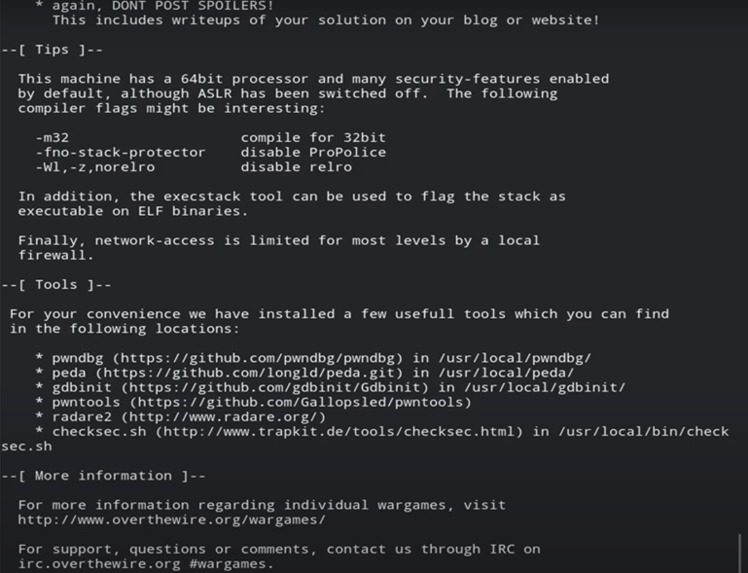
The host to which we to connected to was bandit.labs.overthewire.org, on port 2220.
-
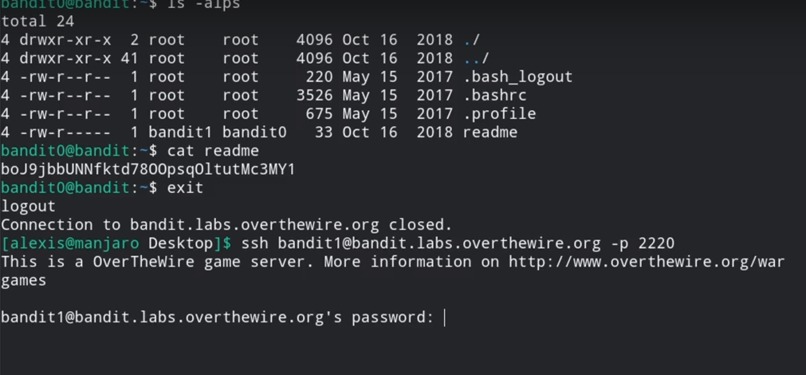
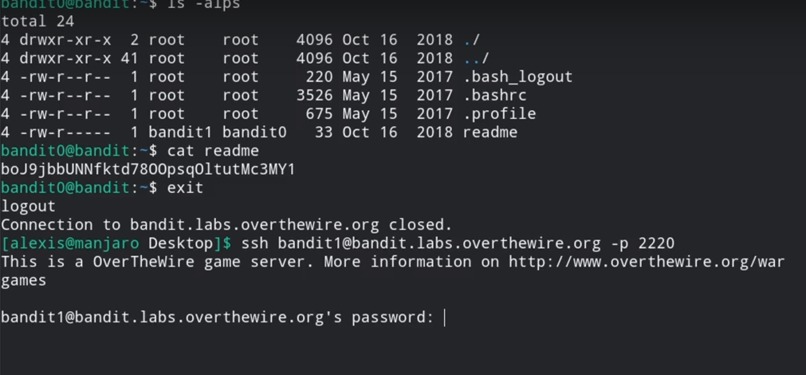
The password for the next level is stored in a file called - located in the home directory.
