-
-
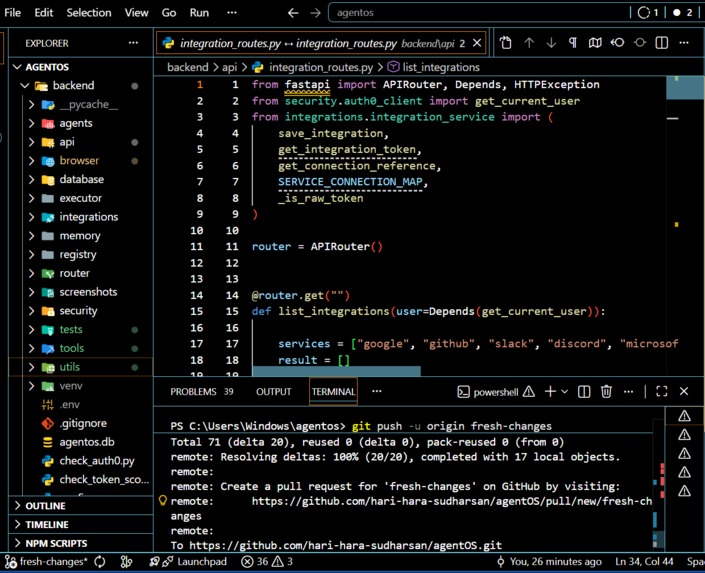
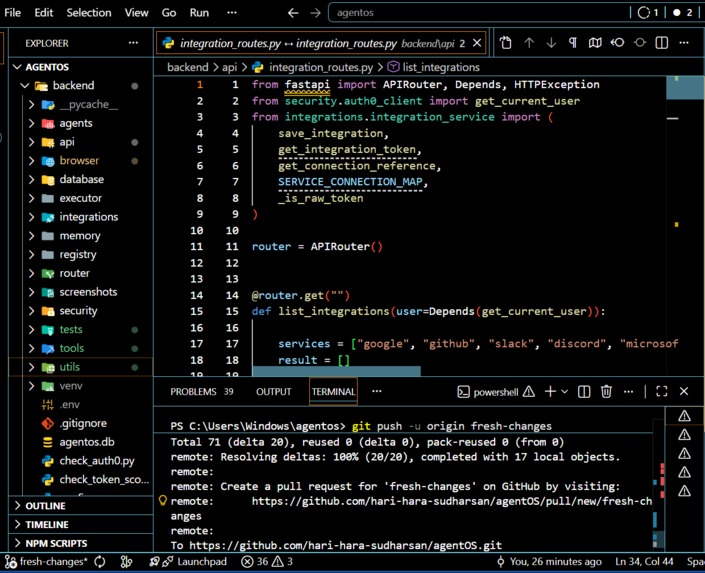
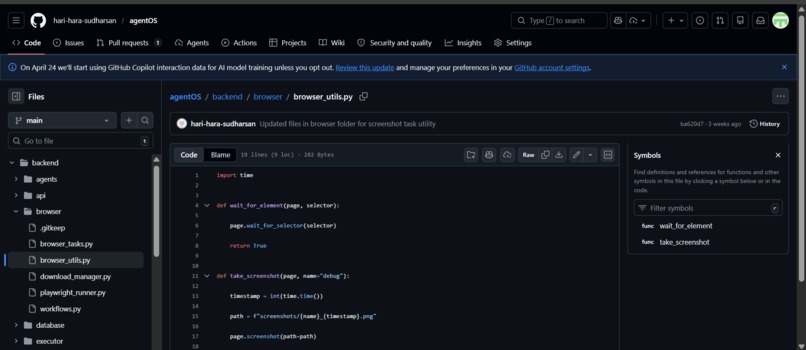
Codebase for AgentOS
-
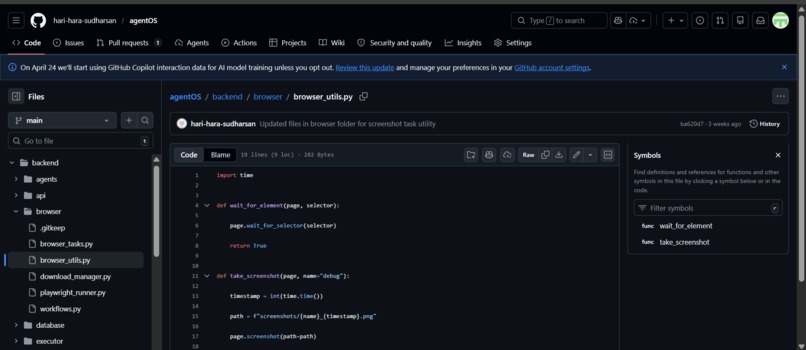
Github files for AgentOS
-
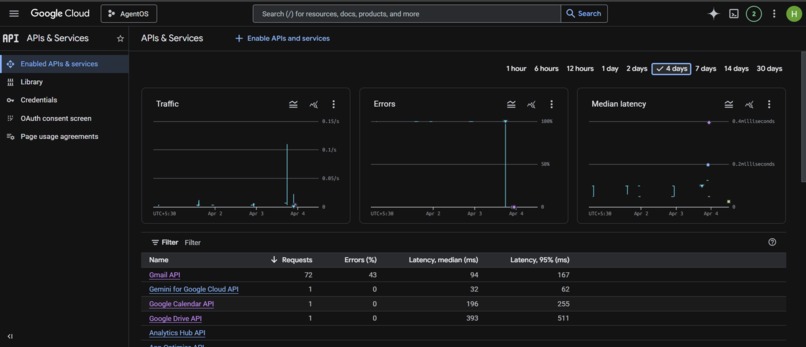
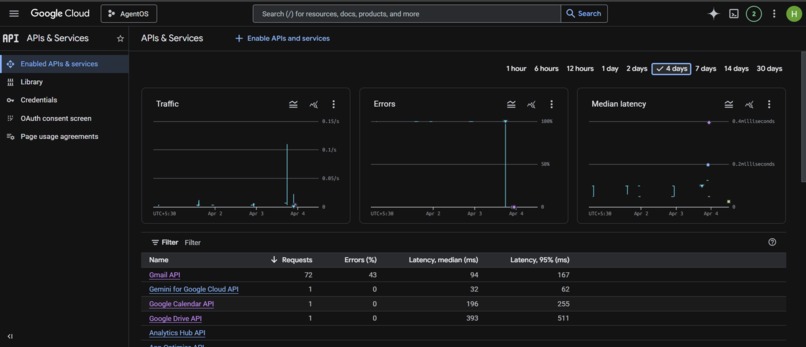
Metrics for AgentOS on google cloud
-
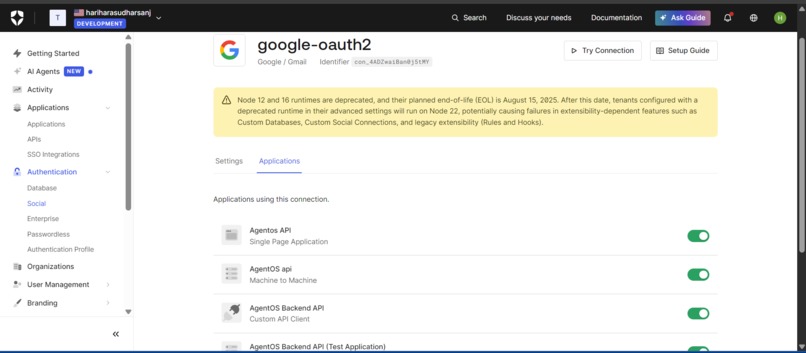
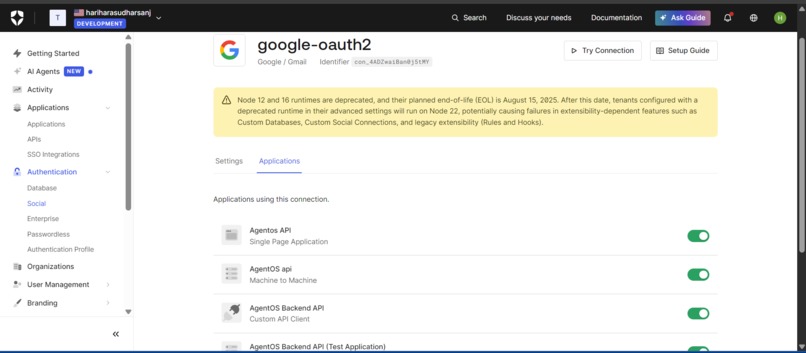
Connections for AgentOS on Auth0
-
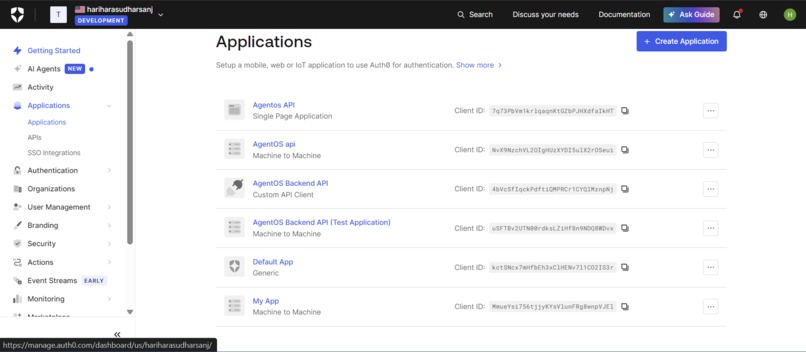
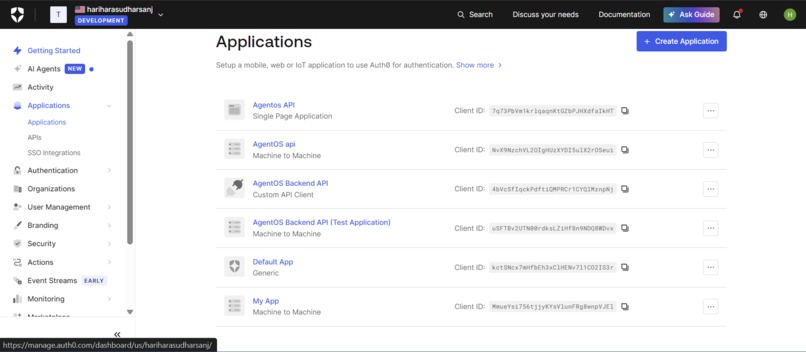
Application Implemetation for AgentOS on Auth0
-
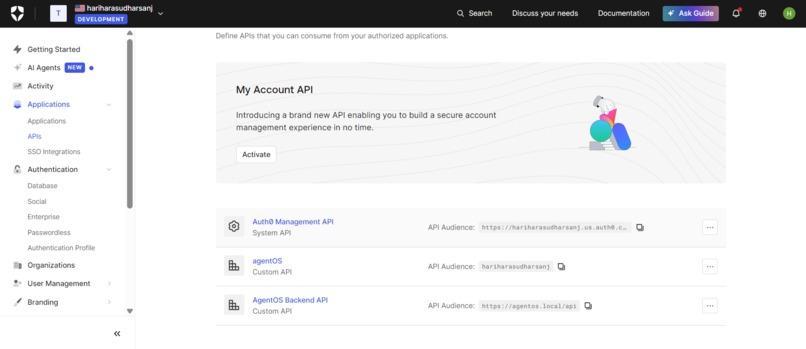
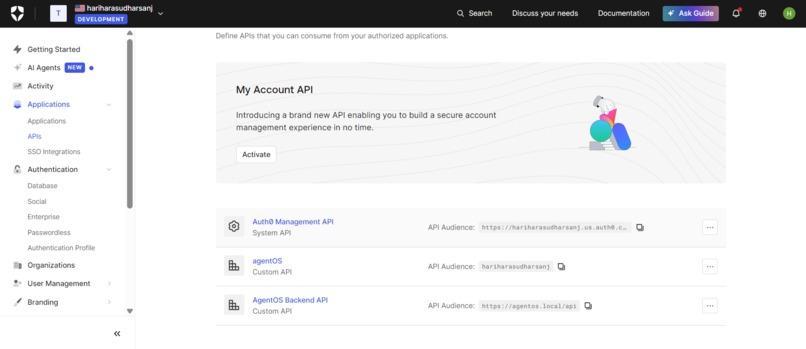
API's for AgentOS on Auth0
-
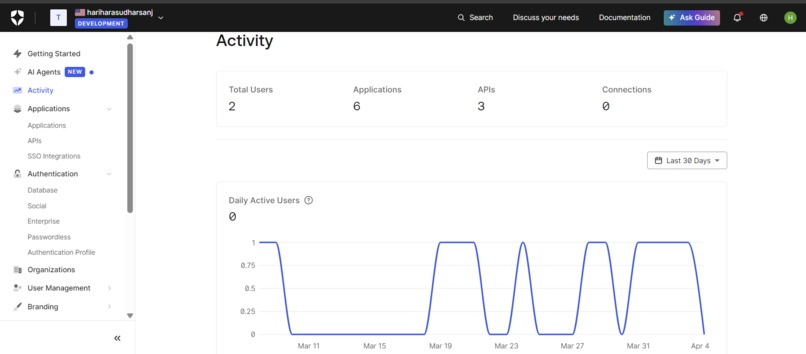
