-
-
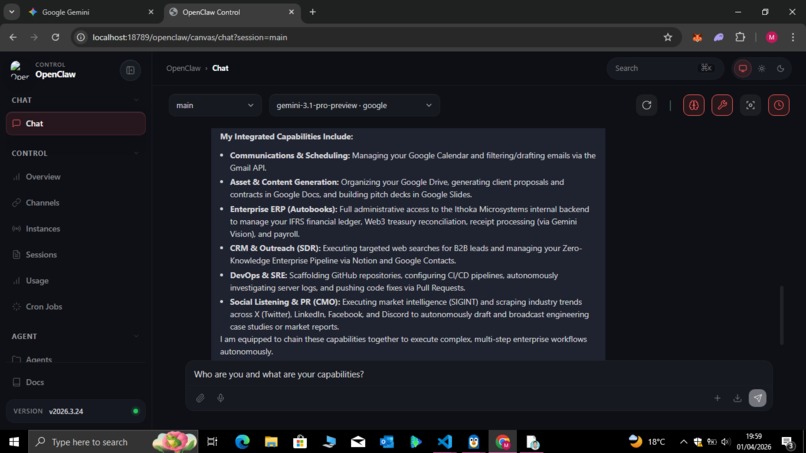
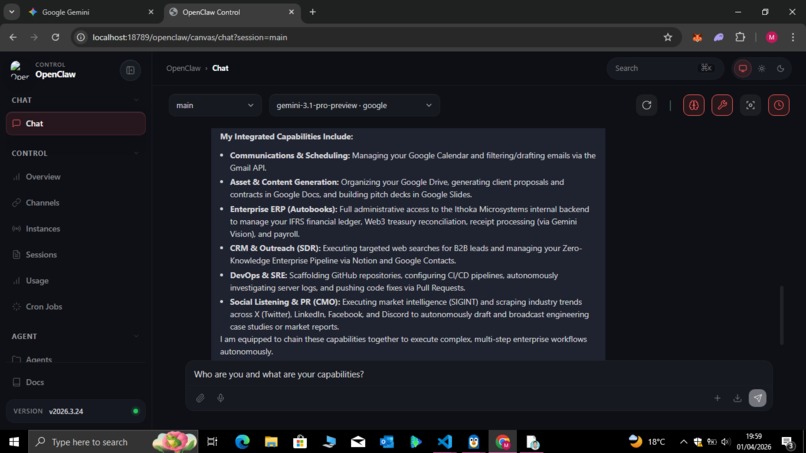
Integrated Agent Capabilities: Zero-Trust B2B Workflows
-
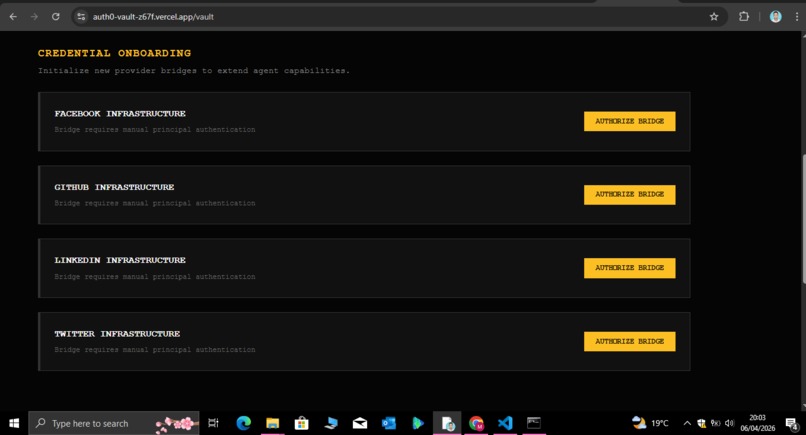
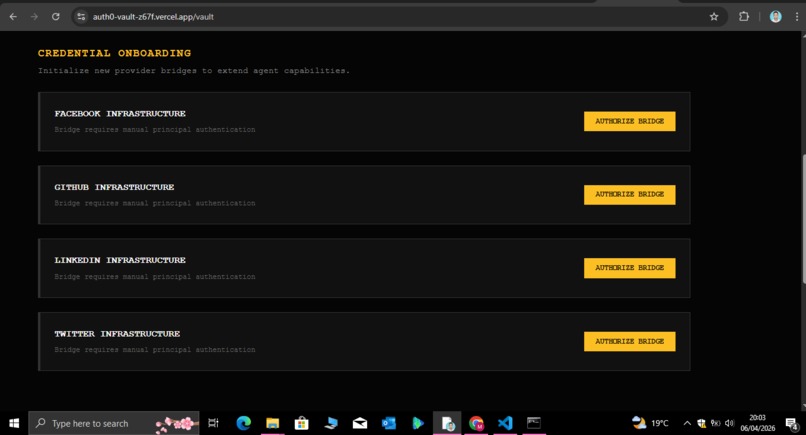
User Control: Granular Identity Bridge Onboarding
-
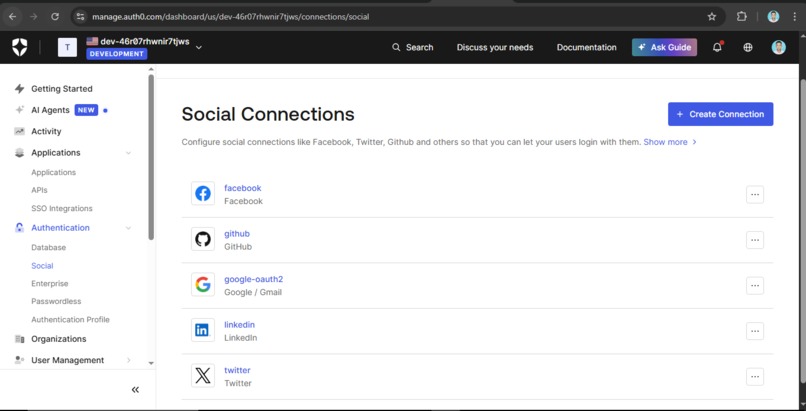
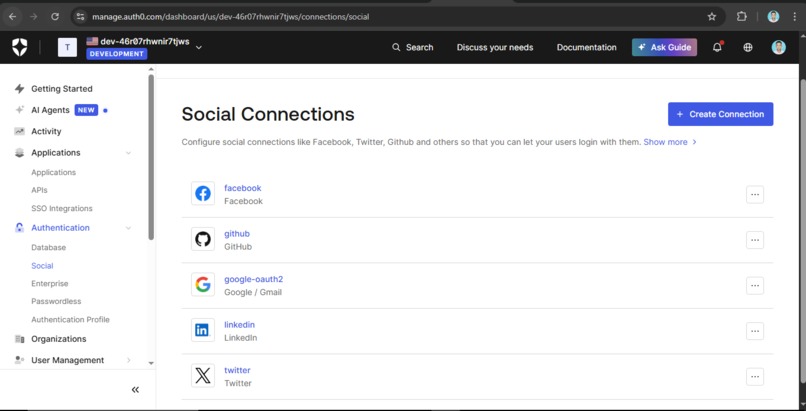
Connections: Auth0 Social Connections
-
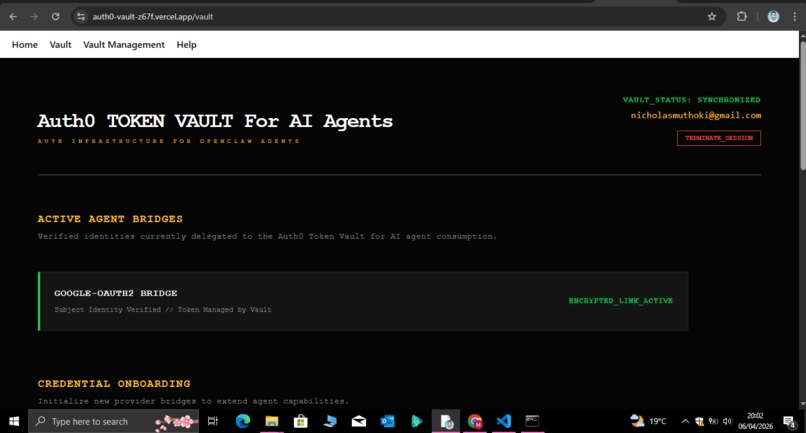
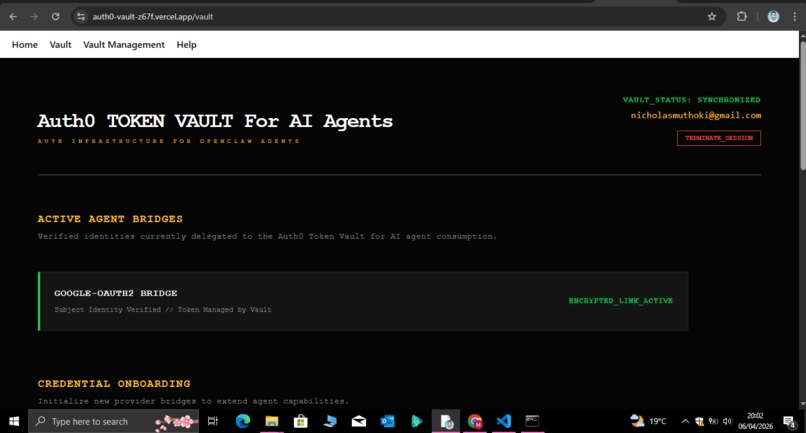
Vault Status: Synchronized Federated Identity Session
-
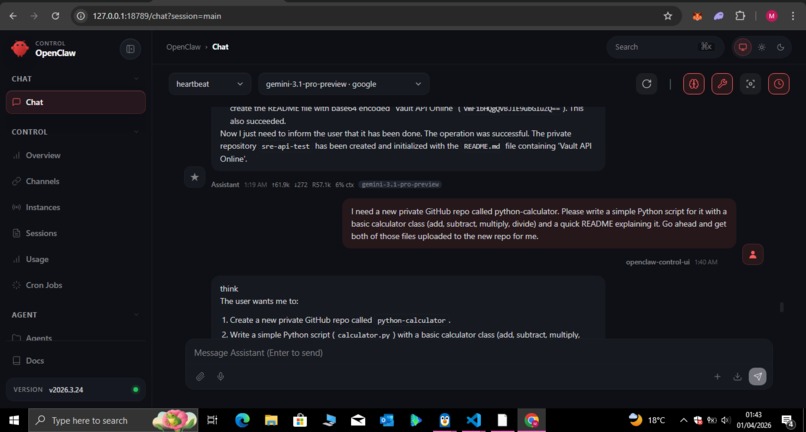
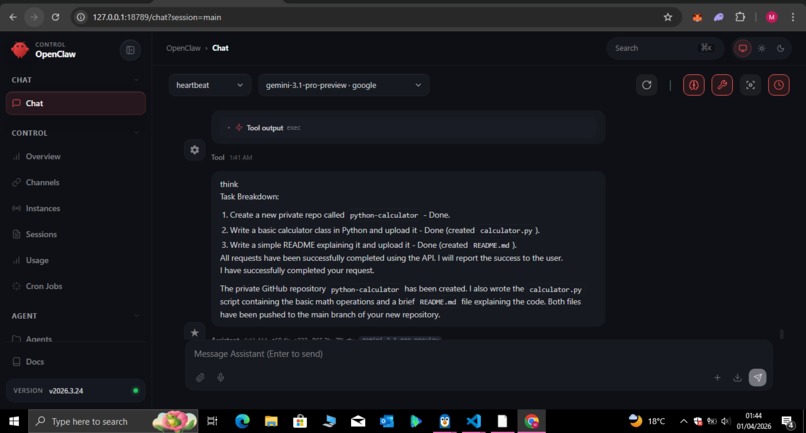
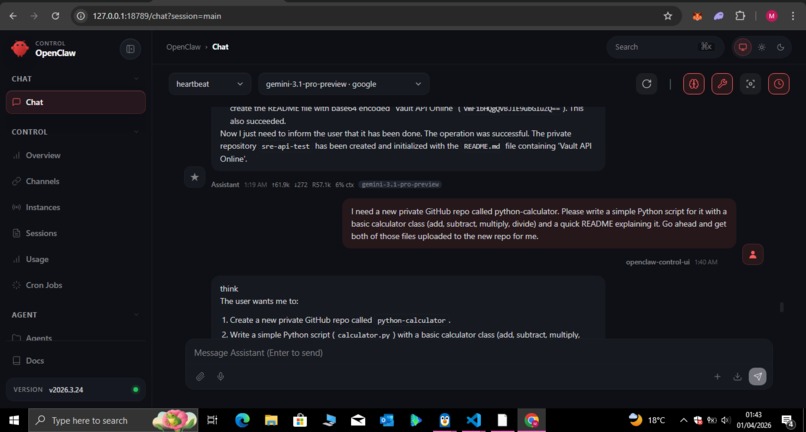
Autonomous Intent: Requesting Scoped Infrastructure Tasks
-
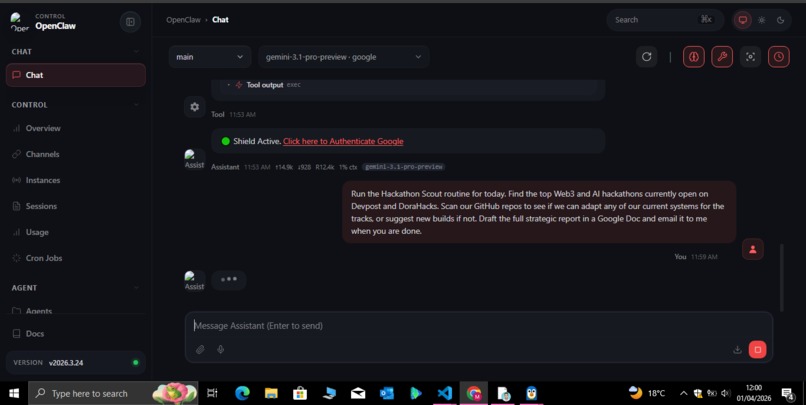