-
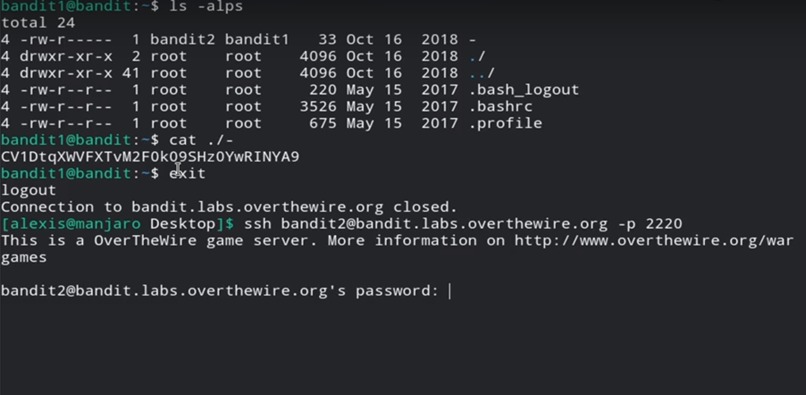
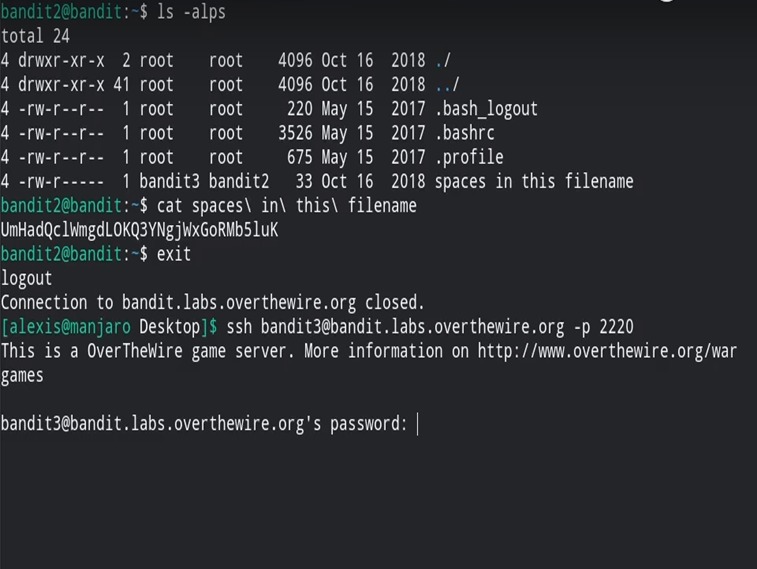
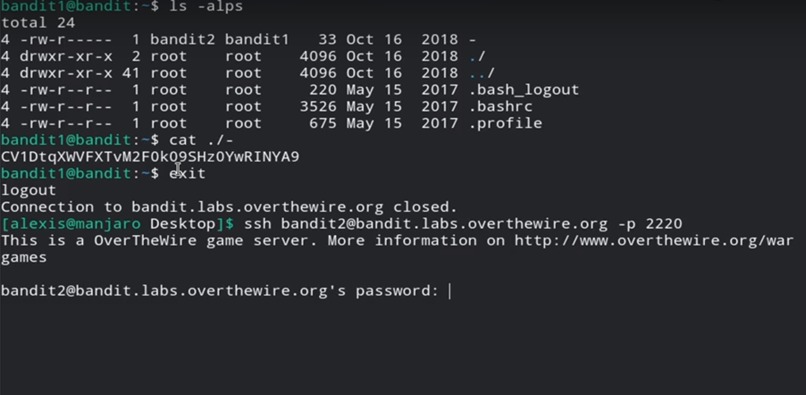
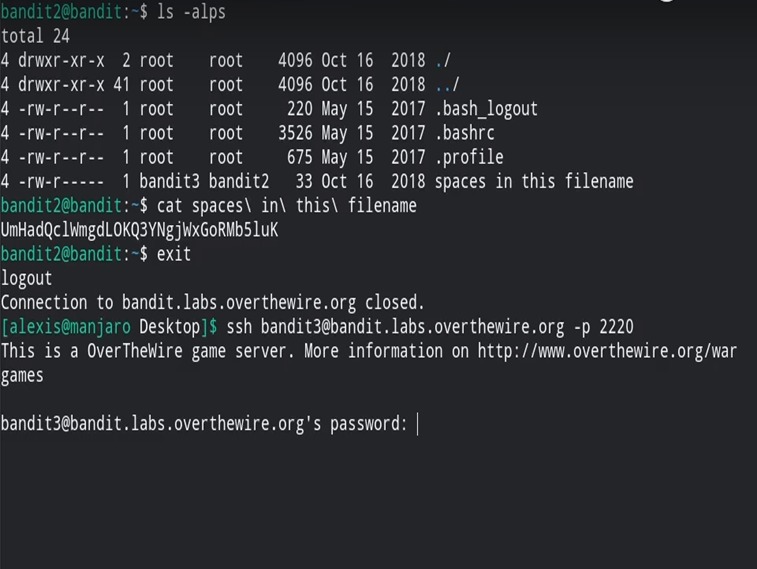
The password for the next level was stored in a file called spaces. In this filename was located in the home directory.