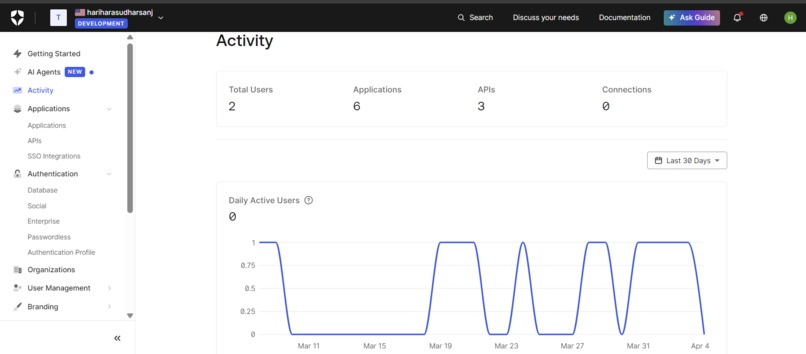
Our Activity for AgentOS on Auth0
-

Login for AgentOS
-
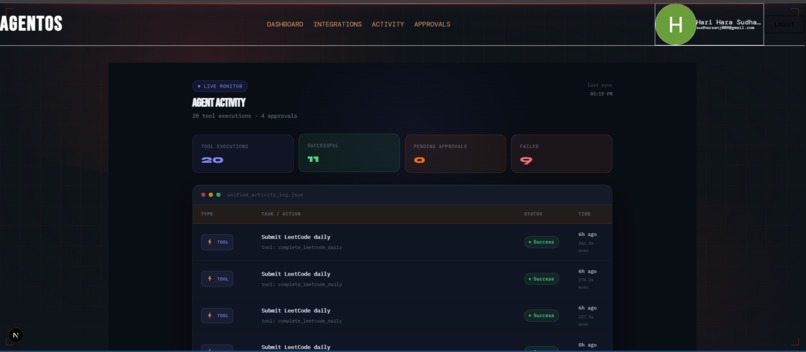
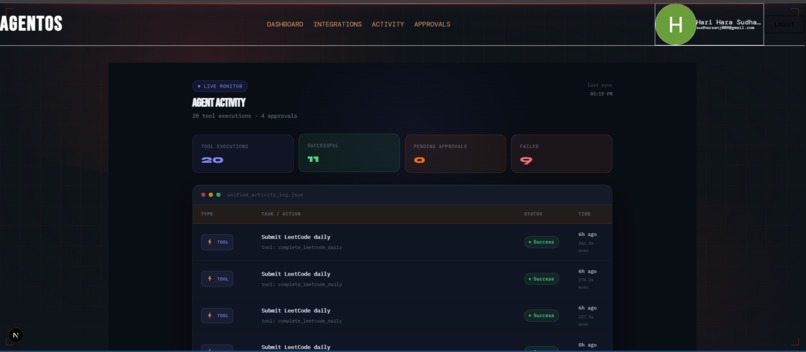
Activity of AgentOS
-
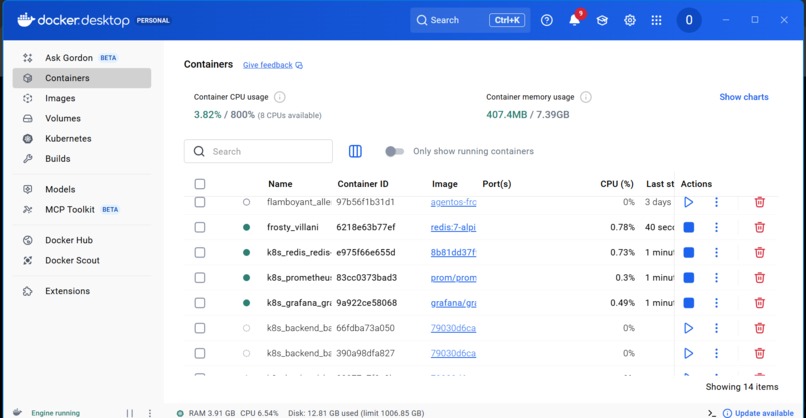
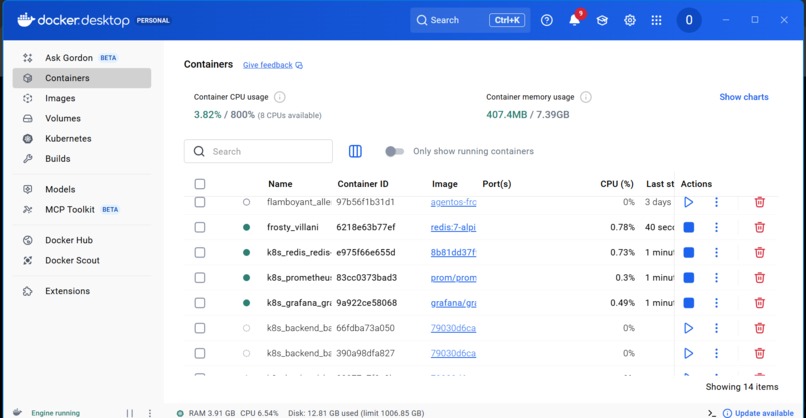
Docker Containerization , Kubernetes Orchestration , Grafana and Prometheus Monitoring for AgentOS
-
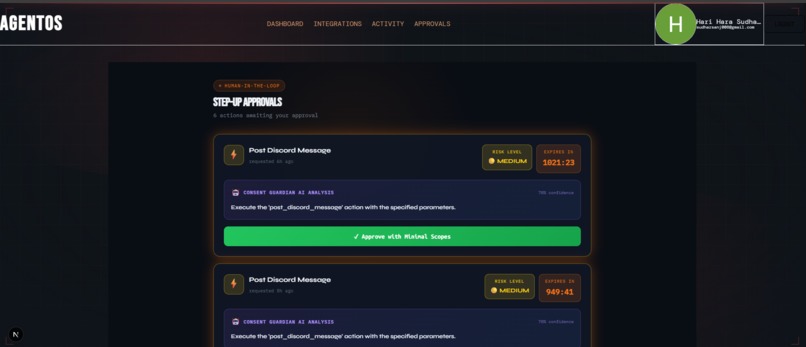
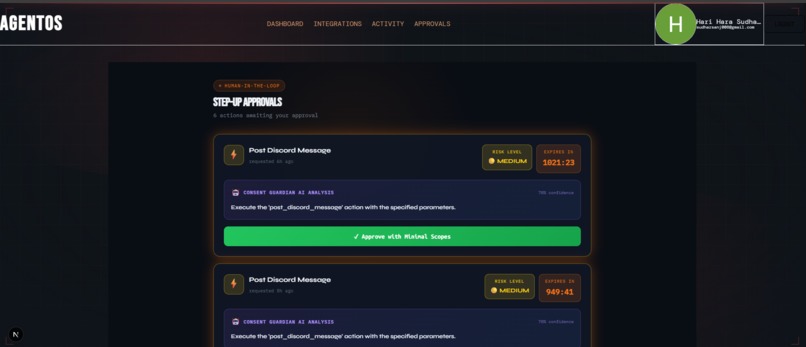
Human In the Loop for High Stake Actions
-
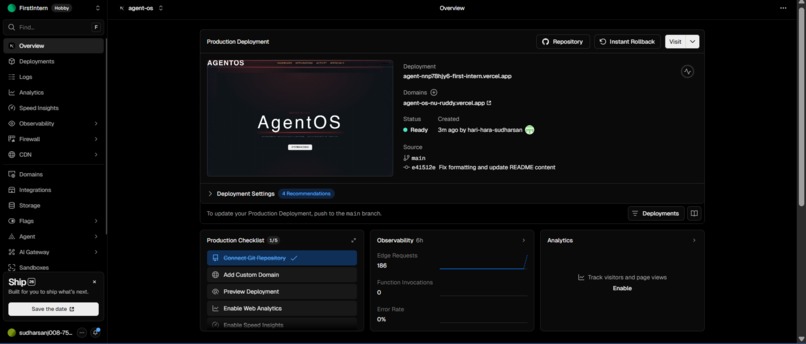
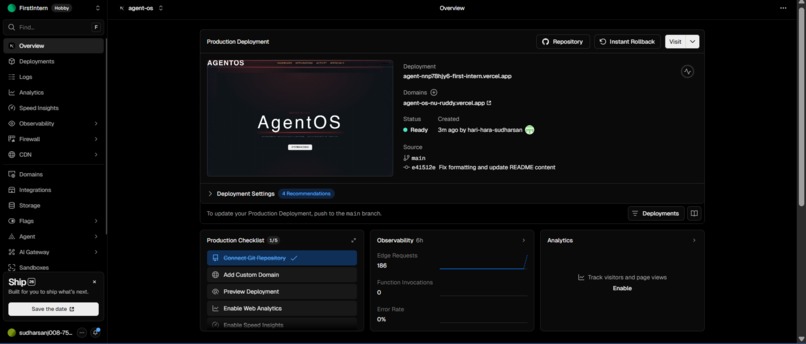
Vercel deployment for AgentOS
AgentOS: Secure Sovereign AI Agent Framework
Tagline:
"Restricted Local AI. Unrestricted Access. Full User Control — Powered by Auth0 Token Vault."
Inspiration
The explosion of sovereign local AI models like OpenClaw inspired this project. Users are increasingly running powerful agents locally on their machines (or even in browsers) to protect privacy and avoid cloud exposure. Yet these agents remain isolated — they can't safely interact with the outside world (Gmail, Calendar, GitHub, Slack) without risking credential leaks or losing user control.
The Authorized to Act Hackathon gave the perfect opportunity: what if we built a secure intermediary that keeps OpenClaw in strict restricted/sandbox mode while letting it act responsibly through Auth0 Token Vault?
We wanted to prove that local sovereign AI can be both powerful and trustworthy. Our tagline became:
"AgentOS: Securely connecting restricted OpenClaw agents to external APIs through Auth0 Token Vault — giving users full control and visibility."
What it does
AgentOS is a production-ready secure intermediary that bridges restricted local sovereign AI (OpenClaw) with external services.
- Users log in and connect accounts (Google, GitHub, Slack, etc.) via OAuth.
- The LangGraph-powered agent processes natural language requests and decides which tools to call.
- Every external API call goes through Auth0 Token Vault — never exposing raw tokens.
- High-stakes actions trigger step-up authentication or async CIBA (human-in-the-loop approval with clear binding messages).