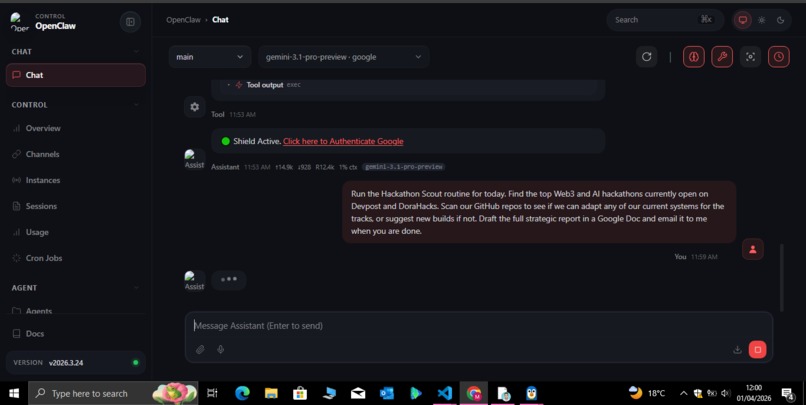
The Shield Intercept: Real-Time Authorization Demand
-
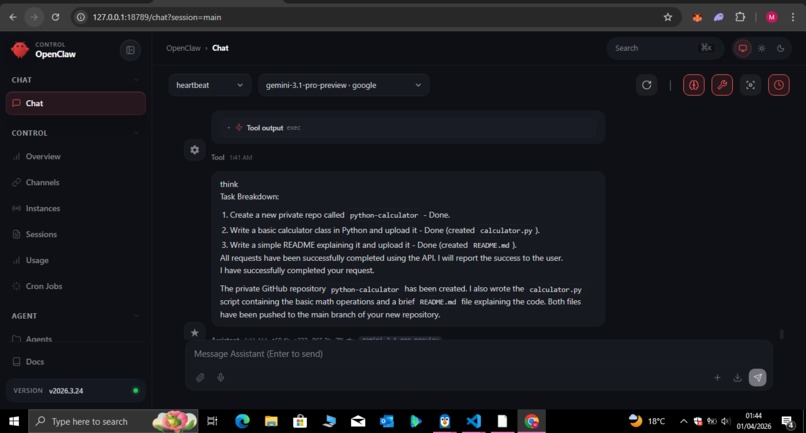
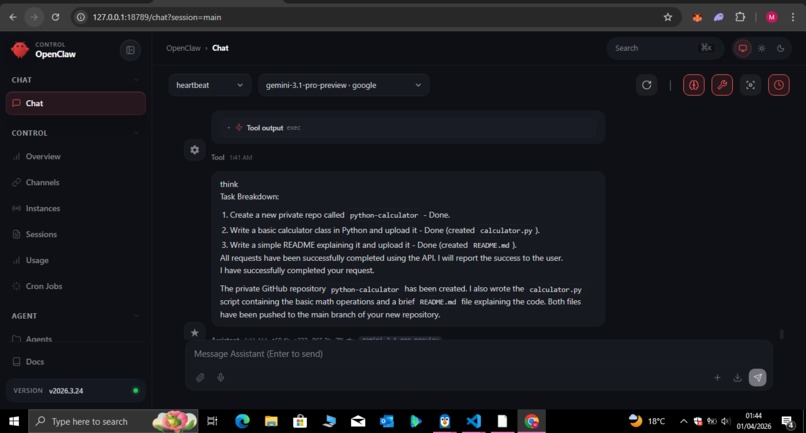
Secure Execution: Multi-Step Task Completion
-
Operational Metrics: Production-Ready Usage Analytics
ABOUT THE PROJECT
Inspiration
AI agents are becoming increasingly autonomous. They are handling finances, managing infrastructure, and interacting with real-world systems.
But there is a fundamental problem:
AI agents today are not safe to deploy.
Most systems rely on:
- Stored API keys
- Long-lived tokens
- Fully trusted execution environments
If compromised, these agents can:
- Leak credentials
- Perform destructive actions
- Access sensitive systems without restriction
We asked a critical question:
What if AI agents never had access to credentials at all?
CFO Shield was inspired by the need to build a secure identity layer for autonomous AI systems, not just smarter agents, but safer ones.
What it does
CFO Shield is a zero-trust identity and execution layer for AI agents, powered by Auth0 Token Vault.
It enables AI agents to:
- Act on behalf of users
- Access real-world services (Google, GitHub, etc.)
- Execute workflows autonomously
Without ever exposing API keys or credentials
Core Model
Instead of storing tokens inside the agent:
- Credentials are stored in a secure vault
- The agent sends requests to a proxy (Vault API)
- The vault performs real-time token exchange (RFC 8693)
- A short-lived access token is injected per request
This ensures:
- Tokens are never stored locally
- Access is ephemeral and scoped
- Permissions can be revoked instantly
How we built it
The system is composed of three core components:
1. Next-Vault (Frontend)
- Built with Next.js + TypeScript
- Handles Auth0 authentication
- Displays connected providers (Google, GitHub, etc.)
- Syncs subject tokens securely
2. Vault API (Zero-Trust Middleware)
- Built in Go
- Implements the Token Vault pattern
- Performs RFC 8693 Token Exchange
- Injects access tokens into outbound requests
- Enforces policies (e.g., blocking DELETE operations)
- Uses thread-safe session management (RWMutex) for performance
3. OpenClaw Workspace (AI Agent Runtime)
- Sovereign/local AI agent environment
- Executes workflows via Bash + TypeScript “skills”
- Routes ALL external requests through the vault
- Contains zero credentials or tokens
Key Innovation
Zero-Credential AI
- No API keys in memory
- No stored OAuth tokens
- Agent operates in restricted mode by design
Secure Delegation (RFC 8693)
- Subject token represents user identity
- Vault exchanges it for scoped access tokens
- Every request gets a fresh credential
Policy Enforcement Layer
Even with valid access:
- Sensitive operations can be blocked
- Permissions enforced centrally
- No privilege escalation possible
What it can do
The agent can autonomously:
- Manage files (Google Workspace)
- Perform DevOps actions (GitHub PRs, repos)
- Execute financial workflows
- Run CRM automations (Notion)
- Perform research and analysis
- Automate communications
All actions are executed securely through the vault.