-
-
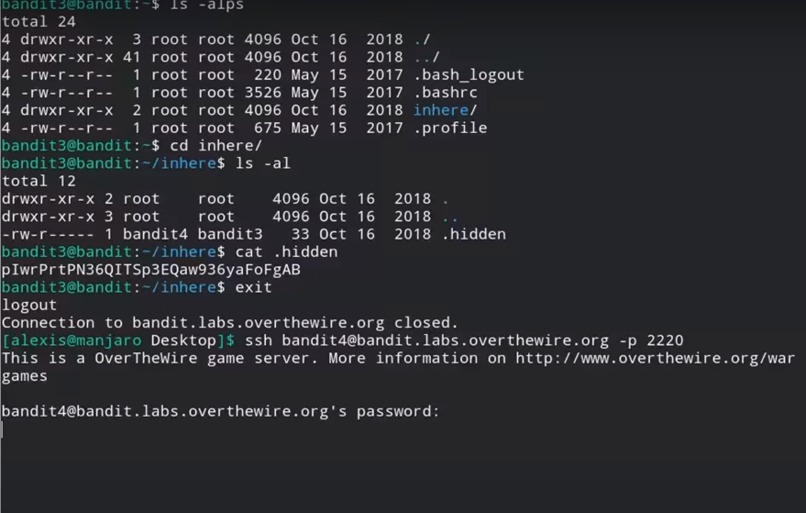
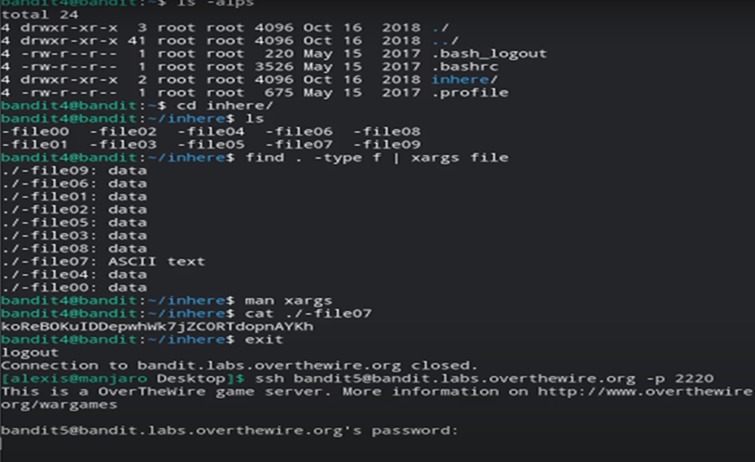
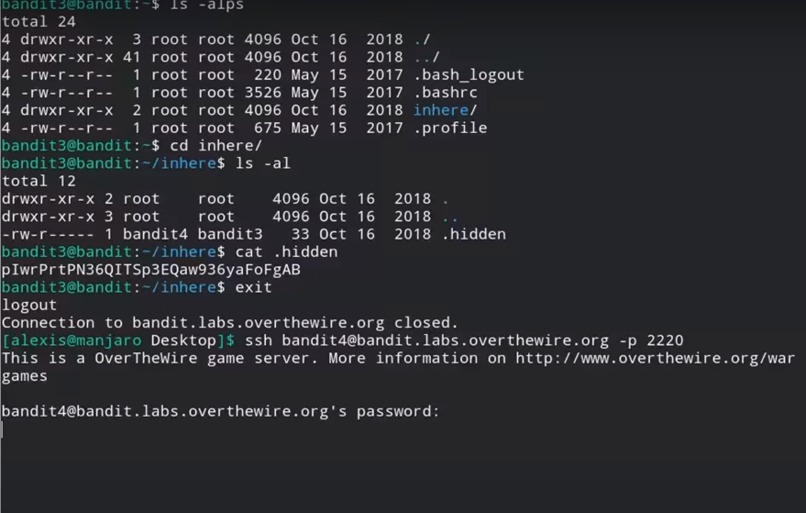
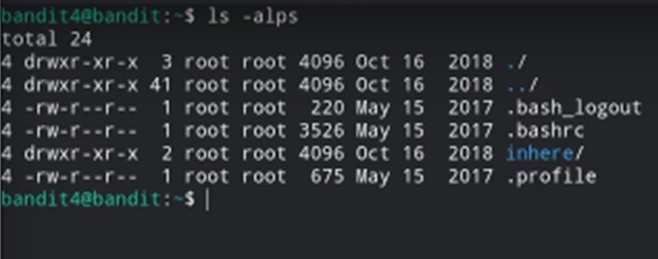