- A polished dashboard gives users full visibility: connected accounts, plain-English scopes, consent timestamps, and one-click revocation.
- Real-time observability via Prometheus + Grafana shows token exchange latency, error rates, approval flows, and more.
OpenClaw stays fully restricted — AgentOS is the only secure gateway to the outside world.
Key Innovations
1. Scope Weaver — Intelligent Adaptive Scoping Engine
Before any action, AgentOS pauses and consults OpenClaw to dynamically generate the exact minimal scopes needed. OpenClaw returns recommended scopes, plain-English explanation, risk level, and scope evolution score. Users see a clear approval card with OpenClaw’s reasoning. Only the precise recommended scopes are requested from Token Vault.
2. Shadow Simulator — Parallel Safe Preview Engine
For every external or high-stakes action, AgentOS runs a parallel shadow simulation using OpenClaw to predict side effects, risks, and safer alternatives. Users get a "What-If Preview" showing predicted actions and suggestions. Execution happens only after explicit approval and Token Vault exchange.
These innovations create an intelligent, self-auditing Agent Operating System that goes far beyond typical agent projects.
How we built it
We built AgentOS with Next.js 15 (frontend) + FastAPI (backend) and LangGraph for agent orchestration. The heart of the project is Auth0 Token Vault:
- Connected Accounts flow for OAuth consent.