Challenges we ran into
- Implementing RFC 8693 Token Exchange correctly
- Ensuring zero token exposure in the agent runtime
- Maintaining low-latency real-time exchange
- Designing a system where security does not depend on trusting the agent
What we learned
We discovered that Auth0 is not just an authentication tool.
It is a secure delegation authority for autonomous systems
Key insight:
The subject token becomes a delegation primitive—not just an identity artifact
This enables:
- Continuous autonomous execution
- Zero credential exposure
- Real-time access control
Impact
CFO Shield enables:
- Safe enterprise AI agents
- Autonomous financial systems
- Secure DevOps automation
- AI copilots with real-world permissions
Without secure identity delegation, autonomous AI cannot be safely deployed.
Future Work
- Fine-grained permission dashboards
- Multi-agent coordination
- Real-time monitoring + audit logs
- Enterprise RBAC systems
Conclusion
CFO Shield is not just an AI tool.
It is a foundational security layer for the future of autonomous AI.
Bonus Blog Post: The Trust Gap in the Agent-Operated Enterprise
The Inevitability of Autonomous Action
We are witnessing a fundamental shift in the AI landscape: the transition from models that "think" to agents that "do." This evolution toward the Agent-Operated Enterprise is inevitable, as businesses seek to automate complex B2B workflows—from financial reconciliation to DevOps orchestration.
However, this transition has exposed a critical systemic weakness that the industry has largely ignored:
The Trust Gap.
While building CFO Shield, our team was forced to confront a core architectural dilemma:
How do you preserve the local sovereignty of an agent like OpenClaw while allowing it to interact with high-stakes enterprise systems like Google Workspace or GitHub?
The Journey: From Stored Keys to Federated Identity
Our initial development phase followed the industry's standard, albeit flawed, pattern: embedding long-lived API keys and OAuth tokens directly into the agent’s environment.
While functional for a "Hello World" demo, it immediately failed the enterprise security test.
We realized we were creating a dangerous “all-or-nothing” trust model.
If the agent’s local runtime were ever compromised, the entire organizational infrastructure would be exposed.
For any serious enterprise application, this level of risk is not just unacceptable—it is a non-starter.
Our breakthrough came when we integrated the Auth0 for AI Agents Token Vault.
We completely scrapped our initial credential model and redesigned the architecture around a delegated execution pattern, leveraging the RFC 8693 Token Exchange standard so that the agent never directly touches a permanent credential.
Overcoming the Technical Hurdle
The primary technical hurdle was implementing a high-performance security middleware in Go that could:
- Intercept agent requests
- Perform real-time token swaps
- Avoid introducing latency that would break the agent's reasoning loop
By using thread-safe session management and optimizing concurrent token exchanges within our vault-api service, we achieved a:
"Cryptographic Air-Gap."
Every request from the agent is now ephemeral.
The agent sends an intent to our proxy, which:
- Validates the user’s authenticated Subject Token against the Auth0 Token Vault
- Injects a short-lived, scoped access token into the outbound request
The credential exists for milliseconds—only long enough to authorize the specific action—and then it vanishes.
The Key Insight: Identity as a Control Layer
The most significant realization of our journey was that:
Identity is the only viable control layer for autonomous AI.
By shifting from stored credentials to continuous authorization, we transformed our AI from a risky automation tool into a trusted execution layer.
CFO Shield proves that when intelligence is decoupled from identity, businesses can finally automate with confidence.
We aren't just building smarter AI.
We are building a secure foundation for the future of agent-run commerce.
By leveraging Token Vault, we demonstrated a fully compliant, enterprise-ready implementation of Auth0’s delegated identity model for autonomous agents, aligning directly with the hackathon challenge.
Built With
- auth0
- bash
- gcp
- github-api
- go
- google-workspace-api
- next.js
- node.js
- openclaw
- rfc-8693
- token-vault
- typescript
- vercel
Log in or sign up for Devpost to join the conversation.