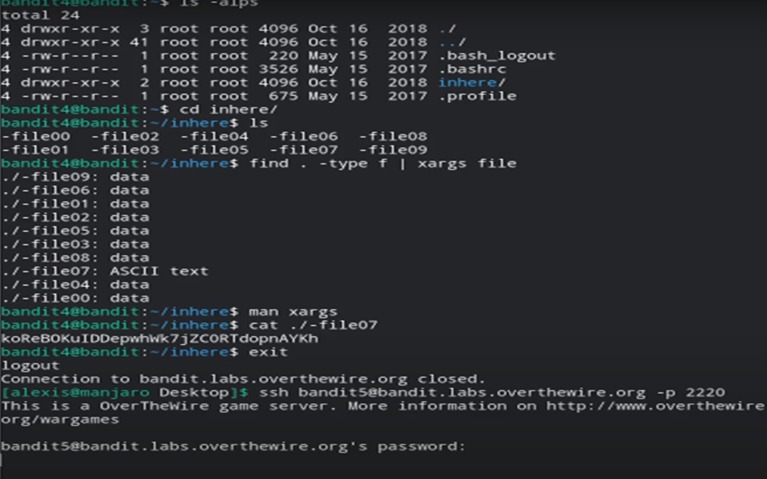
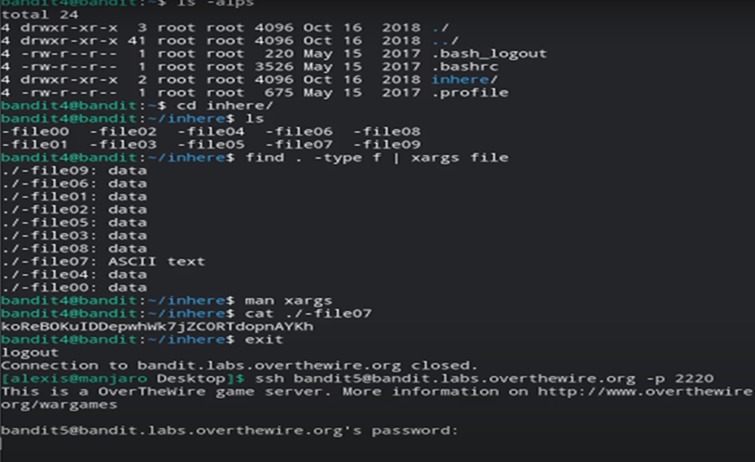
The password for the next level was stored in a hidden file in the inhere directory.