- Strict token exchange using the official
urn:auth0:params:oauth:grant-type:token-exchange:federated-connection-access-tokengrant. - No raw access or refresh tokens ever touch our infrastructure — only non-sensitive connection references are stored.
We added real step-up auth, async CIBA approval, Scope Weaver, and Shadow Simulator. For production readiness, we containerized everything with Docker + Docker Compose, added comprehensive Prometheus metrics, and prepared Kubernetes manifests with Horizontal Pod Autoscaler.
The full stack runs with one command: docker compose up --build. OpenClaw communicates only through our secure bridge.
Challenges we ran into
- Enforcing pure Token Vault paths while rejecting unsafe fallbacks and raw token inputs (400 errors).
- Implementing real step-up + CIBA flows without breaking LangGraph state.
- Making OpenClaw-powered Scope Weaver and Shadow Simulator fast enough for real-time consent and preview.
- Balancing polished UX with enterprise-grade security and observability under hackathon time constraints.
Accomplishments that we're proud of
- Achieved strict Token Vault compliance with zero raw tokens in DB, logs, or runtime.
- Delivered intelligent innovations (Scope Weaver + Shadow Simulator) that make AgentOS self-optimizing and self-auditing.
- Built a complete production-aware stack: Docker, Prometheus/Grafana, and Kubernetes-ready deployment.
- Created transparent user control with OpenClaw-powered explanations and one-click revocation.
- Demonstrated multi-provider tool chaining with explicit permission boundaries.
The project now scores strongly across all six judging criteria — especially Security Model, User Control, Technical Execution, and Insight Value.
What we learned
- Auth0 Token Vault is a game-changer — it removes the burden of manual token management while enforcing least-privilege by design.
- Observability (Prometheus/Grafana) reveals critical patterns like consent bottlenecks and token-exchange latency that would otherwise go unnoticed.
- Human-in-the-loop mechanisms (CIBA + step-up) combined with OpenClaw-powered intelligence build real user trust and surface important authorization patterns for the AI agent community.
- DevOps practices (Docker + K8s + monitoring) can be added to a hackathon project without sacrificing speed, making the submission truly enterprise-ready.
What's next for AgentOS
We plan to open-source AgentOS as a full framework for secure sovereign AI agents. Future enhancements include:
- Fine-grained authorization with OpenFGA
- Multi-agent orchestration and advanced anomaly detection
- One-click deployment templates for Kubernetes and serverless
Ultimately, we want to make secure, user-controlled agentic AI accessible to every developer — so local sovereign agents can safely act in the real world.
Bonus Blog Post
Building AgentOS: My Journey Securing Sovereign AI with Auth0 Token Vault
When I saw the Authorized to Act hackathon, I immediately thought about the growing trend of sovereign local AI like OpenClaw. Developers are running powerful agents locally to maintain privacy, but they hit a hard wall when trying to reach external services safely.
AgentOS was born from that challenge — a secure intermediary that keeps OpenClaw in strict restricted mode while enabling responsible external actions through Auth0 Token Vault.
The biggest technical hurdle was ensuring no raw tokens ever touched our system. We refactored heavily to use the official Token Vault federated grant and added intelligent layers: Scope Weaver for adaptive minimal scoping and Shadow Simulator for safe what-if previews.
Adding Docker, Prometheus/Grafana, and Kubernetes manifests in the final days made the project feel genuinely production-ready. The most rewarding insight was realizing how Token Vault + OpenClaw-powered consent can bridge the gap between full trust and complete isolation in agent systems.
This hackathon taught me how critical a strong identity layer is for the future of agentic AI. I’m proud that AgentOS not only meets the Token Vault requirement but demonstrates a complete, intelligent, and secure pattern for sovereign AI agents.
Thank you to the Auth0 team for Token Vault and this inspiring hackathon.
Built With
- ai-agents
- auth0
- css3
- docker
- fastapi
- grafana
- javascript
- kubernetes
- langchain
- langraph
- next
- nextjs
- openclaw
- prometheus
- python
- render
- tailwind
- token-vault
- typescript
- vercel

Log in or sign up for Devpost to join the conversation.