-
-
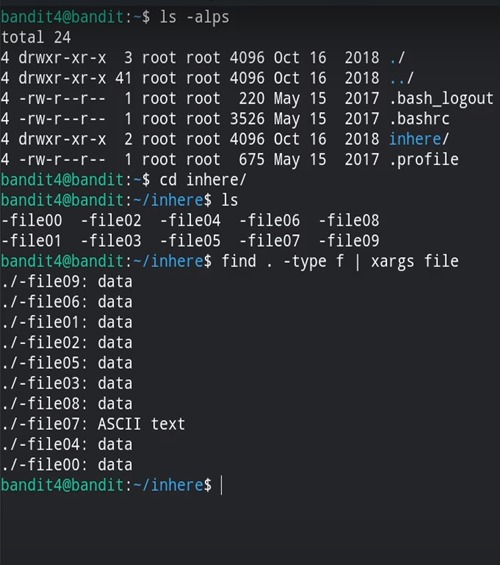
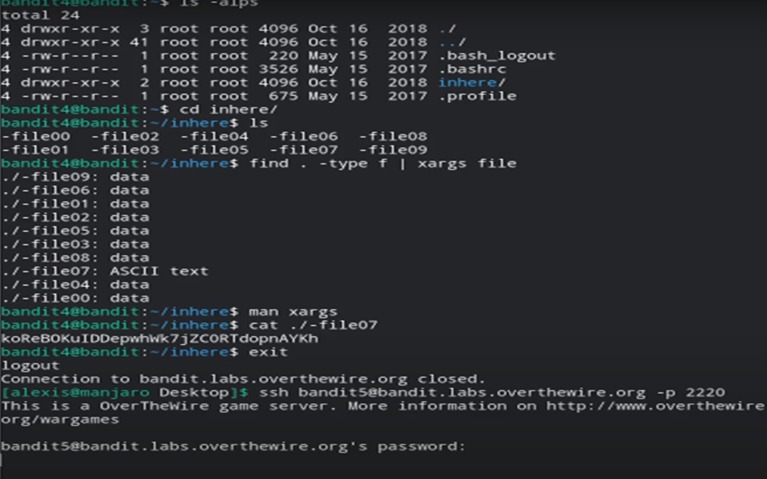
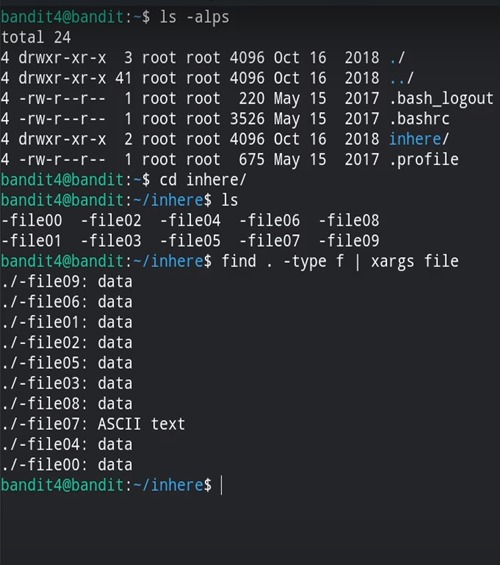
The password for the next level was stored in the only human-readable file in the inhere directory.
-
-
-
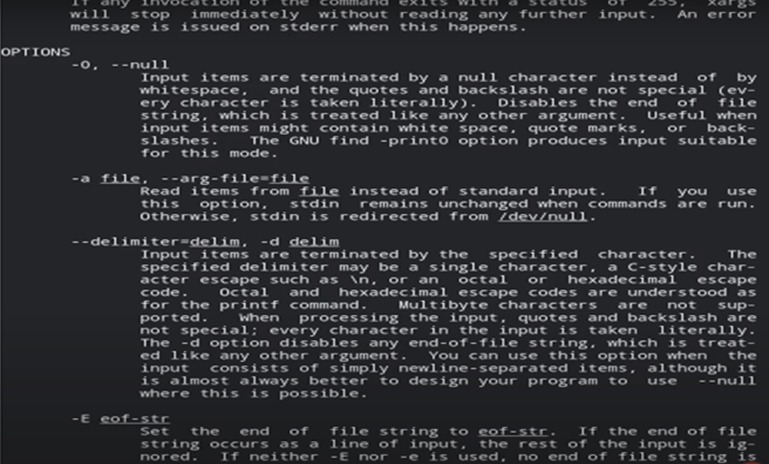
The password for the next level was stored in a file somewhere under the inhere directory.
-
They had all of the following properties: (i) Human-readable (ii) 1033 bytes in size (iii) not executable
-
-
The following essay talks about the 5 levels studied of the cyber war game Bandit offered by the OverTheWire Community. Followed by the conclusion in the end.
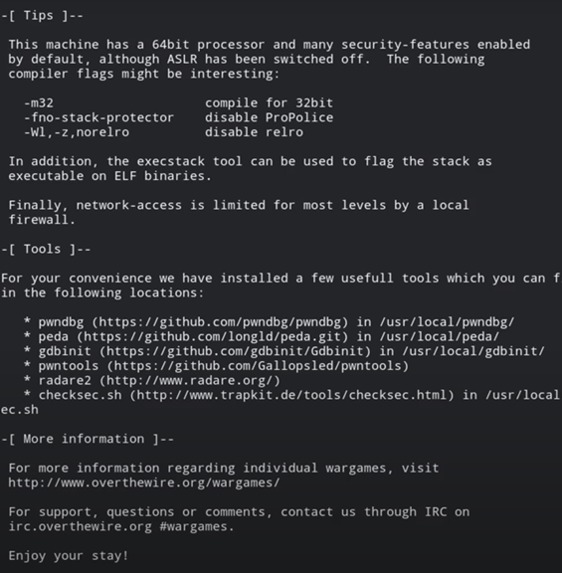
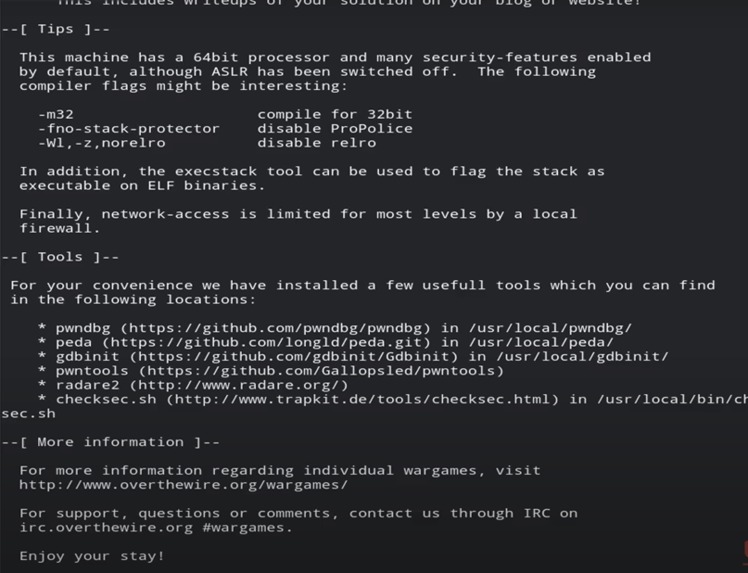
Introduction - Methodologies and Explanation Bash Console - Bash is a command processor that typically runs in a text window where the user types commands that cause actions. Bash can also read and execute commands from a file, called a shell script. Like most Unix shells, it supports filename globbing (wildcard matching), piping, here documents, command substitution, variables, and control structures for condition-testing and iteration. OverTheWire Wargames are a set of Capture the Flag (CTF) challenges offered by the OverTheWire Community .
The Cyber war games we used are taken up from the over thewire website: https://overthewire.org/wargames/
The games offered by the over the wire community are Bandit, Leviathan, Natas, Krypton, Narnia, Behemoth, Utumno and Maze.
The game we played: -
Bandit – This game is designed for absolute beginners. It teaches the basics one needs to know for playing the war games. It has in total 34 levels out of which we have done 5 levels.
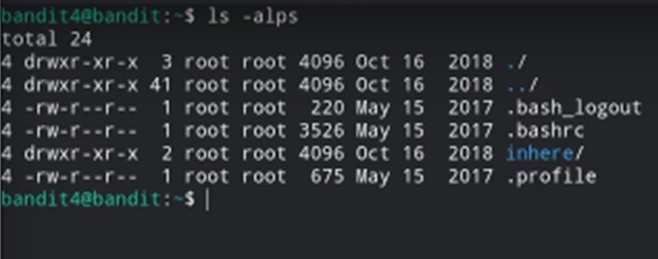
Level 0 – Log in using SSH. Connect to the host (bandit.labs.overthewire.org) on the port 2220. Now add the username and the password. Once it is done, we go to level 1.
Level 1 – In this level the password for the next level is stored in a file called readme that is located in the home directory. Use this password to log into bandit1 using SSH. Whenever you find a password for a level, use SSH (on port 2220) to log into that level and continue the game.
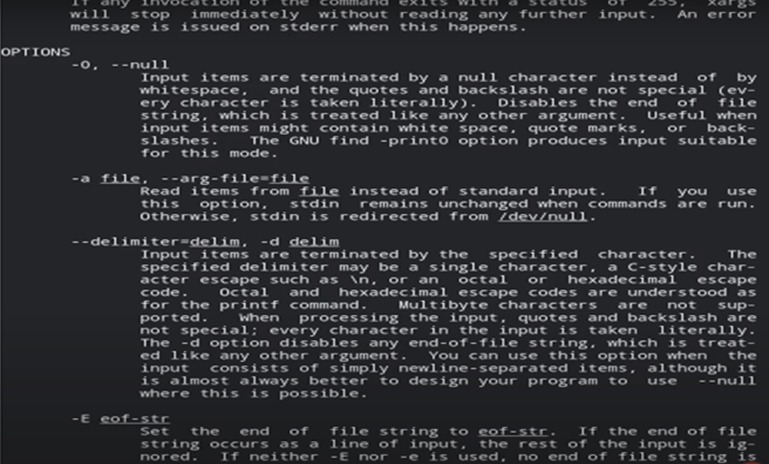
We use the commands like ls, cd, cat, file, du, find
Level 2 – In this level, again, the password for the next level is stored in a file called spaces in this filename located in the home directory. Again, the same commands will be used as in level 1.
Level 3 – In this level, The password for the next level is stored in a hidden file in the inhere directory. Again, the same commands will be used as in level 1.
Level 4 – The password for the next level is stored in the only human-readable file in the inhere directory. Again, the same commands will be used as in level 1.
Level 5 – The password for the next level is stored in a file somewhere under the inhere directory and has all of the following properties: (i) human-readable (ii) 1033 bytes in size (iii) not executable. Again, the same commands will be used as in level 1.
Conclusion and Inspiration
We have used the over the over wire cyber war games. In that we have done 0 to 5 levels of Bandit . The levels were challenging to do but at the same time they were wholesome adventurous and gave us a new outlook to cyber security as a beginner.
The commands for each level were executed using Bash console. To use the bash console, we had to setup the Linux ubuntu on virtual machine of our windows system. We tried online Bash console IDE too but we were unsuccessful in executing commands over there because the whole tool kit for bash console was not available on the IDE and so there was issues in running the command and so we had to install the setup on our systems.
Through this challenge we learnt how to work together in team, how to hold each other accountable for the promises we make, and we learnt that as a team we are one.
Log in or sign up for Devpost to join the conversation.